Page Summary
-
Account linking connects Google accounts with user accounts in your authentication system to personalize user experiences and provide consistent cross-platform experiences.
-
Account linking uses Google Sign-In and optionally OAuth 2.0.
-
Google Sign-In is recommended for Actions targeting only Assistant and allows requesting access to the user's Google profile.
-
OAuth-based Google Sign-in "Streamlined" linking adds Google Sign-In on top of OAuth and is recommended for multi-platform Actions with existing authentication systems that need to support non-Gmail addresses.
-
OAuth linking supports standard OAuth 2.0 flows but is discouraged as it requires transferring user interaction to a screen.
You can use account linking to connect your users' Google accounts with user accounts in your authentication system. This allows you to build richer experiences for your users; for example, you can save the user's food or music preferences, history of transactions, and other information that you can use to provide a more personalized experience.
If your Action is a companion of existing apps on different platforms (for example, the web or Android), you can use account linking to securely make users' preferences available to all platforms, which ensures a consistent cross-platform experience.
Account linking for Actions on Google uses Google Sign-In, Google's secure authentication system, and optionally, OAuth 2.0 , the industry-standard protocol for authorization.
Understand the account linking flow
When Assistant matches a Google account to a user, you can use account linking to ask for the user's permission to access that Google account. You can use the account data to do the following:
- To find a match for the account in your authentication system if the user has already used your Action or one of your apps on other platforms.
- To create a new account in your authentication system for a new user.
Actions on Google offers three different account linking types.
Google Sign-In
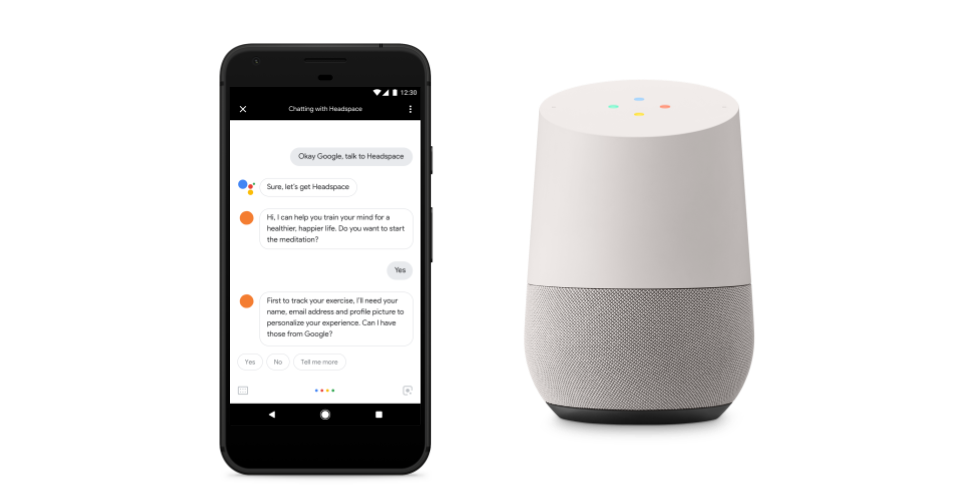
With Google Sign-In for the Assistant, your Action can request access to your user's Google profile during a conversation, including the user's name, email address, and profile picture. The user can complete the whole flow over voice, which provides a frictionless sign-in experience.
This type of account linking is recommended if any of the following applies:
- You don't have an existing authentication system.
- You have an existing authentication system and only want to link to users who signed up to your existing apps using their @gmail.com address.
To learn more, see the Google Sign-In concept guide and implementation guide.
OAuth-based Google Sign-in "Streamlined" linking
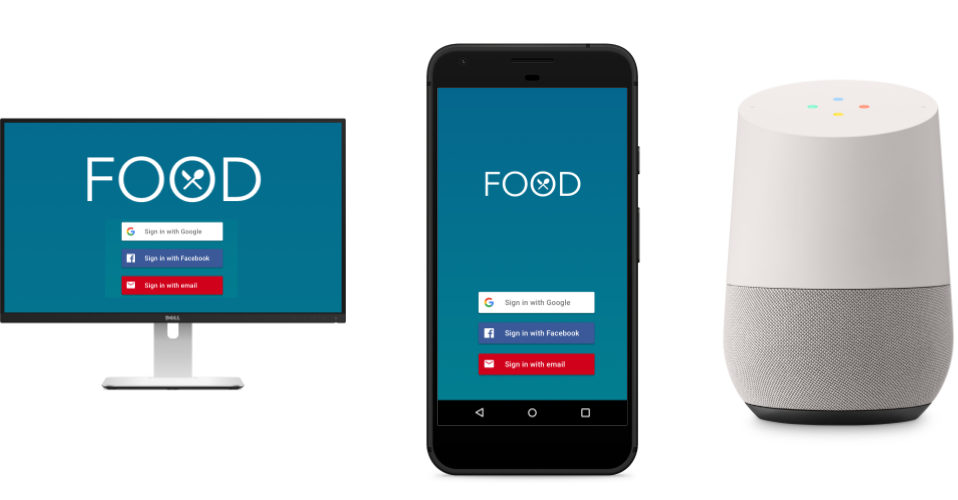
The OAuth-based Google Sign-in "Streamlined" linking type adds Google Sign-In on top of OAuth based account linking. This provides seamless voice-based linking for Google users while also enabling account linking for users who registered to your service with a non-Google identity.
To use this flow, you need to extend one of the supported OAuth 2.0 standard flows to add support for Google proprietary extensions of the protocol, which allow you to:
- Seamlessly link accounts using the Google profile information.
- Seamlessly create new accounts using the Google profile information (optional).
This type of account linking is recommended if you have an existing authentication system and you want to allow users to connect to non @gmail.com addresses.
To learn more, see the OAuth-based Google Sign-in "Streamlined" linking concept guide and implementation guide.
OAuth linking
The OAuth linking type supports two industry standard OAuth 2.0 flows, the implicit and authorization code flows.
Using this flow is discouraged because it requires transferring the user interaction from voice to screen. You can consider using this flow if you have an existing implementation of an OAuth 2.0 server, and you cannot extend the token exchange endpoint to add support for Google's protocols for automatic linking and account creation from an ID token.
To learn more, see the OAuth linking concept guide and implementation guide.
Related resources
For more information about implementing account linking in your Action, see the following resource:
- Account linking: Dialogflow: An introduction to the linking types you can implement in your Action.