OAuth 및 Google 로그인 연결 유형은 OAuth 기반에 Google 로그인을 추가합니다. 계정 연결 이를 통해 Google 사용자에게 원활한 음성 기반 연결이 제공됩니다. 또한 서비스에 등록한 사용자의 계정 연결을 사용 설정할 수 있습니다. Google이 아닌 다른 ID를 사용하는 경우일 수 있습니다
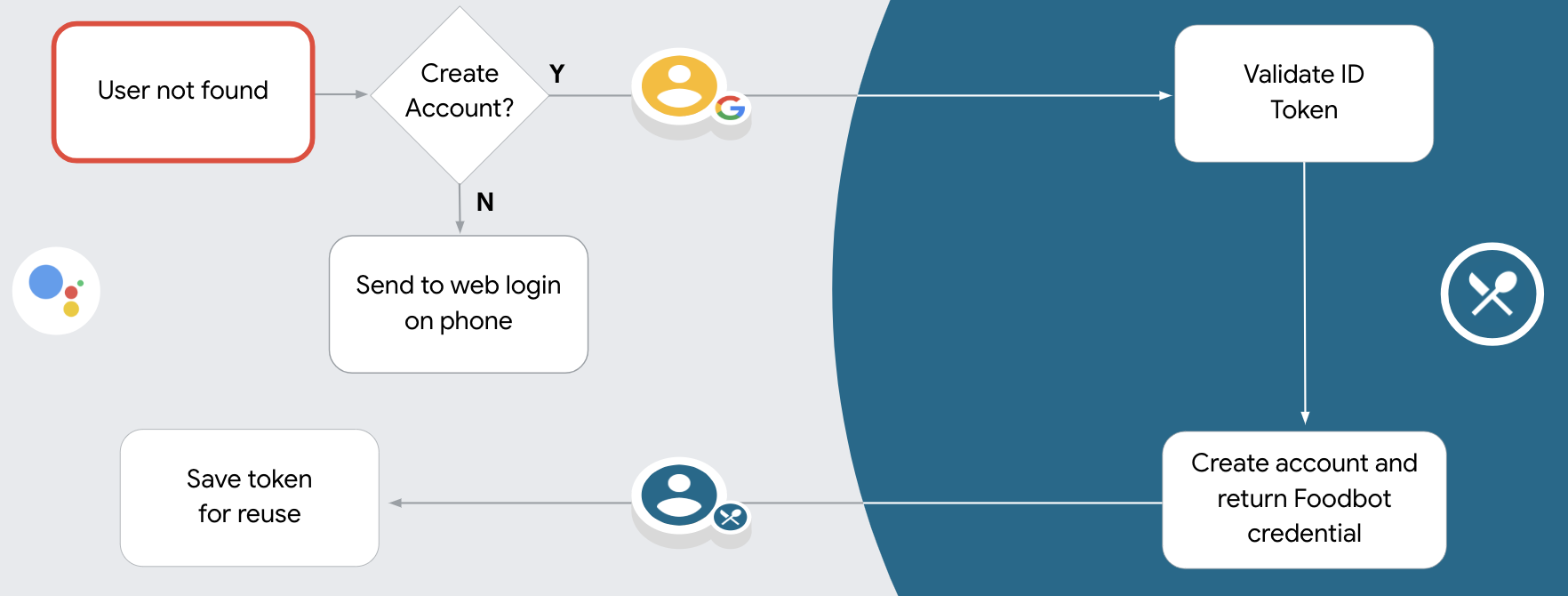
이 연결 유형은 Google 로그인으로 시작하며, 이를 통해 사용자의 Google 프로필 정보가 시스템에 존재합니다. 사용자 정보가 시스템에서 찾을 수 없는 경우 표준 OAuth 흐름이 시작됩니다. 사용자는 다음 작업도 가능합니다. Google 프로필 정보를 사용하여 새 계정을 만들기로 선택하는 경우
<ph type="x-smartling-placeholder">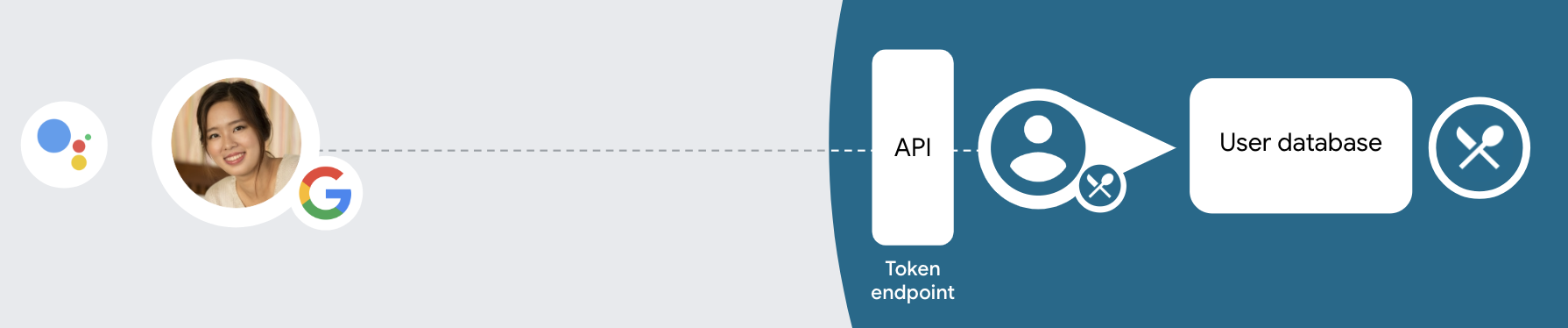
OAuth 및 Google 로그인으로 계정을 연결하려면 다음 일반 단계를 따르세요. 단계:
- 먼저 사용자에게 Google 프로필 액세스에 동의해 달라고 요청합니다.
- 사용자 프로필의 정보를 사용하여 사용자를 식별합니다.
- 인증 시스템에서 Google 사용자와 일치하는 항목을 찾을 수 없는 경우
작업 프로젝트를 구성했는지 여부에 따라 흐름이 진행됩니다.
확인할 수 있습니다
- 음성을 통한 계정 생성을 허용하는 경우 ID를 검증하세요. 토큰입니다. 그런 다음 ID 토큰에 포함된 프로필 정보입니다.
- 음성을 통한 계정 생성을 허용하지 않으면 사용자가 다음으로 이전됩니다. 승인 페이지를 로드하고 사용자 인증 정보를 완료할 수 있는 브라우저 만들 수 있습니다.
음성을 통한 계정 생성 지원
음성을 통한 사용자 계정 생성을 허용하면 어시스턴트에서 사용자에게 다음과 같이 하려고 합니다.
- Google 계정 정보를 사용하여 시스템에서 새 계정을 만듭니다.
- 다른 계정이 있는 경우 다른 계정으로 인증 시스템에 로그인하세요. 계정에 연결할 수 없습니다.
이러한 문제를 최소화하려면 음성을 통한 계정 생성을 허용하는 것이 좋습니다. 계정 생성 흐름의 마찰이 있습니다 사용자는 음성 흐름에서 나가기만 하면 됨 (Google 계정이 아닌 기존 계정을 사용하여 로그인하려는 경우).
음성을 통한 계정 생성 허용 안함
음성을 통한 사용자 계정 생성을 허용하지 않은 경우 어시스턴트는 사용자 인증을 위해 제공한 웹사이트가 포함됩니다. 상호 작용이 발생하는 경우 화면이 없는 기기에서는 어시스턴트가 사용자를 휴대전화로 안내합니다. 계정 연결 절차를 계속 진행합니다.
다음과 같은 경우 생성을 허용하지 않는 것이 좋습니다.
Google 이외의 계정이 있는 사용자가 해당 사용자가 계정의 기존 사용자 계정에 연결하도록 하려는 인증 시스템을 사용할 것입니다. 예를 들어 포인트 멤버십을 제공하는 경우 사용자가 포인트를 잃어버리지 않도록 계정을 만들 수 있습니다.
계정 생성 절차를 완전히 관리할 수 있어야 합니다. 예를 들어 사용자에게 서비스 약관을 표시해야 하는 경우 계정 만들기
OAuth 및 Google 로그인 계정 연결 구현
계정은 업계 표준 OAuth 2.0 흐름으로 연결됩니다. Actions on Google은 암시적 코드 및 승인 코드 흐름을 지원합니다.
암시적 코드 흐름에서 Google은 사용자의 브라우저에서 승인 엔드포인트를 엽니다. 로그인에 성공하면 수명이 긴 액세스 토큰을 Google에 반환합니다. 이제 어시스턴트에서 작업으로 전송되는 모든 요청에 이 액세스 토큰이 포함됩니다.
승인 코드 흐름에는 두 개의 엔드포인트가 필요합니다.
- 승인 엔드포인트: 아직 로그인하지 않은 사용자에게 로그인 UI를 표시하고 요청한 액세스에 대한 동의를 단기 승인 코드 형식으로 기록하는 역할을 합니다.
- 두 가지 유형의 교환을 담당하는 토큰 교환 엔드포인트:
- 장기 갱신 토큰과 단기 액세스 토큰으로 승인 코드를 교환합니다. 이 교환은 사용자가 계정 연결 흐름을 진행할 때 이루어집니다.
- 장기 갱신 토큰을 단기 액세스 토큰으로 교환합니다. 이 교환은 액세스 토큰이 만료되어 Google에 새 액세스 토큰이 필요할 때 발생합니다.
암시적 코드 흐름을 구현하는 것이 더 간단하지만 암시적 흐름을 사용하여 발급된 액세스 토큰은 만료되지 않는 것이 좋습니다. 토큰 만료를 암시적 흐름과 함께 사용하면 사용자가 계정을 다시 연결하게 되기 때문입니다. 보안상의 이유로 토큰 만료가 필요하다면 인증 코드 흐름을 대신 사용하는 것이 좋습니다.
프로젝트 구성
OAuth 및 Google 로그인 계정을 사용하도록 프로젝트 구성 다음 단계를 따르세요.
- Actions 콘솔을 열고 사용하려는 프로젝트를 선택합니다.
- 개발 탭을 클릭하고 계정 연결을 선택합니다.
- 계정 연결 옆의 스위치를 켭니다. <ph type="x-smartling-placeholder">
- 계정 만들기 섹션에서 예를 선택합니다.
연결 유형에서 OAuth & Google 로그인 및 암시적
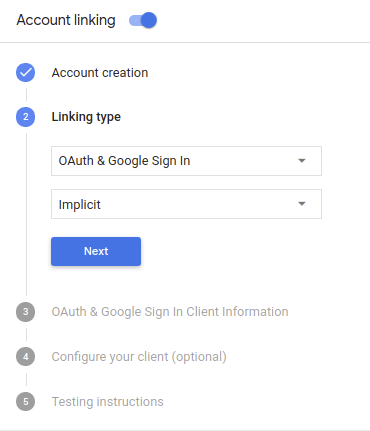
클라이언트 정보에서 다음을 수행합니다.
- 내 작업에서 Google에 발급한 클라이언트 ID에 값을 할당하여 Google에서 전송하는 요청입니다. <ph type="x-smartling-placeholder"></ph>
- 승인 및 토큰 교환 엔드포인트의 URL을 입력하세요.
저장을 클릭합니다.
OAuth 서버 구현
OAuth 2.0 암시적 흐름을 지원하기 위해 서비스 승인 사용할 수 있습니다 이 엔드포인트는 데이터 액세스에 대한 사용자의 동의 받기 승인 엔드포인트 아직 로그인하지 않은 사용자에게 로그인 UI를 표시하고 액세스할 수 있도록 합니다.
작업이 서비스의 승인된 API 중 하나를 호출해야 하는 경우 Google은 이 엔드포인트를 있습니다.
Google에서 시작한 일반적인 OAuth 2.0 암시적 흐름 세션에는 다음 흐름을 따라 하세요.
- Google은 사용자의 브라우저에서 승인 엔드포인트를 엽니다. 이 사용자가 로그인하지 않은 경우 로그인하고 Google에 액세스 권한을 부여합니다. 아직 권한을 부여하지 않은 경우 API를 통해 해당 데이터에 액세스할 수 있습니다.
- 서비스에서 액세스 토큰을 만들고 이를 액세스 토큰을 사용하여 사용자의 브라우저를 Google로 다시 리디렉션함 이 요청에 첨부됩니다.
- Google은 서비스의 API를 호출하고 실행할 수 있습니다 서비스에서 액세스 토큰이 Google에 인증한 다음 API 호출을 완료합니다.
승인 요청 처리
작업이 OAuth2 암시적 흐름을 통해 계정 연결을 수행해야 하는 경우 Google은 다음을 포함한 요청과 함께 사용자를 승인 엔드포인트로 보냅니다. 다음과 같습니다.
| 승인 엔드포인트 매개변수 | |
|---|---|
client_id |
Google에 할당한 클라이언트 ID입니다. |
redirect_uri |
이 요청에 대한 응답을 보낼 URL입니다. |
state |
정해진 기간에 변경되지 않고 Google에 다시 전달되는 리디렉션 URI를 사용할 수 있습니다. |
response_type |
응답에서 반환할 값의 유형입니다. OAuth 2.0 암시적
흐름에서 응답 유형은 항상 token입니다. |
예를 들어 승인 엔드포인트를 https://myservice.example.com/auth에서 사용할 수 있는 경우
요청은 다음과 같을 수 있습니다.
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token
승인 엔드포인트가 로그인 요청을 처리하려면 다음 단계를 따르세요.
다음과 같이
client_id및redirect_uri값을 확인합니다. 의도하지 않았거나 잘못 구성된 클라이언트 앱에 액세스 권한을 부여하지 않도록 합니다.client_id가 등록된 클라이언트 ID와 일치하는지 확인합니다. 확인할 수 있습니다redirect_uri에서 지정한 URL인지 확인합니다. 매개변수의 형식은 다음과 같습니다.https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
사용자가 서비스에 로그인했는지 확인합니다. 사용자가 로그인하지 않은 경우 서비스의 로그인 또는 가입 절차를 완료합니다.
Google에서 API에 액세스하는 데 사용할 액세스 토큰을 생성합니다. 이 액세스 토큰은 임의의 문자열 값이 될 수 있지만 클라이언트와 클라이언트에게 전달하며 추측할 수 없어야 합니다.
사용자의 브라우저를 URL로 리디렉션하는 HTTP 응답 전송
redirect_uri매개변수로 지정됩니다. 다음을 모두 포함 다음 매개변수를 포함합니다.access_token: 방금 생성한 액세스 토큰입니다.token_type: 문자열bearerstate: 원본의 수정되지 않은 상태 값입니다. 요청 다음은 결과 URL의 예입니다.https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
Google의 OAuth 2.0 리디렉션 핸들러가 액세스 토큰을 수신하고
state 값이 변경되지 않았음을 확인합니다. Google이
Google에서 후속 호출에 토큰을 첨부합니다.
작업을 AppRequest의 일부로 추가해야 합니다.
자동 연결 처리
사용자가 작업에서 Google 프로필에 액세스하는 데 동의하면 Google 사용자 ID의 서명된 어설션이 포함된 요청을 보냅니다. 어설션에는 사용자의 Google 계정 ID, 이름, 이메일 주소가 필요합니다. 프로젝트용으로 구성된 토큰 교환 엔드포인트는 확인할 수 있습니다
해당하는 Google 계정이 인증 시스템에 이미 있는 경우
토큰 교환 엔드포인트가 사용자의 토큰을 반환합니다. Google 계정에서
기존 사용자와 일치하면 토큰 교환 엔드포인트가 user_not_found 오류를 반환합니다.
요청의 형식은 다음과 같습니다.
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&intent=get&assertion=JWT&consent_code=CONSENT_CODE&scope=SCOPES
토큰 교환 엔드포인트는 다음 매개변수를 처리할 수 있어야 합니다.
| 토큰 엔드포인트 매개변수 | |
|---|---|
grant_type |
교환되는 토큰의 유형입니다. 이러한 요청의 경우
매개변수의 값은 urn:ietf:params:oauth:grant-type:jwt-bearer입니다. |
intent |
이러한 요청에서 이 매개변수의 값은 `get`입니다. |
assertion |
Google API의 서명된 어설션을 제공하는 JSON 웹 토큰 (JWT)입니다. 사용자 ID입니다. JWT에는 사용자의 Google 계정 ID, 이름, 이메일 주소 |
consent_code |
선택사항: 있는 경우 사용자가 작업이 지정된 범위에 액세스하는 데 동의했습니다. |
scope |
선택사항: 사용자에게 요청하도록 Google을 구성한 모든 범위 |
토큰 교환 엔드포인트가 연결 요청을 수신하면 다음을 수행해야 합니다. 있습니다.
JWT 어설션 검증 및 디코딩
해당 언어의 JWT 디코딩 라이브러리를 사용하여 JWT 어설션을 검증하고 디코딩할 수 있습니다. Google의 공개 키 (JWK 또는 PEM 형식)을 사용하여 토큰의 서명합니다.
JWT 어설션은 디코딩될 때 다음 예시와 같이 표시됩니다.
{ "sub": 1234567890, // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "locale": "en_US" }
토큰의 서명을 확인하는 것 외에도 어설션의 발급자가
(iss 필드)가 https://accounts.google.com이고 잠재고객 (aud 필드)
는 작업에 할당된 클라이언트 ID입니다.
Google 계정이 인증 시스템에 이미 있는지 확인
다음 조건 중 하나가 충족되는지 확인합니다.
- 어설션의
sub필드에 있는 Google 계정 ID는 사용자 데이터베이스에 있습니다. - 어설션의 이메일 주소가 사용자 데이터베이스의 사용자와 일치합니다.
두 가지 조건 중 하나라도 충족되면 사용자가 이미 가입한 것이므로 액세스할 수 있습니다.
Google 계정 ID와 이메일 주소가 어설션에 지정되지 않은 경우
데이터베이스의 사용자와 일치하면 사용자가 아직 가입하지 않은 것입니다. 이 경우
토큰 교환 엔드포인트가 error=user_not_found를 지정하는 HTTP 401 오류로 응답해야 합니다.
다음 예와 같이 됩니다.
HTTP/1.1 401 Unauthorized
Content-Type: application/json;charset=UTF-8
{
"error":"user_not_found",
}
user_not_found 오류와 함께 401 오류 응답을 수신하면
intent 매개변수의 값으로 토큰 교환 엔드포인트를 호출합니다.
create로 설정하고 사용자의 프로필 정보가 포함된 ID 토큰을 전송합니다.
요청을 전달합니다.
Google 로그인을 통한 계정 생성 처리
사용자가 서비스에서 계정을 만들어야 하는 경우 Google은
토큰을 교환 엔드포인트로
intent=create를 사용해야 합니다.
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded response_type=token&grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&scope=SCOPES&intent=create&consent_code=CONSENT_CODE&assertion=JWT[&NEW_ACCOUNT_INFO]
assertion 매개변수에는 다음을 제공하는 JSON 웹 토큰 (JWT)이 포함됩니다.
Google 사용자 ID의 서명된 어설션입니다. JWT에는
사용자의 Google 계정 ID, 이름, 이메일 주소가 포함되며 이를 사용할 수 있습니다.
을 클릭하여 서비스에 새 계정을 만드세요.
계정 생성 요청에 응답하려면 토큰 교환 엔드포인트에서 다음과 같습니다.
JWT 어설션 검증 및 디코딩
해당 언어의 JWT 디코딩 라이브러리를 사용하여 JWT 어설션을 검증하고 디코딩할 수 있습니다. Google의 공개 키 (JWK 또는 PEM 형식)을 사용하여 토큰의 서명합니다.
JWT 어설션은 디코딩될 때 다음 예시와 같이 표시됩니다.
{ "sub": 1234567890, // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "locale": "en_US" }
토큰의 서명을 확인하는 것 외에도 어설션의 발급자가
(iss 필드)가 https://accounts.google.com이고 잠재고객 (aud 필드)
는 작업에 할당된 클라이언트 ID입니다.
사용자 정보 확인 및 새 계정 만들기
다음 조건 중 하나가 충족되는지 확인합니다.
- 어설션의
sub필드에 있는 Google 계정 ID는 사용자 데이터베이스에 있습니다. - 어설션의 이메일 주소가 사용자 데이터베이스의 사용자와 일치합니다.
두 조건 중 하나라도 충족되면 사용자에게 기존 계정을 다음 계정에 연결하라는 메시지를 표시합니다.
HTTP 401 오류로 요청에 응답하고
error=linking_error 및 사용자의 이메일 주소를 login_hint로 설정합니다.
다음 예를 참고하세요.
HTTP/1.1 401 Unauthorized
Content-Type: application/json;charset=UTF-8
{
"error":"linking_error",
"login_hint":"foo@bar.com"
}
두 조건이 모두 충족되지 않는 경우 해당 정보를 사용하여 새 사용자 계정을 만듭니다. 확인할 수 있습니다 일반적으로 새 계정에는 비밀번호가 설정되지 않습니다. 그것은 사용자가 다른 플랫폼에 Google 로그인을 추가하여 애플리케이션 표면 전체에서 Google을 통해 로그인할 수 있습니다 또는 다음 작업을 수행할 수 있습니다. 사용자가 비밀번호를 설정할 수 있도록 비밀번호 복구 절차를 시작하는 링크를 다른 플랫폼에 로그인하기 위한 비밀번호
생성이 완료되면 액세스 토큰을 발급합니다. JSON 객체의 값을 반환하며 HTTP 응답의 본문을 입력하세요.
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "expires_in": SECONDS_TO_EXPIRATION }
인증 흐름 시작
계정 로그인 도우미 인텐트 사용 인증 흐름을 시작합니다.
<ph type="x-smartling-placeholder">const app = dialogflow({ // REPLACE THE PLACEHOLDER WITH THE CLIENT_ID OF YOUR ACTIONS PROJECT clientId: CLIENT_ID, }) // Intent that starts the account linking flow. app.intent('Start Signin', conv => { conv.ask(new SignIn('To get your account details')) })
private String clientId = "<your_client_id>"; @ForIntent("Start Signin") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
const app = actionssdk({ clientId: CLIENT_ID, }) app.intent('Start Signin', conv => { conv.ask(new SignIn('To get your account details')) })
private String clientId = "<your_client_id>"; @ForIntent("actions.intent.TEXT") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
데이터 액세스 요청 처리
어시스턴트 요청에 액세스 토큰이 포함된 경우, 먼저 액세스 토큰이 유효하고 만료되지 않았는지 확인한 다음 사용자 계정 데이터베이스, 토큰과 연결된 사용자 계정입니다.