認証と認可は、それぞれ ID とリソースへのアクセスを確認するために使用されるメカニズムです。このドキュメントでは、アプリで認証と認可を実装する前に知っておくべき重要な用語について説明します。
認証は、リクエストを行っているユーザーを識別します。認可は、リクエスト元がアクセスできるリソースと、そのアクセスレベルを特定します。認証は認可の前提条件です。リクエスト元の ID を確立しないと、アクセスするリソースを特定できません。詳細な定義については、重要な用語のセクションをご覧ください。
ホテル予約の簡略化された例を考えてみましょう。ホテルに到着すると、フロントの係員が予約の確認のために身分証明書の提示を求めます。ID でホテルへの認証を行います。フロント係からホテルキーを受け取ります。このキーを使用すると、ホテルの客室、ジム、ビジネス センターなどの特定のリソースにアクセスできます。ホテルキーを使用すると、これらのリソースにアクセスできます。
プロセスの概要
次の図は、Google Workspace API の認証と認可の大まかな手順を示しています。
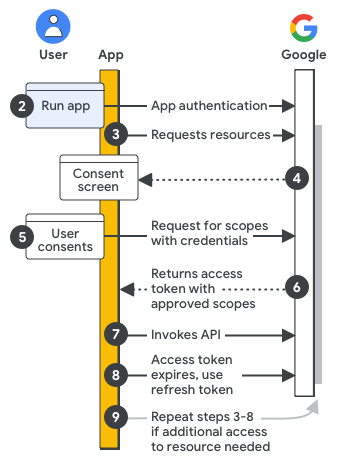
Google Cloud プロジェクトとアプリを構成する: 開発中に、Google Cloud コンソールでアプリを登録し、API キー、エンドユーザー認証情報、サービス アカウント認証情報を使用してアプリを認証するための認可スコープとアクセス認証情報を定義します。
アクセス用にアプリを認証する: アプリが実行されると、登録されたアクセス認証情報が評価されます。アプリがエンドユーザーとして認証を行う場合、ログイン プロンプトが表示されることがあります。
リソースをリクエストする: アプリで Google リソースにアクセスする必要がある場合は、事前に登録した関連するアクセス スコープを使用して Google にリクエストします。
ユーザーの同意を求める: アプリがエンドユーザーとして認証する場合、Google は OAuth 同意画面を表示します。ユーザーは、リクエストされたデータへのアクセスをアプリに許可するかどうかを決定できます。
承認されたリソースのリクエストを送信する: ユーザーがアクセス スコープに同意すると、アプリは認証情報とユーザーが承認したアクセス スコープをリクエストにバンドルします。リクエストは、アクセス トークンを取得するために Google 認証サーバーに送信されます。
Google がアクセス トークンを返す: アクセス トークンには、付与されたアクセス スコープのリストが含まれています。返されたスコープのリストがリクエストされたアクセス スコープよりも制限されている場合、アプリはトークンによって制限されている機能を無効にします。
リクエストされたリソースにアクセスする: アプリは Google からのアクセス トークンを使用して、関連する API を呼び出し、リソースにアクセスします。
更新トークンを取得する(省略可): アプリで 1 つのアクセス トークンの有効期間を超えて Google API にアクセスする必要がある場合は、更新トークンを取得できます。
リソースの追加をリクエストする: 追加のアクセスが必要な場合、アプリはユーザーに新しいアクセス スコープの付与を求め、アクセス トークンを取得するための新しいリクエスト(ステップ 3 ~ 6)を生成します。
重要な用語
認証と認可に関連する用語は次のとおりです。
- 認証
ユーザーまたはユーザーに代わって動作するアプリであるプリンシパルが、そのユーザーまたはアプリであることを確認する行為。Google Workspace アプリを作成する際は、次の認証タイプに注意する必要があります。
- ユーザー認証
- ユーザーがアプリに対して認証(ログイン)を行う行為。通常、ユーザー認証は、ユーザーがユーザー名とパスワードの組み合わせを使用してアプリに対して身元を確認するログイン プロセスを通じて行われます。ユーザー認証は、Google でログインを使用してアプリに組み込むことができます。
- アプリの認証
- アプリを実行しているユーザーに代わって、アプリが Google サービスに直接認証を行うこと。アプリ認証は通常、アプリのコードで事前に作成された認証情報を使用して行われます。
- 認可
プリンシパルがデータにアクセスしたり、オペレーションを実行したりするために必要な権限または「権限」。アプリは、ユーザーに代わって操作を行うことをユーザーに通知することで、承認をリクエストします。ユーザーがリクエストを許可すると、アプリは独自の認証情報を使用して Google からアクセス トークンを取得します。
- Credential
ソフトウェア セキュリティで使用される識別形式。認証の観点から見ると、認証情報はユーザー名とパスワードの組み合わせであることがよくあります。Google Workspace API の承認に関して、認証情報は通常、アプリ デベロッパーと認証サーバーの間でのみ認識される一意のシークレット文字列など、何らかの形式の識別情報です。Google は、API キー、OAuth 2.0 クライアント ID、サービス アカウントの認証情報をサポートしています。
- API キー
- Maps API を使用して提供されるデータなど、一般公開データへのアクセスをリクエストするために使用される認証情報。「このリンクを知っているインターネット上のすべてのユーザー」の設定を使用して共有された一般公開の Google Workspace ファイルにも、この方法でアクセスできますが、ほとんどの Google Workspace データには OAuth 2.0 が必要です。
- OAuth 2 クライアント ID
- ユーザー所有のデータへのアクセスをリクエストするために使用される認証情報。これは、Google Workspace API を使用してデータへのアクセスをリクエストする際に使用される主要な認証情報です。この認証情報にはユーザーの同意が必要です。
- クライアント シークレット
- アプリケーションと認可サーバーのみが知っている文字列。クライアント シークレットは、承認されたリクエスタにのみトークンを付与することで、ユーザーのデータを保護します。暗号化されていないクライアント シークレットをアプリに含めることは絶対にしないでください。クライアント シークレットは安全に保存することをおすすめします。詳細については、クライアント認証情報を安全に処理するをご覧ください。
- サービス アカウント キー
- サービス アカウントが Google サービスへの認可を取得するために使用します。
- サービス アカウント
- サーバー間のやり取りに使用される認証情報。たとえば、プロセスとして実行され、データへのアクセスやオペレーションの実行を行うユーザー インターフェースのないアプリケーションなどです。サービス アカウントは通常、クラウドベースのデータとオペレーションへのアクセスに使用されます。ただし、ドメイン全体の権限の委任と組み合わせて使用すると、ユーザーデータにアクセスできます。
- スコープ
アプリに付与されるリソースまたはアクションへのアクセスレベルを定義する OAuth 2.0 URI 文字列。Google Workspace の場合、認可スコープ URI には、Google Workspace アプリの名前、アクセスするデータの種類、アクセスレベルが含まれます。アプリのユーザーは、リクエストされたスコープを確認して、付与するアクセス権を選択できます。その後、Google の認証サーバーが、許可されたスコープをアクセス トークンとしてアプリに返します。詳しくは、アプリのスコープを選択する方法をご覧ください。
- 認可サーバー
アクセス トークンを使用して、アプリがリクエストしたデータとオペレーションへのアクセスを許可する Google のサーバー。
- 認証コード
アクセス トークンの取得に使用される、認可サーバーから送信されたコード。コードが必要になるのは、アプリケーション タイプがウェブ サーバー アプリまたはインストール済みのアプリの場合のみです。
- アクセス トークン
Google Workspace API へのアクセス権を付与するトークン。単一のアクセス トークンで、複数の API へのさまざまなレベルのアクセス権(スコープ)を付与できます。アプリの認証コードはアクセス トークンをリクエストし、それを使用して Google Workspace API を呼び出します。
- リソース サーバー
アプリが呼び出す API をホストするサーバー。
- OAuth 2.0 フレームワーク
アプリが「安全なアクセス権の委任」またはアプリのユーザーに代わってデータとオペレーションにアクセスするために使用できる標準。アプリで使用する認証メカニズムと認可メカニズムは、OAuth 2.0 フレームワークの実装を表します。
- プリンシパル
リソースへのアクセス権を付与できるエンティティ(ID とも呼ばれます)。Google Workspace APIs では、ユーザー アカウントとサービス アカウントの 2 種類のプリンシパルをサポートします。詳細については、プリンシパルをご覧ください。
- データの種類
認証と認可のコンテキストでは、データ型は、アプリがアクセスしようとしているデータを所有するエンティティを指します。データ型には次の 3 つがあります。
- パブリック ドメインのデータ
- Google マップのデータなど、誰でもアクセスできるデータ。このデータには通常、API キーを使用してアクセスします。
- エンドユーザー データ
- 特定のユーザーまたはグループに属するデータ(特定のユーザーの Google ドライブ ファイルなど)。通常、このデータ型には OAuth 2 クライアント ID またはサービス アカウントを使用してアクセスします。
- クラウドデータ
- Google Cloud プロジェクトが所有するデータ。通常、このデータ型にはサービス アカウントからアクセスします。
- ユーザーの同意
アプリのユーザーがアプリにデータへのアクセスとユーザーに代わって操作を行うことを承認する必要がある承認ステップ。
- アプリケーション タイプ
作成するアプリのタイプ。Google Cloud コンソールを使用して認証情報を作成する際に、アプリケーション タイプを選択するよう求められます。アプリケーション タイプは、ウェブ アプリケーション(JavaScript)、Android、Chrome 拡張機能、iOS、テレビと入力制限付きデバイス、デスクトップ アプリ(「インストール済みアプリ」とも呼ばれます)です。
- サービス アカウント
データにアクセスして認証を受ける必要がある人間以外のユーザーを表す特別なタイプの Google アカウント。アプリケーションは Google API の呼び出しにサービス アカウントの ID を使用するため、ユーザーは直接関与しません。サービス アカウント自体は、Google Workspace API を使用して通常アクセスされるユーザーデータにアクセスするために使用することはできません。ただし、サービス アカウントはドメイン全体の権限の委任を実装することでユーザーデータにアクセスできます。詳細については、サービス アカウントについてをご覧ください。
- ドメイン全体の権限の委任
Google Workspace 組織のユーザーに代わってユーザーデータにアクセスするアプリケーションを承認できる管理機能。ドメイン全体の委任は、ユーザーデータに対して管理者関連のタスクを実行するために使用できます。このような権限の委任を行うには、Google Workspace 管理者が OAuth 2.0 のサービス アカウントを使用します。この機能の強力さから、権限のドメイン全体の委任を有効にできるのは特権管理者のみです。詳しくは、ドメイン全体の権限をサービス アカウントに委任するをご覧ください。
次のステップ
アプリの OAuth 同意画面を構成して、ユーザーがアプリによるデータへのアクセスを理解して承認できるようにします。
