Questa pagina riassume tutte le modifiche (nuove funzionalità, correzioni di bug, aggiornamenti) apportate all'API Android Management e ad Android Device Policy ogni mese.
Iscriviti alla mailing list dell'API Android Management per ricevere aggiornamenti mensili e avvisi di servizio direttamente nella tua casella di posta.
Gestione dei dispositivi XR
API Android Management
- AMAPI ora supporta Android XR. Scopri di più sulla gestione dei dispositivi XR.
Marzo 2026
API Android Management
-
Come documentato
a ottobre 2025 e comunicato nel seguente
annuncio del servizio, il valore predefinito per il criterio
enterpriseDisplayNameVisibilityora èENTERPRISE_DISPLAY_NAME_VISIBLE. Questo criterio controlla se ilenterpriseDisplayNameviene mostrato sui dispositivi, ad esempio sulla schermata di blocco dei dispositivi di proprietà dell'azienda. Per nascondere il nome dell'azienda, imposta esplicitamente la policy suENTERPRISE_DISPLAY_NAME_HIDDEN. - La configurazione EAP all'interno di Configurazione di rete aperta è stata aggiornata, aggiungendo il supporto di EAP-PWD come metodo EAP esterno. Consulta la documentazione per l'elenco completo delle funzionalità supportate.
- Abbiamo aggiornato la documentazione per:
-
networkResetDisabledper chiarire che questo criterio si applica solo ai dispositivi completamente gestiti. -
installType.KIOSKeRoleType.KIOSKper chiarire che su Android 11 e versioni successive il controllo utente non è consentito per tutte le app. -
screenCaptureDisabledepersonalUsagePolicies.screenCaptureDisabledper menzionare che questa impostazione blocca anche Cerchia e Cerca.
-
Febbraio 2026
API Android Management
-
Sui dispositivi di proprietà aziendale con Android 10 e versioni successive, gli amministratori IT ora possono
gestire il DNS privato utilizzando il nuovo
privateDnsSettingsnel campoPolicy.DeviceConnectivityManagement. Le modalità disponibili inPrivateDnsSettings.privateDnsModeincludono: scelta dell'utente, automatica e host specificato (solo dispositivi completamente gestiti). - AMAPI ora supporta un'anteprima dell'integrazione con il Model Context Protocol (MCP). Ciò fornisce le basi per consentire agli EMM di creare interfacce conversazionali basate sull'AI utilizzando strumenti di sola lettura. Per ulteriori dettagli, consulta la documentazione.
-
È stata aggiornata
la documentazione di
NetworkInfo.TelephonyInfoper chiarire il supporto per i vari tipi di dispositivi:- Le informazioni generali sulla telefonia sono disponibili per tutte le schede SIM sui dispositivi completamente gestiti (Android 6 e versioni successive).
- Per le eSIM aggiunte dall'amministratore, le informazioni sulla telefonia sono disponibili in tutte le modalità di gestione su Android 15 e versioni successive.
-
I campi
activationStateeconfigModesono applicabili solo alle eSIM sui dispositivi con Android 15 e versioni successive.
Gennaio 2026
API Android Management
-
Abbiamo aggiunto una nuova norma per controllare l'aggiunta di eSIM avviata dall'utente. Il campo
userInitiatedAddEsimSettingsall'interno diDeviceRadioStateconsente agli amministratori di specificare se l'utente è autorizzato ad aggiungere profili eSIM sui dispositivi di proprietà aziendale con Android 15 e versioni successive. -
La documentazione del
flag
WIPE_ESIMS, utilizzato inPolicy.wipeDataFlagseDeleteDeviceRequest.wipeDataFlags, è stata aggiornata per chiarire che per i dispositivi con Android 16 o versioni successive, le eSIM gestite vengono sempre cancellate quando un profilo di lavoro viene rimosso da un dispositivo di proprietà personale, indipendentemente dall'impostazione di questo flag. - È stata rilasciata la versione 1.7.1 dell'SDK AMAPI. Questa versione aggiunge log più dettagliati per le API degli indicatori di fiducia del dispositivo per facilitare la diagnosi dei problemi. Per maggiori dettagli, consulta le note di rilascio dell'SDK Android Management.
- I Termini di servizio dell'API AMAPI sono stati aggiornati per includere esplicitamente l'SDK AMAPI e per aggiungere alla definizione di "Clienti" i produttori di apparecchiature originali (OEM) di dispositivi Android.
-
Le linee guida per l'utilizzo consentito ora vietano specificamente l'utilizzo di
Advertising IDper accedere agli indicatori Device Trust.
Novembre 2025
API Android Management
- A partire dal 1° novembre 2025, la registrazione dei dispositivi tramite l'API Android Management richiede la registrazione e l'approvazione di Android Enterprise. Gli sviluppatori possono avviare questa procedura compilando il modulo di richiesta.
-
La documentazione relativa al valore
CUSTOMinApplicationPolicy.InstallTypeè stata aggiornata per chiarirne l'utilizzo. Sono inclusi maggiori dettagli sui requisiti perApplicationPolicy.signingKeyCertse sul comportamento previsto quando si modificainstallTypedi un'applicazione inCUSTOMo viceversa. -
Le descrizioni delle norme esistenti
setUserIconDisabledeshareLocationDisabledsono state perfezionate per una maggiore chiarezza.
SDK API Android Management
-
La versione 1.7.0 dell'SDK AMAPI è stata rilasciata a novembre. Questa release dell'SDK
include il supporto per il
comando
REQUEST_DEVICE_INFO. Per informazioni dettagliate, consulta le note di rilascio dell'SDK AMAPI.
Ottobre 2025
API Android Management
- Abbiamo aggiunto una nuova norma per gestire le applicazioni predefinite sui dispositivi. Gli amministratori possono configurare un elenco di applicazioni con priorità per ogni tipo di app e l'app qualificata e installata per prima sul dispositivo verrà impostata come predefinita. Una volta configurato, questo criterio impedisce agli utenti di modificare le impostazioni predefinite dell'applicazione, mantenendo la conformità alle norme aziendali. Per ulteriori dettagli, consulta questa guida.
-
A maggio abbiamo introdotto una policy per configurare l'impostazione
enterpriseDisplayNameVisibility, consentendo agli amministratori di controllare la visibilità dell'impostazioneenterpriseDisplayNamesul dispositivo, ad esempio nella schermata di blocco dei dispositivi di proprietà dell'azienda. In quell'annuncio abbiamo menzionato che a breve imposteremo il valore predefinito di questa impostazione dei criteri suENTERPRISE_DISPLAY_NAME_VISIBLE. Questa modifica dovrebbe essere applicata a gennaio 2026. - Sono stati aggiornati anche gli elementi della documentazione:
-
Abbiamo chiarito il comportamento del comando
LOCKsui dispositivi con profili di lavoro. -
Abbiamo aggiunto informazioni su
nonComplianceDetailsper le modifiche all'mte_policysui dispositivi in attesa di riavvio.
-
Abbiamo chiarito il comportamento del comando
Settembre 2025
API Android Management
-
Abbiamo introdotto il concetto di
ruoli dell'applicazione. Sono compresi:
-
COMPANION_APPper l'interazione offline con Android Device Policy -
KIOSKper esperienze con dispositivi dedicati da utilizzare con app che hannoInstallTypeconfigurato comeREQUIRED_FOR_SETUPoCUSTOM -
MOBILE_THREAT_DEFENSE_ENDPOINT_DETECTION_RESPONSE(MTD/EDR) eSYSTEM_HEALTH_MONITORING.
ApplicationPolicy.roleseRoleType. -
- Sono disponibili una nuova release stabile e un candidato per la release dell'SDK AMAPI. Consulta le note di rilascio per i dettagli su cosa è incluso in queste versioni.
Agosto 2025
API Android Management
-
Ora supportiamo l'installazione di applicazioni utilizzando l'SDK AMAPI
1.6.0-rc01 e versioni successive. Per installare un'applicazione, aggiungila a
application policyconinstallTypeCUSTOMe i certificati della chiave di firma dell'applicazione sono specificati nell'elencosigningKeyCerts. Utilizzando l'SDK AMAPI, esegui i comandiinstallCustomAppeuninstallCustomAppper installare e disinstallare le applicazioni personalizzate. Per ulteriori dettagli, consulta la documentazione. -
Abbiamo aggiunto
ApplicationPolicy.signingKeyCertsin sostituzione dell'utilizzo diExtensionConfig.signingKeyFingerprintsSha256, che ora è deprecato.ApplicationPolicy.signingKeyCertsdeve essere impostato quando l'app hainstallTypeimpostato suCUSTOM(ovvero un'app personalizzata) o quando l'app haextensionConfigimpostato (ovvero un'app di estensione) e non è presente sul Play Store. Per ulteriori dettagli, consulta la documentazione. -
Per l'SDK AMAPI, abbiamo rilasciato:
- Una release stabile aggiornata v1.5.0
- Una nuova release candidate v1.6.0-rc01 che introduce la funzionalità per gestire le app personalizzate.
Luglio 2025
API Android Management
-
Abbiamo aggiornato
PasswordRequirementsper consentire requisiti basati sulla complessità nell'ambito del profilo di lavoro. È stata pubblicata una nuova guida per spiegare l'interazione tra le impostazioni delle password basate sulla complessità e quelle non basate sulla complessità.
Giugno 2025
API Android Management
-
Per Android 16 e versioni successive, gli amministratori IT possono ora utilizzare l'impostazione dei criteri
appFunctionsper controllare se le app sul dispositivo per i dispositivi completamente gestiti o nel profilo di lavoro per i dispositivi con profili di lavoro possono esporre le funzioni delle app.crossProfileAppFunctionspuò essere utilizzato per controllare se le app del profilo personale possono richiamare le funzioni delle app esposte dalle app nel profilo di lavoro. -
Abbiamo aggiunto all'API Android Management due nuovi metodi:
modifyPolicyApplicationseremovePolicyApplications. Questi metodi consentono di creare, aggiornare e rimuovere sottoinsiemi di applicazioni nel campo Applicazioni dei criteri, senza dover recuperare e fornire apolicies.patchtutte le applicazioni che rimangono invariate. -
È stato introdotto un nuovo comando
WIPEcome alternativa adevices.delete, che può essere attivato utilizzandodevices.issueCommand. Questo metodo attiva il ripristino dei dati di fabbrica dei dispositivi di proprietà dell'azienda e l'eliminazione del profilo di lavoro dei dispositivi personali. Dopo la cancellazione o l'eliminazione, verrà eliminato anche il record del dispositivo.
Abbiamo pubblicato una nuova guida per spiegare i vari metodi per eseguire il deprovisioning di un dispositivo. -
Abbiamo aggiornato l'SDK API Android Management (AMAPI SDK) per includere l'indicatore
Device.WorkProfileStateper identificare lo stato di gestione del dispositivo.
Per ulteriori dettagli, consulta le note di rilascio dell'SDK AMAPI.
Maggio 2025
API Android Management
-
Abbiamo aggiunto una nuova limitazione delle norme
apnPolicyperDeviceConnectivityManagementper consentire agli amministratori IT di configurare i nomi dei punti di accesso (APN) sui dispositivi. Gli APN applicati dal criterio avranno la precedenza su tutti gli altri APN configurati dagli utenti. -
È stata implementata una nuova limitazione delle norme
preferentialNetworkServiceSettingsinDeviceConnectivityManagementper consentire agli amministratori IT di configurare le reti preferenziali. Il campopreferentialNetworkIdnella applicazione può essere utilizzato per scegliere una rete preferenziale per ogni singola applicazione. Per ulteriori informazioni, consulta la nostra guida al network slicing 5G e la documentazione AOSP sul network slicing 5G. - Questa release offre agli amministratori IT una gestione delle eSIM migliorata, consentendo loro di aggiungere, rimuovere e visualizzare le eSIM gestite su tutti i dispositivi. Da ora in poi, gli amministratori possono definire policy per le eSIM gestite, specificando il loro comportamento se un dispositivo viene cancellato o se un profilo di lavoro non è conforme, garantendo il controllo e la conformità alle policy dell'organizzazione.
-
La nuova impostazione dei criteri
enterpriseDisplayNameVisibilityconsente agli amministratori di controllare la visibilità delenterpriseDisplayNamesul dispositivo, ad esempio nella schermata di blocco dei dispositivi di proprietà dell'azienda. Anche se ora per impostazione predefinita viene visualizzato il nome dell'azienda configurato durante la configurazione iniziale del dispositivo, questa impostazione cambierà tra sei mesi (novembre 2025), dopodiché l'impostazione predefinita saràENTERPRISE_DISPLAY_NAME_VISIBLE.
Aprile 2025
API Android Management
-
Abbiamo aggiunto una nuova limitazione dei criteri
bluetoothSharingaPersonalUsagePolicieseDeviceConnectivityManagementper consentire agli amministratori IT di autorizzare o vietare la condivisione di file tramite Bluetooth. -
Un nuovo
evento di log di sicurezza viene generato e notificato utilizzando la notifica Pub/Sub
nell'API AMAPI quando il campo
BackupServiceStateviene attivato o disattivato dall'amministratore. -
Abbiamo aggiunto un nuovo campo
EuiccChipInfoinHardwareInfoper leggere l'EID per i dispositivi di proprietà aziendale ed è stato aggiunto un nuovo comandoREQUEST_DEVICE_INFOper leggere l'EID dai dispositivi di proprietà personale. - Sono stati aggiornati anche gli elementi della documentazione:
- Abbiamo aggiornato l'SDK API Android Management (SDK AMAPI) per includere la versione stabile di Device Trust di Android Enterprise. Le note di rilascio sono disponibili all'indirizzo https://developers.google.com/android/management/sdk-release-notes
Marzo 2025
API Android Management
- La risorsa Enterprise ora include maggiori dettagli nel campo tipo di enterprise. Specificano se l'azienda utilizza account Google Play gestiti (e se sono di proprietà del cliente o dell'EMM) o se si tratta di un dominio Google gestito (con verifica DNS o un team con indirizzo email verificato). Queste informazioni aiutano i provider EMM a prepararsi per una funzionalità imminente che consente alle aziende di eseguire l'upgrade dagli account Google Play gestiti ai domini Google gestiti, consentendo loro di adattare la console di amministrazione IT in base al tipo di azienda.
Febbraio 2025
API Android Management
- Abbiamo aggiunto la guida su come rilevare i profili di lavoro gestiti dall'app Android Device Policy.
- Abbiamo aggiornato l'SDK API Android Management (AMAPI SDK) per includere il primo candidato per la release per le API degli indicatori di fiducia del dispositivo. Consulta le note di rilascio dell'SDK AMAPI per conoscere l'ultima versione disponibile.
Gennaio 2025
API Android Management
- Gli EMM ora possono limitare la registrazione dell'amministratore IT tramite un'email proveniente da una lista consentita di nomi di dominio.
- Sono stati aggiornati anche gli elementi della documentazione:
- La guida alle app web è stata aggiornata per chiarire in che modo il browser predefinito scelto dall'utente interagisce con le impostazioni di visualizzazione come la modalità a schermo intero o l'interfaccia utente minima. Il browser potrebbe supportare o meno questi attributi. Gli amministratori IT sono responsabili del test della compatibilità del browser con le impostazioni dell'app web prima di eseguirne il deployment per gli utenti.
Dicembre 2024
API Android Management
-
Per Android 15 e versioni successive, gli amministratori IT possono ora utilizzare
privateSpacePolicyper consentire o impedire la creazione di uno spazio privato. -
Per Android 15 e versioni successive, abbiamo introdotto
WifiRoamingModeinWifiRoamingPolicy, consentendo agli amministratori IT di disattivare il roaming Wi-Fi per SSID specifici su dispositivi completamente gestiti e su profili di lavoro su dispositivi di proprietà dell'azienda. - Sono stati aggiornati vari elementi della nostra documentazione:
-
La descrizione del campo
keyguardDisableora include informazioni sulla modalità di gestione. -
La documentazione dell'
securityPostureora include una tabella che mostra l'esito equivalente dell'API Play Integrity per ogni esito dell'API AM.
-
La descrizione del campo
Novembre 2024
API Android Management
-
Ora impediamo agli utenti di modificare il proprio indirizzo email durante la registrazione dei clienti. Abbiamo anche introdotto la convalida per
admin_emaildurante la creazione di un URL di registrazione. - Sono stati aggiornati vari elementi della nostra documentazione:
-
Abbiamo aggiornato la descrizione delle norme relative a
addUserDisabled. Per i dispositivi in cuimanagementModeèDEVICE_OWNERquesto campo viene ignorato e all'utente non è mai consentito aggiungere o rimuovere utenti. -
Abbiamo aggiornato le
ExtensionConfigper chiarire che l'esenzione dalle limitazioni della batteria si applica ad Android 11 e versioni successive. -
Abbiamo aggiornato la descrizione di
PermissionPolicy. -
Abbiamo chiarito a quante applicazioni può essere delegato un ambito nell'enum
DelegatedScope.
-
Abbiamo aggiornato la descrizione delle norme relative a
Ottobre 2024
API Android Management
- Abbiamo aggiornato il comportamento delle norme
CommonCriteriaMode.
COMMON_CRITERIA_MODE_ENABLEDora attiverà il controllo dell'integrità dei criteri di crittografia e l'ulteriore convalida del certificato di rete. Il risultato del controllo dell'integrità del criterio è impostato suPolicySignatureVerificationStatussestatusReportingSettings.commonCriteriaModeEnabledè impostato sutrue.
Non sono state apportate modifiche al comportamento del valore predefinito (COMMON_CRITERIA_MODE_UNSPECIFIED) o quando viene disattivato esplicitamente conCOMMON_CRITERIA_MODE_DISABLED. - Abbiamo aggiornato la documentazione per
PERSONAL_USAGE_DISALLOWED_USERLESSper ricordare agli sviluppatori che questa modifica è necessaria prima di gennaio 2025. Se questa modifica viene omessa, gli utenti potrebbero visualizzare un prompt "Esegui l'autenticazione con Google" durante la registrazione, quando l'amministratore IT ha attivato questa funzionalità.
La cronologia completa di questa funzionalità è pubblicata sul portale partner di Android Enterprise: Cronologia delle funzionalità: flusso di registrazione, registrazione dei dispositivi ed esperienze sui dispositivi migliorati. - Abbiamo aggiornato la documentazione per
CrossProfileDataSharingper includere i dettagli della condivisione semplice dei dati tramite intent.
Settembre 2024
API Android Management
L'API Android Management ora supporta le seguenti funzionalità di Android 15:
- Per Android 15 e versioni successive è stata aggiunta una nuova norma per controllare le impostazioni di roaming Wi-Fi. Gli amministratori IT possono utilizzare
WifiRoamingPolicyper selezionareWifiRoamingModedesiderato. Supportato su dispositivi completamente gestiti e profili di lavoro su dispositivi di proprietà dell'azienda.
Release di Android 15
API Android Management
L'API Android Management ora supporta le seguenti funzionalità di Android 15:
- Android 15 introduce nuovi criteri per controllare
Cerchia e Cerca. Gli amministratori IT possono utilizzare
AssistContentPolicyper controllare questa funzionalità. - Android 15 introduce nuove norme per controllare il rilevamento del phishing delle app.
Gli amministratori IT possono utilizzare
ContentProtectionPolicyper controllare se l'app viene scansionata da On Device Abuse Detection (ODAD) per rilevare malware di phishing. - Android 15 estende il supporto delle impostazioni di
luminosità dello schermo e
spegnimento dello schermo utilizzando il criterio
DisplaySettingsai dispositivi di proprietà aziendale con un profilo di lavoro. In precedenza, questa impostazione era disponibile solo sui dispositivi completamente gestiti.
Agosto 2024
API Android Management
- Su Android 13 e versioni successive, gli amministratori IT possono ora eseguire query sul
ICCIDassociato alla scheda SIM delTelephonyInfoincluso in unNetworkInfo. Questa operazione è supportata sui dispositivi completamente gestiti quando il camponetworkInfoEnabledinstatusReportingSettingsè impostato sutrue. - Sono stati aggiornati vari elementi della nostra documentazione:
- Abbiamo aggiornato la documentazione per la modalità Common Criteria per chiarire che è supportata solo sui dispositivi di proprietà aziendale con Android 11 o versioni successive.
- Abbiamo documentato il campo facoltativo
DefaultStatusinSigninDetail.
Luglio 2024
API Android Management
- Sono stati aggiornati vari elementi della nostra documentazione:
- Abbiamo rimosso la nota nella documentazione di
enrollmentToket.createrelativa all'impossibilità di recuperare i contenuti del token, in quanto è possibile ottenere il valore del token di registrazione utilizzandoenrollmentTokens.get. - Abbiamo chiarito la
documentazione
NonComplianceReason.
- Abbiamo rimosso la nota nella documentazione di
Giugno 2024
API Android Management
- Gli amministratori IT ora possono controllare le impostazioni di
luminosità dello schermo e
spegnimento dello schermo utilizzando il criterio
DisplaySettings. Funzionalità supportata sui dispositivi completamente gestiti con Android 9 e versioni successive. - Abbiamo aggiornato la nostra documentazione per spiegare che, anche quando si utilizza
AUTO_UPDATE_HIGH_PRIORITY, gli aggiornamenti delle app con implementazioni più grandi nell'ecosistema Android possono richiedere fino a 24 ore. - Abbiamo aggiornato l'SDK API Android Management (AMAPI SDK) per spiegare
i diversi casi d'uso ora supportati da questa libreria (originariamente nota come
SDK di estensibilità). La documentazione aggiornata riguarda:
Consulta le note di rilascio dell'SDK AMAPI per conoscere l'ultima versione disponibile.
Maggio 2024
API Android Management
- I metodi
getelistperenrollmentTokensora restituiscono i campivalue,qrCodeeallowPersonalUsagecompilati. - Per i dispositivi completamente gestiti, l'impostazione
AllowPersonalUsageora supportaPERSONAL_USAGE_DISALLOWED_USERLESS. - Su Android 11 e versioni successive, la nuova policy
UserControlSettingsconsente di specificare se il controllo utente è consentito per una determinata app.UserControlSettingsinclude azioni utente come l'interruzione forzata e la cancellazione dei dati dell'app. - La versione 1.1.5 dell'SDK AMAPI è ora disponibile. Ulteriori
informazioni sono disponibili nella
pagina delle note di rilascio.
Nota:ti consigliamo vivamente di utilizzare sempre l'ultima versione disponibile della libreria per usufruire delle correzioni di bug e dei miglioramenti disponibili.
Aprile 2024
API Android Management
- Su Android 13 e versioni successive, per i dispositivi di proprietà aziendale, abbiamo aggiunto controlli su
a quali SSID Wi-Fi possono connettersi i dispositivi. Utilizzando
WifiSsidPolicy, gli amministratori IT possono specificare un elenco di SSID da aggiungere a una lista consentita (WIFI_SSID_ALLOWLIST) o a una lista bloccata (WIFI_SSID_DENYLIST). - Per i dispositivi di proprietà aziendale, abbiamo aggiunto identificatori hardware (IMEI,
MEID e numero di serie) a
ProvisioningInfoa cui gli EMM possono ora accedere durante la configurazione del dispositivo utilizzando l'URL di accesso.
Marzo 2024
API Android Management
- Abbiamo aggiunto controlli aggiuntivi sull'installazione delle app utilizzando
InstallConstraint, gli amministratori IT possono limitare l'installazione delle app in base a criteri specifici.
ImpostandoinstallPriority, gli amministratori IT possono assicurarsi che le app critiche vengano installate per prime. - Su Android 10 e versioni successive, AMAPI supporta la configurazione di reti aziendali a 192 bit
in
openNetworkConfiguration
passando il valore di sicurezza WPA3-Enterprise_192.
Su Android 13 e versioni successive, nella normaMinimumWifiSecurityLevelora supportiamoENTERPRISE_BIT192_NETWORK_SECURITY, che può essere utilizzato per garantire che i dispositivi non si connettano a reti Wi-Fi al di sotto di questo livello di sicurezza. - Abbiamo aggiornato l'impostazione
UsbDataAccessin modo che il valoreUSB_DATA_ACCESS_UNSPECIFIEDsia impostato per impostazione predefinita suDISALLOW_USB_FILE_TRANSFER.
Febbraio 2024
API Android Management
- Su Android 9 e versioni successive, gli amministratori IT ora possono controllare se la stampa è consentita
utilizzando il campo
printingPolicy. - Per Android 14 e versioni successive, è stata aggiunta una nuova norma per controllare
le app CredentialProvider. Gli amministratori IT possono utilizzare il campo
credentialProviderPolicyper controllare se l'app può fungere da provider di credenziali. - È stato aggiunto un nuovo criterio per controllare
Arm Memory Tagging Extension (MTE) sul dispositivo. Il campo
MtePolicyè supportato sui dispositivi completamente gestiti e sui profili di lavoro sui dispositivi di proprietà dell'azienda con Android 14 e versioni successive. - Abbiamo aggiornato la modalità di ricezione degli errori correlati alle installazioni
attivate dagli amministratori IT da parte dell'API AM. A seguito di questa migrazione, il campo
InstallationFailureReasonora include anche gli errori del client (oltre a quelli del server). - Per Android 12 e versioni successive, gli amministratori IT possono utilizzare una coppia di chiavi installata sul dispositivo
per l'autenticazione Wi-Fi aziendale. Per ulteriori informazioni, consulta il nuovo campo
ClientCertKeyPairAliasin Open Network Configuration (ONC) e la nostra guida alla configurazione di rete.
Gennaio 2024
API Android Management
- I dispositivi gestiti dal tuo DPC personalizzato ora possono essere migrati senza problemi per utilizzare l'API Android Management.
Dicembre 2023
API Android Management
- Aggiunto
MinimumWifiSecurityLevelper definire i diversi livelli di sicurezza minimi richiesti per connettersi a reti Wi-Fi. Supportato sui dispositivi completamente gestiti e sui profili di lavoro sui dispositivi di proprietà aziendale con Android 13 e versioni successive.
Novembre 2023
API Android Management
- Android 12 e versioni successive ora supportano la configurazione della rete Wi-Fi aziendale senza password utilizzando i campi
IdentityePasswordin Configurazione di rete aperta. Questa funzionalità era già supportata prima di Android 12.Nota:su Android 12 e versioni successive, per le reti Wi-Fi con autenticazione nome utente/password EAP, se la password utente non viene fornita e
AutoConnectè impostato sutrue, il dispositivo potrebbe tentare di connettersi alla rete con una password segnaposto generata casualmente. Per evitare questo problema quando la password dell'utente non viene fornita, impostaAutoConnectsufalse. - Gli eventi del dispositivo locale che si verificano in rapida successione vengono raggruppati e
segnalati in un unico
messaggio Pub/Sub agli EMM.
1Tipo di evento Latenza prevista tra l'evento sul dispositivo e la notifica EMM corrispondente1 Comportamento precedente Nuovo comportamento Priorità elevata Stati delle app con chiave Immediato, al massimo una segnalazione al minuto Immediato, al massimo una segnalazione al minuto Priorità standard Stati delle app con chiave Basato sulla pianificazione Entro un minuto Eventi correlati alle applicazioni durante il provisioning, per le app con stati di installazione definiti dall'amministratore IT2 Integrato in altri eventi correlati al provisioning Entro un minuto in aggiunta ad altri eventi di provisioning correlati Eventi relativi alle applicazioni dopo il provisioning, per le app con stati di installazione definiti dall'amministratore IT2 Basato sulla pianificazione Entro 5 minuti Eventi correlati alle applicazioni durante e dopo il provisioning, per le app con stati di installazione definiti dal dipendente3 Basato sulla pianificazione Entro 60 minuti Altri eventi delle app sul dispositivo Basato sulla pianificazione Entro 60 minuti Obiettivi basati sul massimo impegno in base a circostanze controllate. La latenza effettiva può variare in base a una serie di fattori ambientali e del dispositivo.
2InstallTypedelle app applicate nei criteri:FORCE_INSTALLED,BLOCKED,REQUIRED_FOR_SETUP,PREINSTALLEDeKIOSK.
3InstallTypedelle app disponibili:AVAILABLE,INSTALL_TYPE_UNSPECIFIED.
Ottobre 2023
API Android Management
- Le app lanciate come
SetupActionora possono annullare la registrazione. In questo modo verrà ripristinato un dispositivo di proprietà aziendale o verrà eliminato il profilo di lavoro su un dispositivo di proprietà personale.
Release di Android 14
API Android Management
Con il rilascio di Android 14, l'API Android Management ora supporta le seguenti funzionalità di Android 14:
- Limitazione dell'accesso ai contatti del profilo di lavoro
alle applicazioni di sistema e alle app personali specificate in
exemptionsToShowWorkContactsInPersonalProfile. Ora l'accesso ai contatti del profilo di lavoro può essere attivato per tutte le app personali, per app personali selezionate o per nessuna app personale.Per comodità, la nuova opzione
SHOW_WORK_CONTACTS_IN_PERSONAL_PROFILE_DISALLOWED_EXCEPT_SYSTEMinshowWorkContactsInPersonalProfilegarantisce che le uniche app personali ad accedere ai contatti di lavoro siano le app Telefono, Messaggi e Contatti predefinite del dispositivo. In questo caso, né le app Telefono, Messaggi e Contatti configurate dall'utente né altre app personali installate dall'utente o dal sistema potranno eseguire query sui contatti di lavoro. - Disattiva l'uso della radio
a banda ultralarga sul dispositivo. Ciò può essere ottenuto utilizzando il nuovo criterio
deviceRadioState.ultraWidebandState. - Blocca l'utilizzo della rete cellulare 2G,
migliorando la sicurezza della rete. Questa opzione è offerta tramite le nuove norme
deviceRadioState.cellularTwoGState. - Android 14 introduce le
scorciatoie personalizzabili della schermata di blocco.
Il controllo amministrativo delle funzionalità della schermata di blocco, che include fotocamera, sblocco con l'impronta, sblocco con il volto e così via, è stato esteso per disattivare anche le scorciatoie della schermata di blocco utilizzando la nuova opzione
SHORTCUTS.
Settembre 2023
API Android Management
- Ora le informazioni sul dispositivo e sul provisioning possono essere recuperate facoltativamente
durante la configurazione, consentendo agli sviluppatori di creare criteri più mirati durante
la configurazione o filtrare i dispositivi in base agli attributi forniti. L'URL di accesso
ora includerà un parametro
provisioningInfoche può essere scambiato con i dettagli del dispositivo corrispondenti utilizzando il nuovo metodo provisioningInfo get. SigninDetailsora possono essere distinti l'uno dall'altro con un valoretokenTagpersonalizzabile.
Agosto 2023
API Android Management
- È stata introdotta la modalità Dispositivo smarrito per i dispositivi di proprietà aziendale. La modalità Dispositivo smarrito consente ai datori di lavoro di bloccare e proteggere da remoto un dispositivo smarrito e, facoltativamente, di visualizzare un messaggio sullo schermo del dispositivo con i dati di contatto per facilitare il recupero dell'asset.
- È stato aggiunto il supporto per la delega della selezione dei certificati, che concede a un'app
l'accesso alla selezione dei certificati KeyChain per conto delle app richiedenti.
Per ulteriori dettagli, consulta
DelegatedScope.CERT_SELECTION. - Sono state aggiunte ulteriori norme di gestione del Wi-Fi:
configureWifi- Gli amministratori ora possono disattivare l'aggiunta o la configurazione di reti Wi-Fi.wifiConfigDisabledè ora deprecato.wifiDirectSettings- Questo criterio può essere utilizzato per disattivare la configurazione di Wi-Fi Direct.tetheringSettings- Questo criterio può essere utilizzato per disattivare il tethering Wi-Fi o tutte le forme di tethering.tetheringConfigDisabledè ora deprecato.wifiState- Questo criterio può essere utilizzato per attivare/disattivare forzatamente il Wi-Fi sul dispositivo di un utente.
- La condivisione delle reti Wi-Fi configurate dall'amministratore verrà disattivata a partire da Android 13 e versioni successive
Luglio 2023
API Android Management
- Aggiunto il campo
userFacingTypeaApplicationReportper indicare se un'app è rivolta agli utenti. - È stato aggiunto il motivo specifico di mancata conformità
ONC_WIFI_INVALID_ENTERPRISE_CONFIG.
Mancata conformità con motivoINVALID_VALUEe motivo specificoONC_WIFI_INVALID_ENTERPRISE_CONFIGviene segnalato se la rete Wi-Fi aziendale non haDomainSuffixMatchimpostato. - È stata aggiunta una nuova notifica Pub/Sub
EnrollmentCompleteEvent, come tipo diUsageLogEventche viene pubblicata al termine della registrazione del dispositivo. - Aggiunta di
airplaneModeStateindeviceRadioStateper controllare lo stato attuale della modalità Aereo e se l'utente può attivarla o disattivarla. Per impostazione predefinita, l'utente può attivare o disattivare la modalità Aereo. Supportato sui dispositivi completamente gestiti e sui profili di lavoro sui dispositivi di proprietà aziendale, su Android 9 e versioni successive.
Giugno 2023
API Android Management
- È stato aggiunto il supporto per il campo
DomainSuffixMatchin Open Network Configuration per configurare le reti Wi-Fi aziendali per Android 6+. Le configurazioni Wi-Fi aziendali senzaDomainSuffixMatchsono considerate non sicure e verranno rifiutate dalla piattaforma. - È stata aggiunta
UsbDataAccessun'impostazione dei criteri che consente agli amministratori di disattivare completamente il trasferimento di dati tramite USB.usbFileTransferDisabledè ora deprecato, utilizzaUsbDataAccess.
Dicembre 2022
API Android Management
-
Le funzionalità di gestione dei widget del profilo di lavoro sono state migliorate con l'aggiunta di due nuovi campi API:
workProfileWidgetsa livello di applicazione eworkProfileWidgetsDefaulta livello di dispositivo. Questi consentono un maggiore controllo sulla possibilità che un'applicazione in esecuzione nel profilo di lavoro crei widget nel profilo genitore, ad esempio la schermata Home. Questa funzionalità non è consentita per impostazione predefinita, ma può essere impostata su consentita utilizzandoworkProfileWidgetseworkProfileWidgetsDefaulted è supportata solo per i profili di lavoro. -
Abbiamo aggiunto il supporto per impostare le impostazioni di randomizzazione dell'indirizzo MAC durante la configurazione delle reti Wi-Fi. Ora gli amministratori possono specificare se
MACAddressRandomizationModeè impostato suHardwareoAutomaticdurante la configurazione delle reti Wi-Fi, che ha effetto sui dispositivi con versione del sistema operativo Android 13 e successive ed è applicabile a tutte le modalità di gestione. Se impostato suHardware, l'indirizzo MAC di fabbrica verrà configurato per la rete Wi-Fi, mentre se impostato suAutomatic, l'indirizzo MAC sarà casuale. - Sono stati aggiornati vari elementi della nostra documentazione:
-
Understanding Security Posture è stato creato per fornire chiarezza sulle potenziali risposte delle valutazioni di
devicePostureesecurityRisk. -
autoUpdateModeè stato fornito perautoUpdatePolicycome alternativa consigliata grazie alla maggiore flessibilità della frequenza di aggiornamento. -
Abbiamo chiarito che
BlockActioneWipeActionsono limitati ai dispositivi di proprietà dell'azienda. - La pagina delle notifiche Pub/Sub è stata aggiornata per riflettere con precisione i tipi di risorse per i diversi tipi di notifiche.
- Per Android 13 e versioni successive, le app di estensione sono esenti dalle limitazioni della batteria, pertanto non verranno inserite nel bucket di standby delle app con limitazioni.
Ottobre 2022
API Android Management
- Sono stati aggiornati vari elementi della nostra documentazione:
- Ti consigliamo di avere un criterio per dispositivo, per attivare funzionalità di gestione granulare a livello di dispositivo.
- Affinché FreezePeriods funzioni come previsto, i criteri di aggiornamento di sistema non possono essere impostati come SYSTEM_UPDATE_TYPE_UNSPECIFIED..
- Sono stati forniti ulteriori suggerimenti per gli aggiornamenti dei criteri relativi alla visibilità dei passaggi della password durante il provisioning dei dispositivi di proprietà dell'azienda.
- shareLocationDisabled è supportato per i dispositivi completamente gestiti e i profili di lavoro di proprietà personale.
- Abbiamo fornito una descrizione aggiornata dell'utilizzo di enterprises.devices.delete e dei suoi effetti sulla visibilità dei dispositivi.
- La durata massima del token di registrazione è ora di 10.000 anni, mentre in precedenza era di 90 giorni.
12 luglio 2022
API Android Management
- Sono stati aggiunti i valori NETWORK_ACTIVITY_LOGS e SECURITY_LOGS a DelegatedScope per concedere alle applicazioni dei criteri del dispositivo l'accesso ai log corrispondenti.
14 giugno 2022
API Android Management
- Sono stati aggiunti specificNonComplianceReason e specificNonComplianceContext a NonComplianceDetail per fornire un contesto dettagliato per gli errori di applicazione delle norme.
6 giugno 2022
API Android Management
- È stato aggiunto un comando per consentire all'amministratore di cancellare da remoto i dati dell'applicazione di un'app.
- Ora i token di registrazione possono essere creati con una durata più lunga rispetto al precedente massimo di 90 giorni, fino a circa 10.000 anni. I token di registrazione con una durata superiore a 90 giorni avranno una lunghezza di 24 caratteri, mentre quelli con una durata pari o inferiore a 90 giorni continueranno ad avere 20 caratteri.
24 maggio 2022
API Android Management
- Le funzionalità di crittografia hardware, come l'attestazione di chiavi, verranno ora utilizzate nelle valutazioni dell'integrità del dispositivo, se supportate dal dispositivo. Ciò garantisce una solida integrità del sistema. I dispositivi che non superano queste valutazioni o che non supportano queste funzionalità di sicurezza basate sulla crittografia hardware segnaleranno il nuovo SecurityRisk HARDWARE_BACKED_EVALUATION_FAILED.
16 maggio 2022
API Android Management
- È stato aggiunto unifiedLockSettings in PasswordPolicies per consentire all'amministratore di configurare se il profilo di lavoro richiede un blocco separato.
25 marzo 2022
API Android Management
- È stata aggiunta l'impostazione alwaysOnVpnLockdownExemption per specificare quali app devono essere esentate dall'impostazione AlwaysOnVpnPackage.
- Sono stati aggiunti tutti i campi disponibili della risorsa Products dell'API Play EMM alla risorsa Application.
22 febbraio 2022
API Android Management
- È stato aggiunto cameraAccess per controllare l'uso della fotocamera e del relativo pulsante di attivazione/disattivazione, e microphoneAccess per controllare l'uso del microfono e del relativo pulsante di attivazione/disattivazione. Questi campi sostituiscono i campi cameraDisabled e unmuteMicrophoneDisabled, rispettivamente, appena ritirati.
15 febbraio 2022
SDK AMAPI
- Correzione di bug di secondaria importanza. Per ulteriori dettagli, consulta il repository Maven di Google.
15 novembre 2021
Android Device Policy
-
Le app contrassegnate come non disponibili in
personalApplicationsverranno ora disinstallate dal profilo personale dei dispositivi di proprietà aziendale, se già installate, come avviene in ApplicationPolicy per il profilo di lavoro e i dispositivi completamente gestiti.
17 settembre 2021
API Android Management
-
Ora puoi designare un'app come app di estensione utilizzando
ExtensionConfig. Le app di estensione possono comunicare direttamente con Android Device Policy e in futuro potranno interagire con l'insieme completo di funzionalità di gestione offerte nell'API Android Management, consentendo un'interfaccia locale per la gestione del dispositivo che non richiede la connettività del server.- Questa release iniziale include il supporto per l'esecuzione locale di
Commandse al momento solo il comandoClearAppData. Per ulteriori dettagli, consulta la guida all'integrazione dell'estensibilità. - I comandi rimanenti verranno aggiunti nel tempo, così come le funzionalità aggiuntive dell'app di estensione progettate per mostrare l'ampiezza delle funzionalità di gestione dei dispositivi all'app di estensione.
- Questa release iniziale include il supporto per l'esecuzione locale di
30 giugno 2021
Android Device Policy
- Correzioni di bug minori
2 giugno 2021
Android Device Policy
- Correzioni di bug minori
5 maggio 2021
Android Device Policy
- Correzioni di bug minori
6 aprile 2021
Android Device Policy
- Correzioni di bug minori
Marzo 2021
API Android Management
- Aggiunti due nuovi
AdvancedSecurityOverrides. Queste policy attivano le best practice per la sicurezza di Android Enterprise per impostazione predefinita, consentendo alle organizzazioni di sostituire i valori predefiniti per i casi d'uso avanzati. googlePlayProtectVerifyAppsattiva la verifica app di Google Play per impostazione predefinita.developerSettingsimpedisce agli utenti di accedere alle opzioni sviluppatore e alla modalità provvisoria per impostazione predefinita, funzionalità che altrimenti introducono il rischio di esfiltrazione dei dati aziendali.-
ChoosePrivateKeyRuleora supporta la concessione diretta di chiavi KeyChain specifiche alle app gestite. - Ciò consente alle app di destinazione di accedere a chiavi specifiche chiamando
getCertificateChain()egetPrivateKey()senza dover prima chiamarechoosePrivateKeyAlias(). - L'API Android Management concede per impostazione predefinita l'accesso diretto alle chiavi specificate nella policy, ma in caso contrario concede l'accesso dopo che l'app specificata ha chiamato
choosePrivateKeyAlias(). Per ulteriori dettagli, consultaChoosePrivateKeyRule.
Ritiri
ensureVerifyAppsEnabledè ora deprecato. Utilizza invecegooglePlayProtectVerifyAppsAdvancedSecurityOverrides.- Gli utenti API esistenti (progetti Google Cloud con l'API Android Management
abilitata al 15 aprile 2021) possono continuare a utilizzare
ensureVerifyAppsEnabledfino a ottobre 2021, ma sono invitati a eseguire la migrazione aAdvancedSecurityOverridesil prima possibile. A ottobreensureVerifyAppsEnablednon funzionerà più. debuggingFeaturesAllowedesafeBootDisabledsono ora deprecati. Utilizza invecedeveloperSettingsAdvancedSecurityOverrides.- Gli utenti API esistenti (progetti Google Cloud con l'API Android Management
abilitata al 15 aprile 2021) possono continuare a utilizzare
debuggingFeaturesAllowedesafeBootDisabledfino a ottobre 2021, ma sono invitati a utilizzareAdvancedSecurityOverridesil prima possibile. A ottobredebuggingFeaturesAllowedesafeBootDisablednon funzioneranno più.
Febbraio 2021
API Android Management
- È stato aggiunto il supporto di
personalApplicationsper i dispositivi di proprietà dell'azienda a partire da Android 8. La funzionalità è ora supportata su tutti i dispositivi di proprietà aziendale con un profilo di lavoro. - Il numero di telefono del dispositivo ora viene riportato sui dispositivi completamente gestiti come parte
della risorsa
Device.
Gennaio 2021
Android Device Policy
- Correzioni di bug minori
Dicembre 2020
API Android Management
- Aggiunta di
personalApplicationsaPersonalUsagePolicies. Sui dispositivi di proprietà aziendale, il reparto IT può specificare una lista consentita o una lista bloccata di applicazioni nel profilo personale. Questa funzionalità è attualmente disponibile solo sui dispositivi Android 11, ma verrà eseguito il backporting su Android 8 in una release futura.
Android Device Policy
- Aggiornamenti minori all'interfaccia utente di provisioning
Novembre 2020
API Android Management
- È stato aggiunto
AutoDateAndTimeZone, in sostituzione diautoTimeRequired, per controllare la configurazione automatica di data, ora e fuso orario su un dispositivo di proprietà dell'azienda. - A partire da Android 11, gli utenti non possono più cancellare i dati delle app o forzare
l'arresto delle applicazioni quando il dispositivo è configurato come kiosk (ovvero,
quando
InstallTypedi un'applicazione inApplicationPolicyè impostato suKIOSK). - Sono stati aggiunti nuovi controlli
LocationModeper sostituire i controlli del metodo di rilevamento della posizione deprecato. Sui dispositivi di proprietà dell'azienda, il reparto IT ora può scegliere se applicare la posizione, disattivarla o consentire agli utenti di attivarla e disattivarla. - È stato aggiunto il supporto per
CommonCriteriaMode, una nuova funzionalità di Android 11. Può essere attivata per soddisfare requisiti specifici Common Criteria Mobile Device Fundamentals Protection Profile (MDFPP).
Ritiri
autoTimeRequiredè ora deprecato, in seguito al deprecamento di controlli automatici specifici dell'ora in Android 11. UtilizzaAutoDateAndTimeZone.- Le seguenti opzioni
LocationModesono ora obsolete, in seguito alla loro obsolescenza in Android 9:HIGH_ACCURACY,SENSORS_ONLY,BATTERY_SAVINGeOFF. UtilizzaLOCATION_ENFORCED,LOCATION_DISABLEDeLOCATION_USER_CHOICE.
Ottobre 2020
Android Device Policy
- È stato aggiunto
RELINQUISH_OWNERSHIPcome nuovo tipo di comando del dispositivo. Quando implementano il profilo di lavoro, gli amministratori possono cedere la proprietà dei dispositivi di proprietà aziendale ai dipendenti, cancellando il profilo di lavoro e ripristinando lo stato di fabbrica di tutti i criteri del dispositivo, lasciando intatti i dati personali. In questo modo, il reparto IT perde il diritto di proprietà del dispositivo ora e in futuro e non deve aspettarsi che il dispositivo venga registrato di nuovo. Per ripristinare i dati di fabbrica di un dispositivo mantenendone la proprietà, utilizza il metododevices.delete.
Agosto 2020
API Android Management
-
I miglioramenti all'esperienza del profilo di lavoro sui dispositivi di proprietà aziendale sono stati annunciati nell'anteprima per gli sviluppatori di Android 11. L'API Android Management aggiunge il supporto a questi miglioramenti per i dispositivi con Android 8.0+ o versioni successive. Le aziende ora possono designare i dispositivi con profilo di lavoro come di proprietà aziendale, consentendo la gestione del profilo di lavoro di un dispositivo, dei criteri di utilizzo personale e di determinate impostazioni a livello di dispositivo, mantenendo al contempo la privacy nel profilo personale.
- Per una panoramica generale del miglioramento dell'esperienza del profilo di lavoro, vedi Profilo di lavoro: il nuovo standard per la privacy dei dipendenti.
- Consulta la sezione Dispositivi di proprietà dell'azienda per uso lavorativo e personale per scoprire come configurare un profilo di lavoro su un dispositivo di proprietà dell'azienda.
- Un esempio di norma per un dispositivo di proprietà dell'azienda con un profilo di lavoro è disponibile in Dispositivi con profili di lavoro.
- Aggiunta di
blockScopeablockAction. UtilizzablockScopeper specificare se un'azione di blocco si applica a un intero dispositivo di proprietà aziendale o solo al suo profilo di lavoro.
Aggiunta di
connectedWorkAndPersonalAppaapplicationPolicy. A partire da Android 11, alcune app di base possono connettersi tra i profili di lavoro e personali di un dispositivo. Se colleghi un'app tra profili, puoi offrire un'esperienza più unificata agli utenti. Ad esempio, se collegano un'app di calendario, gli utenti possono visualizzare insieme i propri eventi di lavoro e personali.Alcune app (ad esempio la Ricerca Google) potrebbero essere collegate per impostazione predefinita sui dispositivi. Un elenco delle app connesse su un dispositivo è disponibile in Impostazioni > Privacy > App personali e di lavoro collegate.
Utilizza
connectedWorkAndPersonalAppper consentire o non consentire le app collegate. Se consenti a un'app di connettersi tra profili, l'utente ha solo la possibilità di connettere l'app. Gli utenti possono disconnettere le app in qualsiasi momento.È stato aggiunto
systemUpdateInfoadevicesper segnalare informazioni sugli aggiornamenti di sistema in attesa.
Luglio 2020
Android Device Policy
- [23 luglio] Correzioni di bug minori
Giugno 2020
Android Device Policy
- [17 giugno] Correzioni di bug minori.
Maggio 2020
Android Device Policy
- [12 maggio] Correzioni di bug minori.
Aprile 2020
Android Device Policy
- [14 aprile] Correzioni di bug minori.
Marzo 2020
Android Device Policy
- [16 marzo] Correzioni di bug minori.
Febbraio 2020
Android Device Policy
- [24 febbraio] Correzioni di bug minori.
Gennaio 2020
Android Device Policy
- [15 gennaio] Correzioni di bug minori.
Dicembre 2019
API Android Management
- È disponibile una nuova norma per il blocco delle app non attendibili (app da origini sconosciute). Utilizza
advancedSecurityOverrides.untrustedAppsPolicyper:- Blocca le installazioni di app non attendibili a livello di dispositivo (inclusi i profili di lavoro).
- Blocca l'installazione di app non attendibili solo in un profilo di lavoro.
- Consenti l'installazione di app non attendibili a livello di dispositivo.
- Ora è possibile applicare un periodo di timeout per consentire metodi di blocco schermo non sicuri (ad es.
sblocco con l'impronta e con il volto) su un dispositivo o un profilo di lavoro
utilizzando
requirePasswordUnlock. Al termine del periodo di timeout, un utente deve utilizzare una forma di autenticazione avanzata (password, PIN, sequenza) per sbloccare un dispositivo o un profilo di lavoro. - È stato aggiunto
kioskCustomizationper supportare la possibilità di attivare o disattivare le seguenti funzionalità dell'interfaccia utente di sistema nei dispositivi in modalità kiosk:- Azioni globali avviate dal tasto di accensione (vedi
powerButtonActions). - Informazioni e notifiche di sistema (vedi
statusBar). - Pulsanti Home e Panoramica (vedi
systemNavigation). - Barra di stato (vedi
statusBar). - Finestre di dialogo di errore per app che hanno subito un arresto anomalo o non rispondono (vedi
systemErrorWarnings).
- Azioni globali avviate dal tasto di accensione (vedi
- È stato aggiunto il criterio
freezePeriodper supportare il blocco degli aggiornamenti di sistema annuali durante un periodo di blocco specifico. - Un nuovo parametro è disponibile in
devices.delete:wipeReasonMessageti consente di specificare un breve messaggio da mostrare a un utente prima di cancellare il profilo di lavoro dal suo dispositivo personale.
Ritiri
installUnknownSourcesAllowed è ora contrassegnato come ritirato.
Il supporto del criterio continuerà fino al secondo trimestre del 2020 per gli utenti che hanno attivato
l'API Android Management prima delle 14:00 GMT del 19 dicembre 2019.
Il criterio non è supportato per gli utenti che hanno attivato l'API dopo questa data.
advancedSecurityOverrides.untrustedAppsPolicy sostituisce installUnknownSourcesAllowed.
La tabella seguente fornisce una mappatura tra le due norme. Gli sviluppatori devono
aggiornare le loro soluzioni con le nuove norme il prima possibile*.
| installUnknownSourcesAllowed | advancedSecurityOverrides.untrustedAppsPolicy |
|---|---|
TRUE |
ALLOW_INSTALL_DEVICE_WIDE |
FALSE |
ALLOW_INSTALL_IN_PERSONAL_PROFILE_ONLYNota:applicato a tutti i tipi di dispositivi (profili di lavoro e completamente
gestiti). Poiché i dispositivi completamente gestiti non hanno un profilo personale,
le app non attendibili vengono bloccate su tutto il dispositivo. Per bloccare le app non attendibili
su un intero dispositivo con un profilo di lavoro, utilizza
|
untrustedAppsPolicy (DISALLOW_INSTALL) non viene applicato se untrustedAppsPolicy è impostato su
UNTRUSTED_APPS_POLICY_UNSPECIFIED o se il criterio non è
specificato. Per bloccare le app non attendibili su un intero dispositivo, devi
impostare esplicitamente il criterio su DISALLOW_INSTALL.
Novembre 2019
Android Device Policy
- [27 novembre] Correzioni di bug minori.
Ottobre 2019
API Android Management
- Le nuove opzioni
IframeFeatureti consentono di specificare quali funzionalità dell'iframe della versione gestita di Google Play attivare/disattivare nella console.
Android Device Policy
- [16 ottobre] Correzioni di bug minori e ottimizzazione delle prestazioni.
4 settembre 2019
Funzionalità
- La risorsa
policiesora è in grado di distribuire release di app chiuse (canali di test chiuso), consentendo alle organizzazioni di testare le versioni pre-release delle app. Per maggiori dettagli, vedi Distribuire app per i test chiusi. - Aggiunta di
permittedAccessibilityServicesapolicies, che può essere utilizzato per:- non consentire tutti i servizi di accessibilità non di sistema su un dispositivo oppure
- consentire solo alle app specificate di accedere a questi servizi.
6 agosto 2019
Funzionalità
- L'API Android Management ora valuta la sicurezza di un dispositivo e
segnala i risultati nei report sui dispositivi
(in
securityPosture).securityPosturerestituisce lo stato della postura di sicurezza di un dispositivo (POSTURE_UNSPECIFIED,SECURE,AT_RISKoPOTENTIALLY_COMPROMISED), come valutato da SafetyNet e altri controlli, insieme ai dettagli di eventuali rischi per la sicurezza identificati da condividere con i clienti tramite la console di gestione.Per attivare questa funzionalità per un dispositivo, assicurati che i relativi criteri abbiano almeno un campo di
statusReportingSettingsabilitato.
2 luglio 2019
Funzionalità
- Per distinguere l'avvio di un'app da
launchAppinsetupActions, l'attività avviata per prima come parte dell'app ora contiene l'extra dell'intent booleanocom.google.android.apps.work.clouddpc.EXTRA_LAUNCHED_AS_SETUP_ACTION(impostato sutrue). Questo extra ti consente di personalizzare la tua app in base all'avvio dalaunchAppo da parte di un utente.
31 maggio 2019
Release di manutenzione
- Correzioni di bug minori e ottimizzazione delle prestazioni.
7 maggio 2019
Funzionalità
- È stato aggiunto
policyEnforcementRulesper sostituirecomplianceRules, che è stato ritirato. Per ulteriori informazioni, consulta l'avviso di ritiro riportato sopra. - Sono state aggiunte nuove API per creare e modificare app web. Per maggiori dettagli, vedi Supporto delle app web.
Esperienza utente
Android Device Policy:l'icona dell'app non è più visibile sui dispositivi. Gli utenti possono comunque visualizzare la pagina dei criteri precedentemente avviata dall'icona:
- Dispositivi completamente gestiti: Impostazioni > Google > Criteri dispositivo
- Dispositivi con profili di lavoro: Impostazioni > Google > Lavoro > Device Policy
- Tutti i dispositivi: app Google Play Store > Android Device Policy
16 aprile 2019
- Android Device Policy è ora disponibile in Corea del Sud.
21 marzo 2019
Funzionalità
- Sono stati aggiunti nuovi metadati, inclusi numeri di serie alternativi, a
devices. - Il numero di app con
installTypeREQUIRED_FOR_SETUPè ora limitato a cinque per norma. per garantire la migliore esperienza utente possibile durante il provisioning del dispositivo e del profilo di lavoro.
12 febbraio 2019
Esperienza utente
- Android Device Policy:è stata aggiunta una messaggistica di mancata conformità migliorata per aiutare gli utenti a riportare i propri dispositivi a uno stato conforme o per informarli quando non è possibile.
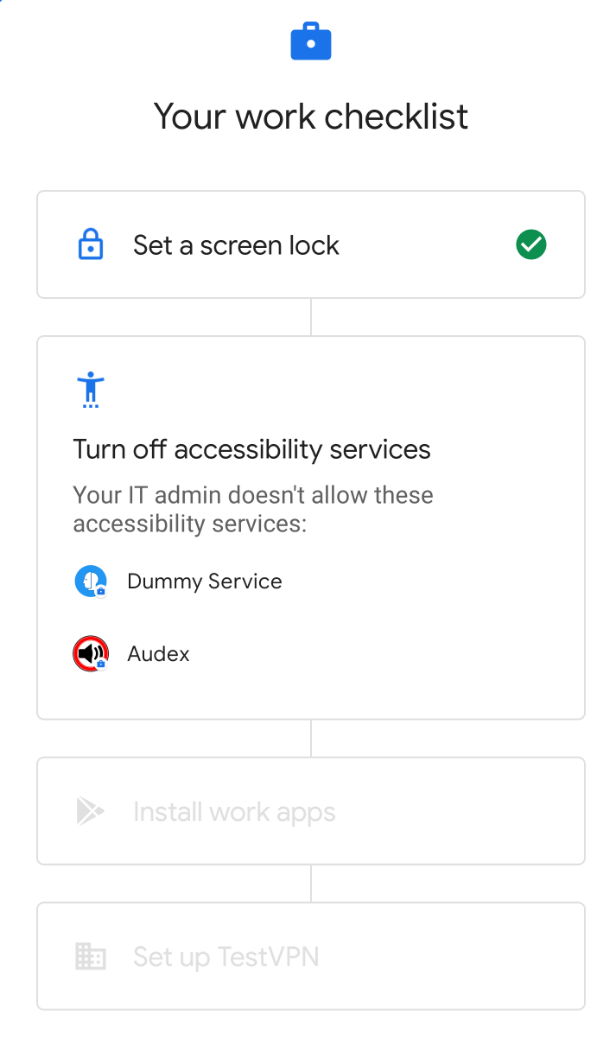
- Android Device Policy:dopo la registrazione di un token di registrazione, una
nuova esperienza di configurazione guida gli utenti attraverso i passaggi richiesti dalle norme
per completare la configurazione del dispositivo o del profilo di lavoro.
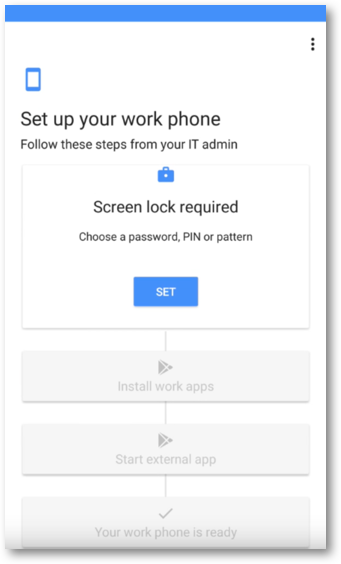
Figura 1. Esperienza di configurazione guidata.
Funzionalità
- Aggiunto nuovo campo a
installTypeREQUIRED_FOR_SETUP: se è true, l'app deve essere installata prima del completamento della configurazione del dispositivo o del profilo di lavoro. Nota:se l'app non è installata per qualsiasi motivo (ad es. incompatibilità, disponibilità geografica, connessione di rete scarsa), la configurazione non verrà completata.
- Aggiunta di
SetupActionapolicies. ConSetupAction, puoi specificare un'app da avviare durante la configurazione, consentendo a un utente di configurare ulteriormente il proprio dispositivo. Per maggiori dettagli, vedi Avviare un'app durante la configurazione. - Per le aziende con i report sullo stato abilitati, i nuovi report sui dispositivi vengono ora emessi immediatamente dopo qualsiasi tentativo non riuscito di sbloccare un dispositivo o un profilo di lavoro.
Ritiri
- In
policies,wifiConfigsLockdownEnabledè stato deprecato. Le reti Wi-Fi specifiche sono ora non modificabili per impostazione predefinita. Per renderli modificabili, impostawifiConfigDisabledsu false.
10 dicembre 2018
Funzionalità
- È stato aggiunto il supporto per i dispositivi con profilo di lavoro al metodo di provisioning dell'URL di accesso. I proprietari di dispositivi con profilo di lavoro ora possono accedere con le proprie credenziali aziendali per completare il provisioning.
Esperienza utente
È stato aggiunto il supporto della modalità Buio in Android Device Policy. La modalità Buio è un tema di visualizzazione disponibile in Android 9 Pie, che può essere attivato in Impostazioni > Display > Avanzate > Tema del dispositivo > Buio.
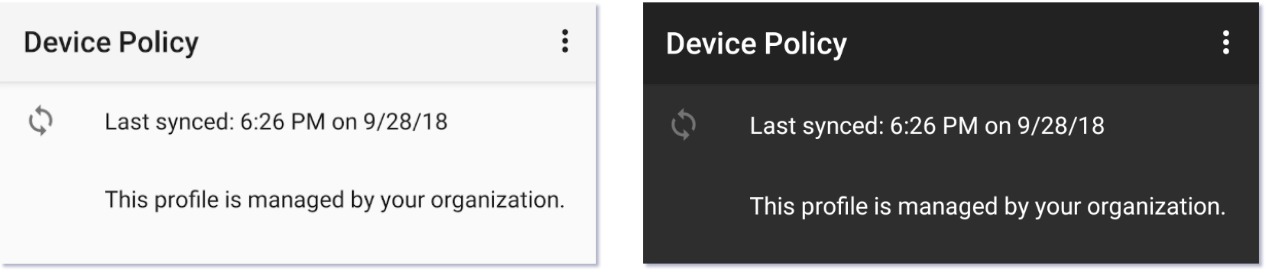
Figura 1. (L) Modalità di visualizzazione normale (R) Modalità Buio
2 novembre 2018
Funzionalità
- È disponibile un nuovo metodo di registrazione per i dispositivi completamente gestiti. Il metodo utilizza un URL di accesso per chiedere agli utenti di inserire le proprie credenziali, consentendoti di assegnare un criterio ed eseguire il provisioning dei dispositivi degli utenti in base alla loro identità.
- È stato aggiunto il supporto dell'iframe delle configurazioni gestite,
un'interfaccia utente che puoi aggiungere alla console per consentire agli amministratori IT di impostare e salvare le configurazioni gestite. L'iframe restituisce un
mcmIdunivoco per ogni configurazione salvata, che puoi aggiungere apolicies. - Aggiunta di
passwordPoliciesePasswordPolicyScopeapolicies:passwordPoliciesimposta i requisiti della password per l'ambito specificato (dispositivo o profilo di lavoro).- Se
PasswordPolicyScopenon è specificato, l'ambito predefinito èSCOPE_PROFILEper i dispositivi con profilo di lavoro eSCOPE_DEVICEper i dispositivi completamente gestiti o dedicati. passwordPoliciessostituiscepasswordRequirementssePasswordPolicyScopenon è specificato (valore predefinito) oPasswordPolicyScopeè impostato sullo stesso ambito dipasswordRequirements
20 settembre 2018
Correzioni di bug
- È stato risolto un problema che faceva sì che i dispositivi kiosk risultassero erroneamente non conformi dopo il provisioning, per un sottoinsieme di configurazioni dei criteri
28 agosto 2018
Funzionalità
Aggiornamenti per supportare il provisioning e la gestione di profili di lavoro e dispositivi completamente gestiti:
- Sono disponibili nuovi metodi di provisioning per i profili di lavoro:
- Fornisci agli utenti un link al token di registrazione.
- Vai a Impostazioni > Google > Configura profilo di lavoro.
- Sono stati aggiunti nuovi campi a
enrollmentTokens.oneTimeOnly: se è true, il token di registrazione scadrà dopo il primo utilizzo.userAccountIdentifier: identifica un account Google Play gestito specifico.- Se non specificato: l'API crea automaticamente un nuovo account ogni volta che un dispositivo viene registrato con il token.
- Se specificato: l'API utilizza l'account specificato ogni volta che un dispositivo viene registrato con il token. Puoi specificare lo stesso account in più token. Per ulteriori informazioni, vedi Specificare un utente.
- Aggiunta di
managementMode(sola lettura) adevices.- Dispositivi con profili di lavoro:
managementModeè impostato suPROFILE_OWNER. - Dispositivi dedicati e dispositivi completamente gestiti:
managementModeè impostato suDEVICE_OWNER.
- Dispositivi con profili di lavoro:
Aggiornamenti alla risorsa policies per migliorare le funzionalità di gestione delle app:
- È stato aggiunto il nuovo campo
playStoreMode.WHITELIST(impostazione predefinita): solo le app aggiunte ai criteri sono disponibili nel profilo di lavoro o sul dispositivo gestito. Qualsiasi app non inclusa nelle norme non è disponibile e viene disinstallata se era stata installata in precedenza.BLACKLIST: Le app aggiunte alla policy non sono disponibili. Tutte le altre app elencate su Google Play sono disponibili.
- È stato aggiunto
BLOCKEDcome opzione InstallType, che impedisce l'installazione di un'app. Se l'app è già installata, verrà disinstallata.- Puoi utilizzare installType
BLOCKEDinsieme aplayStoreModeBLACKLISTper impedire a un dispositivo gestito o a un profilo di lavoro di installare app specifiche.
- Puoi utilizzare installType
Esperienza utente
- Impostazioni di Android Device Policy aggiornate in modo che corrispondano alle impostazioni del dispositivo.
12 luglio 2018
Esperienza utente
- Unite le pagine di stato e dei dettagli del dispositivo in Android Device Policy in un'unica pagina.
- Coerenza migliorata dell'interfaccia utente di configurazione con la configurazione guidata di Android.
Funzionalità
- È stato aggiunto PermissionGrants a livello di criterio. Ora puoi controllare
le autorizzazioni di runtime a quattro livelli:
- Globale, per tutte le app: imposta defaultPermissionPolicy a livello di criterio.
- Per autorizzazione, in tutte le app: imposta permissionGrant a livello di policy.
- Per app, in tutte le autorizzazioni:imposta defaultPermissionPolicy all'interno di ApplicationPolicy.
- Per app, per autorizzazione:imposta permissionGrant all'interno di ApplicationPolicy.
- Quando ripristini i dati di fabbrica di un dispositivo, il nuovo WipeDataFlag ti consente di:
WIPE_EXTERNAL_STORAGE: pulisci la memoria esterna del dispositivo (ad es. schede SD).PRESERVE_RESET_PROTECTION_DATA: conserva i dati della protezione ripristino dati di fabbrica sul dispositivo. Questo flag garantisce che solo un utente autorizzato possa recuperare un dispositivo se, ad esempio, il dispositivo viene smarrito. Nota:attiva questa funzionalità solo se hai impostatofrpAdminEmails[]nella policy.
Correzioni di bug
- È stato risolto il problema relativo all'uscita di Android Device Policy dalla modalità di blocco attività durante l'aggiornamento in primo piano.
25 maggio 2018
Esperienza utente
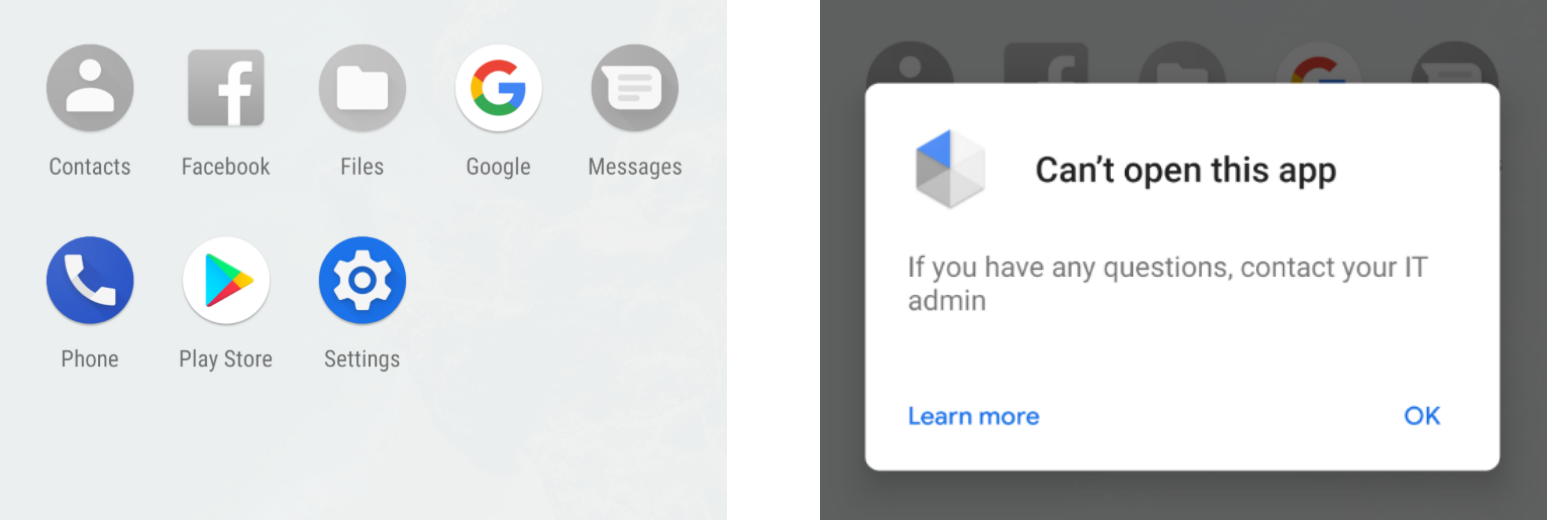
- Anziché nascondere le app disattivate dal launcher, i dispositivi Android 7.0 e versioni successive
ora mostrano le icone delle app disattivate in grigio:
Funzionalità
policiesè stato aggiornato per supportare le seguenti funzionalità di gestione dei certificati:- Concessione automatica dell'accesso ai certificati alle app.
- Delega di tutte le funzionalità di gestione dei certificati supportate da
Android Device Policy a un'altra app (vedi
CERT_INSTALL).
- Ora le singole app possono essere disattivate in ApplicationPolicy (imposta
disabledsutrue), indipendentemente dalle regole di conformità . - Ora è possibile disattivare le app di sistema.
- Aggiunti i report sulle applicazioni a
devices. Per ogni app gestita installata su un dispositivo, il report restituisce il nome del pacchetto, la versione, l'origine dell'installazione e altre informazioni dettagliate. Per attivare, impostaapplicationReportsEnabledsutruenel criterio del dispositivo. - Aggiornamento di
enterprisesper includere i termini e condizioni. I termini e condizioni di un'azienda vengono visualizzati sui dispositivi durante il provisioning.
Correzioni di bug
- Flusso di provisioning aggiornato per disabilitare l'accesso alle impostazioni, tranne quando l'accesso è necessario per completare la configurazione (ad es. la creazione di un passcode).
3 aprile 2018
Esperienza utente
- È stato aggiornato il design di Android Device Policy e del flusso di provisioning dei dispositivi per migliorare l'esperienza utente complessiva.
Funzionalità
- È stato aggiunto il supporto per l'avvio diretto, che consente di cancellare da remoto i dispositivi Android 7.0 e versioni successive che non sono stati sbloccati dall'ultimo riavvio.
- È stata aggiunta un'impostazione modalità di localizzazione alla risorsa
policies, che consente di configurare la modalità di precisione della localizzazione su un dispositivo gestito. - È stato aggiunto un campo di risposta di errore alla risorsa
Command.
Correzioni di bug
- Le prestazioni del provisioning sono state migliorate.
- I report di conformità vengono ora generati immediatamente dopo il provisioning di un dispositivo. Per configurare un'azienda in modo che riceva i report sulla conformità, vedi Ricevere notifiche dettagliate sulla mancata conformità.
Problemi noti
- Le impostazioni della schermata di blocco si arrestano in modo anomalo sui dispositivi LG con Android 8.0 o versioni successive (ad es. LG V30) gestiti da Android Device Policy.
14 febbraio 2018
Esperienza utente
- È stato aggiornato il testo di convalida per il campo "codice", che viene visualizzato se un utente sceglie di inserire manualmente un codice QR per registrare un dispositivo.
Funzionalità
- Ora puoi impostare un criterio per attivare l'aggiornamento automatico delle app installate forzatamente se
non soddisfano una versione minima specificata dell'app. In
ApplicationPolicy:
- Imposta
installTypesuFORCE_INSTALLED - Specifica un valore
minimumVersionCode.
- Imposta
- È stata aggiornata la risorsa Dispositivi con nuovi campi contenenti informazioni che potrebbero essere utili agli amministratori IT, come il nome dell'operatore del dispositivo (vedi NetworkInfo per maggiori dettagli), se il dispositivo è criptato e se Verifica app è attivata (vedi DeviceSettings per maggiori dettagli).
Correzioni di bug
- I comandi
RESET_PASSWORDeLOCKora funzionano con i dispositivi Android 8.0 Oreo. - È stato risolto il problema relativo al mancato popolamento di DeviceSettings.
- È stato risolto il problema relativo alla gestione delle norme
stayOnPluggedModes.
12 dicembre 2017
Funzionalità
- Android Device Policy ora supporta un launcher kiosk di base, che può essere attivato tramite criterio. L'avvio app blocca un dispositivo su un insieme di app predefinite e impedisce all'utente di accedere alle impostazioni del dispositivo. Le app specificate vengono visualizzate in ordine alfabetico su una sola pagina. Per segnalare un bug o richiedere una funzionalità, tocca l'icona del feedback nel launcher.
- Configurazione del dispositivo aggiornata con una nuova logica di nuovi tentativi. Se un dispositivo viene riavviato durante la configurazione, la procedura di provisioning ora continua da dove era stata interrotta.
- Sono ora disponibili le seguenti nuove norme. Per tutti i dettagli, consulta il
riferimento
API:
keyguardDisabledFeaturesaccountTypesWithManagementDisabledinstallAppsDisabledmountPhysicalMediaDisableduninstallAppsDisabledbluetoothContactSharingDisabledshortSupportMessagelongSupportMessagebluetoothConfigDisabledcellBroadcastsConfigDisabledcredentialsConfigDisabledmobileNetworksConfigDisabledtetheringConfigDisabledvpnConfigDisabledcreateWindowsDisablednetworkResetDisabledoutgoingBeamDisabledoutgoingCallsDisabledsmsDisabledusbFileTransferDisabledensureVerifyAppsEnabledpermittedInputMethodsrecommendedGlobalProxysetUserIconDisabledsetWallpaperDisabledalwaysOnVpnPackagedataRoamingDisabledbluetoothDisabled - L'SDK di destinazione di Android Device Policy è stato aggiornato ad Android 8.0 Oreo.
Correzioni di bug
- Ora è possibile saltare la visualizzazione del selettore di rete se non è possibile
stabilire una connessione all'avvio. Per attivare il selettore di rete all'avvio, utilizza il criterio
networkEscapeHatchEnabled.

