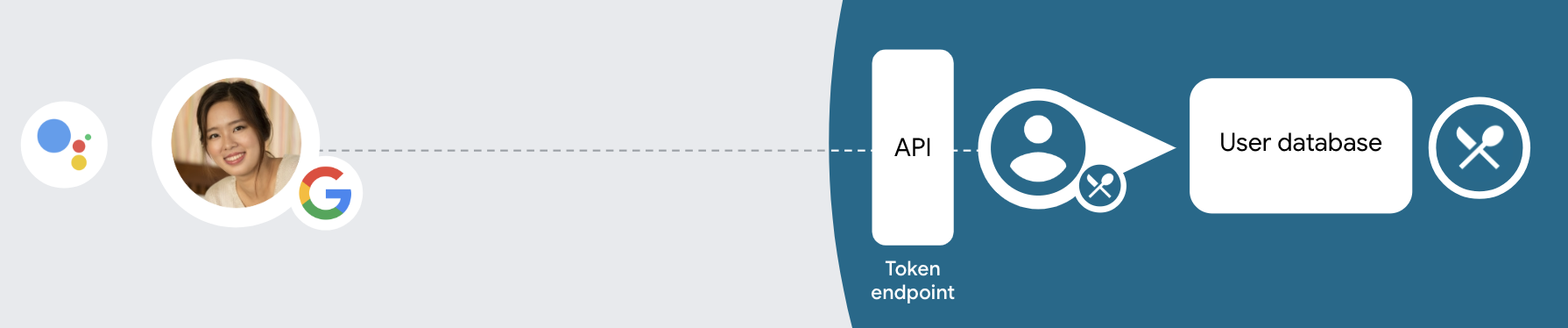
「OAuth 與 Google 登入」連結類型除了 OAuth 以外,還可以添加 Google 登入功能 帳戶連結。讓 Google 使用者能夠順暢使用語音連結 也可以為已註冊服務的使用者啟用帳戶連結 以非 Google 身分登入
這種連結類型開頭為 Google 登入,可讓您檢查 您的系統中已有 Google 個人資料。如果使用者資訊 在您的系統中找不到,將啟動標準 OAuth 流程。使用者也可以 選擇以 Google 個人資料建立新的帳戶。
如要使用 OAuth 和 Google 登入功能進行帳戶連結,請遵循下列一般做法 步驟:
- 請先徵得使用者同意,允許存取自己的 Google 個人資料。
- 使用個人資料中的資訊來辨別使用者。
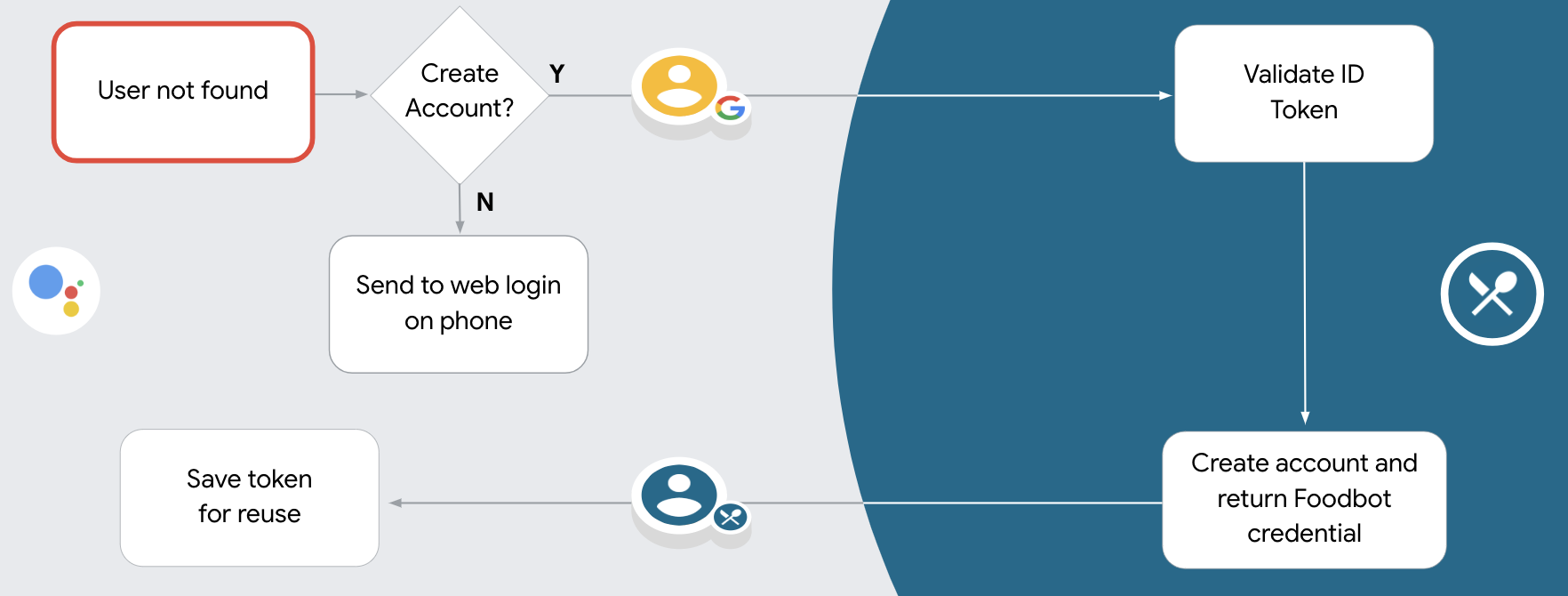
- 如果在驗證系統中找不到對應的 Google 使用者,
將如何繼續流程,取決於您是否已設定 Actions 專案
以便允許使用者透過語音建立使用者帳戶
你的網站
- 如果允許透過語音建立帳戶,請驗證身分證件 產生憑證接著,您就能根據 儲存在 ID 權杖中的設定檔資訊
- 如果您不允許透過語音建立帳戶,系統會將使用者轉移至 瀏覽器,可在其中載入您的授權頁面並完成使用者作業 建立流程
支援透過語音建立帳戶
如果您允許透過語音建立使用者帳戶,Google 助理會詢問使用者是否要 他們想要採取下列行動:
- 使用他人的 Google 帳戶資訊在您的系統中建立新帳戶,或
- 使用其他帳戶登入驗證系統 現有的非 Google 帳戶。
如果您希望盡量減少透過語音建立帳戶,建議允許透過語音建立帳戶 帳戶建立流程也會更加順暢使用者只需要離開語音流程 如果他們想使用現有的非 Google 帳戶登入。
不允許透過語音建立帳戶
如果您不允許透過語音建立使用者帳戶,Google 助理會開啟 您提供給使用者驗證的網站。如果互動是發生 使用者如果裝置沒有螢幕,Google 助理會將使用者導向手機 ,繼續進行帳戶連結流程。
在下列情況下,建議您禁止建立:
您不想開放非 Google 帳戶的使用者建立新的 使用者帳戶,並希望他們 將他們現有的使用者帳戶連結至 驗證系統。舉例來說,假設你提供會員方案 則希望確保使用者不會失去 自己在網站上累積的點數 現有帳戶。
您需要完全掌控帳戶建立流程。例如,您可以 如果需要在期間內向使用者顯示服務條款,則禁止建立 建立帳戶。
實作 OAuth 和 Google 登入帳戶連結
帳戶採用業界標準的 OAuth 2.0 流程連結。 Actions on Google 支援隱式和授權碼流程。
在隱式程式碼流程中,Google 會在使用者的瀏覽器中開啟您的授權端點。成功登入後,系統會將長期存取權杖傳回 Google。從現在起,每次透過 Google 助理傳送給您動作的要求中,都會包含這個存取權杖。
在授權碼流程中,您需要兩個端點:
- 授權端點,該端點負責將登入 UI 提供給未登入的使用者,並以簡碼授權代碼的形式,記錄使用者要求的存取權。
- 權杖交換端點,負責以下兩種交換類型:
- 交換長期更新權杖的授權碼和短期存取權杖。這項交換作業會在使用者完成帳戶連結流程時進行。
- 對短期存取權杖交換交換憑證。當 Google 需要新的存取權杖,因為更新權杖已過期時,就會發生此交換行為。
雖然隱含程式碼流程的實作方式較簡單,但 Google 建議使用隱含流程發布的存取權杖不會過期,因為若權杖與隱含流程搭配使用,就會強制使用者重新連結帳戶。如果基於安全考量而需要權杖過期,您應該考慮改用授權碼流程。
設定專案
設定專案以使用 OAuth 和 Google 登入帳戶 連結,請按照下列步驟操作:
- 開啟 Actions 主控台,然後選取您要使用的專案。
- 按一下「開發」分頁標籤,然後選擇「帳戶連結」。
- 啟用「帳戶連結」旁的切換鈕。
- 在「建立帳戶」部分中選取「是」。
在「連結類型」中選取「OAuth 與」Google 登入和隱含。
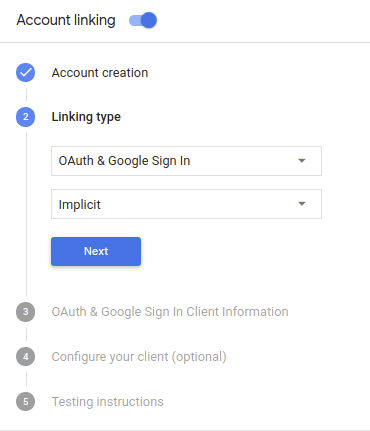
在「Client Information」中,執行下列操作:
- 指派值給「Actions to Google」核發的用戶端 ID,用來識別用戶端 ID 以及來自 Google 的要求
- 插入授權和權杖交換端點的網址。
按一下 [儲存]。
實作 OAuth 伺服器
To support the OAuth 2.0 implicit flow, your service makes an authorization endpoint available by HTTPS. This endpoint is responsible for authenticating and obtaining consent from users for data access. The authorization endpoint presents a sign-in UI to your users that aren't already signed in and records consent to the requested access.
When your Action needs to call one of your service's authorized APIs, Google uses this endpoint to get permission from your users to call these APIs on their behalf.
A typical OAuth 2.0 implicit flow session initiated by Google has the following flow:
- Google opens your authorization endpoint in the user's browser. The user signs in if not signed in already, and grants Google permission to access their data with your API if they haven't already granted permission.
- Your service creates an access token and returns it to Google by redirecting the user's browser back to Google with the access token attached to the request.
- Google calls your service's APIs, and attaches the access token with each request. Your service verifies that the access token grants Google authorization to access the API and then completes the API call.
Handle authorization requests
When your Action needs to perform account linking via an OAuth2 implicit flow, Google sends the user to your authorization endpoint with a request that includes the following parameters:
| Authorization endpoint parameters | |
|---|---|
client_id |
The client ID you assigned to Google. |
redirect_uri |
The URL to which you send the response to this request. |
state |
A bookkeeping value that is passed back to Google unchanged in the redirect URI. |
response_type |
The type of value to return in the response. For the OAuth 2.0 implicit
flow, the response type is always token. |
For example, if your authorization endpoint is available at https://myservice.example.com/auth,
a request might look like:
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token
For your authorization endpoint to handle sign-in requests, do the following steps:
Verify the
client_idandredirect_urivalues to prevent granting access to unintended or misconfigured client apps:- Confirm that the
client_idmatches the client ID you assigned to Google. - Confirm that the URL specified by the
redirect_uriparameter has the following form:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID
- Confirm that the
Check if the user is signed in to your service. If the user isn't signed in, complete your service's sign-in or sign-up flow.
Generate an access token that Google will use to access your API. The access token can be any string value, but it must uniquely represent the user and the client the token is for and must not be guessable.
Send an HTTP response that redirects the user's browser to the URL specified by the
redirect_uriparameter. Include all of the following parameters in the URL fragment:access_token: the access token you just generatedtoken_type: the stringbearerstate: the unmodified state value from the original request The following is an example of the resulting URL:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
Google's OAuth 2.0 redirect handler will receive the access token and confirm
that the state value hasn't changed. After Google has obtained an
access token for your service, Google will attach the token to subsequent calls
to your Action as part of the AppRequest.
Handle automatic linking
After the user gives your Action consent to access their Google profile, Google sends a request that contains a signed assertion of the Google user's identity. The assertion contains information that includes the user's Google Account ID, name, and email address. The token exchange endpoint configured for your project handles that request.
If the corresponding Google account is already present in your authentication system,
your token exchange endpoint returns a token for the user. If the Google account doesn't
match an existing user, your token exchange endpoint returns a user_not_found error.
The request has the following form:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&intent=get&assertion=JWT&consent_code=CONSENT_CODE&scope=SCOPES
Your token exchange endpoint must be able to handle the following parameters:
| Token endpoint parameters | |
|---|---|
grant_type |
The type of token being exchanged. For these requests, this
parameter has the value urn:ietf:params:oauth:grant-type:jwt-bearer. |
intent |
For these requests, the value of this parameter is `get`. |
assertion |
A JSON Web Token (JWT) that provides a signed assertion of the Google user's identity. The JWT contains information that includes the user's Google Account ID, name, and email address. |
consent_code |
Optional: When present, a one-time code that indicates that the user has granted consent for your Action to access the specified scopes. |
scope |
Optional: Any scopes you configured Google to request from users. |
When your token exchange endpoint receives the linking request, it should do the following:
Validate and decode the JWT assertion
You can validate and decode the JWT assertion by using a JWT-decoding library for your language. Use Google's public keys (available in JWK or PEM format) to verify the token's signature.
When decoded, the JWT assertion looks like the following example:
{ "sub": 1234567890, // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "locale": "en_US" }
In addition to verifying the token's signature, verify that the assertion's issuer
(iss field) is https://accounts.google.com and that the audience (aud field)
is the client ID assigned to your Action.
Check if the Google account is already present in your authentication system
Check whether either of the following conditions are true:
- The Google Account ID, found in the assertion's
subfield, is in your user database. - The email address in the assertion matches a user in your user database.
If either condition is true, the user has already signed up and you can issue an access token.
If neither the Google Account ID nor the email address specified in the assertion
matches a user in your database, the user hasn't signed up yet. In this case, your
token exchange endpoint should reply with a HTTP 401 error, that specifies error=user_not_found,
as in the following example:
HTTP/1.1 401 Unauthorized
Content-Type: application/json;charset=UTF-8
{
"error":"user_not_found",
}
user_not_found error, Google
calls your token exchange endpoint with the value of the intent parameter
set to create and sending an ID token that contains the user's profile information
with the request.
Handle account creation via Google Sign-In
When a user needs to create an account on your service, Google makes a
request to your token exchange endpoint that specifies
intent=create, as in the following example:
POST /token HTTP/1.1 Host: oauth2.example.com Content-Type: application/x-www-form-urlencoded response_type=token&grant_type=urn:ietf:params:oauth:grant-type:jwt-bearer&scope=SCOPES&intent=create&consent_code=CONSENT_CODE&assertion=JWT[&NEW_ACCOUNT_INFO]
The assertion parameter contains A JSON Web Token (JWT) that provides
a signed assertion of the Google user's identity. The JWT contains information
that includes the user's Google Account ID, name, and email address, which you can use
to create a new account on your service.
To respond to account creation requests, your token exchange endpoint must do the following:
Validate and decode the JWT assertion
You can validate and decode the JWT assertion by using a JWT-decoding library for your language. Use Google's public keys (available in JWK or PEM format) to verify the token's signature.
When decoded, the JWT assertion looks like the following example:
{ "sub": 1234567890, // The unique ID of the user's Google Account "iss": "https://accounts.google.com", // The assertion's issuer "aud": "123-abc.apps.googleusercontent.com", // Your server's client ID "iat": 233366400, // Unix timestamp of the assertion's creation time "exp": 233370000, // Unix timestamp of the assertion's expiration time "name": "Jan Jansen", "given_name": "Jan", "family_name": "Jansen", "email": "jan@gmail.com", // If present, the user's email address "locale": "en_US" }
In addition to verifying the token's signature, verify that the assertion's issuer
(iss field) is https://accounts.google.com and that the audience (aud field)
is the client ID assigned to your Action.
Validate user information and create new account
Check whether either of the following conditions are true:
- The Google Account ID, found in the assertion's
subfield, is in your user database. - The email address in the assertion matches a user in your user database.
If either condition is true, prompt the user to link their existing account with
their Google Account by responding to the request with an HTTP 401 error, specifying
error=linking_error and the user's email address as the login_hint, as in the
following example:
HTTP/1.1 401 Unauthorized
Content-Type: application/json;charset=UTF-8
{
"error":"linking_error",
"login_hint":"foo@bar.com"
}
If neither condition is true, create a new user account using the information provided in the JWT. New accounts do not typically have a password set. It is recommended that you add Google Sign In to other platforms to enable users to log in via Google across the surfaces of your application. Alternatively, you can email the user a link that starts your password recovery flow to allow the user to set a password for signing in on other platforms.
When the creation is completed, issue an access token and return the values in a JSON object in the body of your HTTPS response, like in the following example:
{ "token_type": "Bearer", "access_token": "ACCESS_TOKEN", "expires_in": SECONDS_TO_EXPIRATION }
啟動驗證流程
使用帳戶登入輔助意圖 以啟動驗證流程
const app = dialogflow({ // REPLACE THE PLACEHOLDER WITH THE CLIENT_ID OF YOUR ACTIONS PROJECT clientId: CLIENT_ID, }) // Intent that starts the account linking flow. app.intent('Start Signin', conv => { conv.ask(new SignIn('To get your account details')) })
private String clientId = "<your_client_id>"; @ForIntent("Start Signin") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
const app = actionssdk({ clientId: CLIENT_ID, }) app.intent('Start Signin', conv => { conv.ask(new SignIn('To get your account details')) })
private String clientId = "<your_client_id>"; @ForIntent("actions.intent.TEXT") public ActionResponse text(ActionRequest request) { ResponseBuilder rb = getResponseBuilder(request); return rb.add(new SignIn().setContext("To get your account details")).build(); }
處理資料存取要求
如果 Google 助理要求包含存取權杖, 請先檢查存取權杖是否有效且尚未過期,然後再從 使用者帳戶資料庫。

