En este documento, se explica cómo implementar la autorización de OAuth 2.0 para acceder a la API de YouTube Data con aplicaciones que se ejecutan en dispositivos como TVs, consolas de juegos y impresoras. Más específicamente, este flujo está diseñado para dispositivos que no tienen acceso a un navegador o que tienen capacidades de entrada limitadas.
OAuth 2.0 permite que los usuarios compartan datos específicos con una aplicación y, al mismo tiempo, mantengan la privacidad de sus nombres de usuario, contraseñas y otra información. Por ejemplo, una aplicación para TV podría usar OAuth 2.0 para obtener permiso para seleccionar un archivo almacenado en Google Drive.
Dado que las aplicaciones que usan este flujo se distribuyen a dispositivos individuales, se supone que las apps no pueden mantener secretos. Pueden acceder a las APIs de Google mientras el usuario está presente en la app o cuando esta se ejecuta en segundo plano.
Alternativas
Si escribes una app para una plataforma como Android, iOS, macOS, Linux o Windows (incluida la Plataforma universal de Windows), que tiene acceso al navegador y a todas las capacidades de entrada, usa el flujo de OAuth 2.0 para aplicaciones para dispositivos móviles y computadoras. (Debes usar ese flujo incluso si tu app es una herramienta de línea de comandos sin interfaz gráfica).
Si solo quieres acceder a la cuenta de Google de los usuarios y usar el token de ID de JWT para obtener información básica del perfil del usuario, consulta Acceso en TVs y dispositivos de entrada limitada.
Requisitos previos
Habilita las API para tu proyecto.
Cualquier aplicación que llame a las APIs de Google debe habilitarlas en la Consola de APIs.
Para habilitar una API en tu proyecto, sigue estos pasos:
- Abre la Biblioteca de APIs en la Consola de APIs de Google.
- Si se te solicita, selecciona un proyecto o crea uno nuevo.
- Usa la página Biblioteca para buscar y habilitar la API de YouTube Data. Busca otras APIs que usará tu aplicación y habilítalas también.
Crea credenciales de autorización
Todas las aplicaciones que usan OAuth 2.0 para acceder a las APIs de Google deben tener credenciales de autorización que identifiquen la aplicación en el servidor OAuth 2.0 de Google. En los siguientes pasos, se explica cómo crear credenciales para tu proyecto. Luego, tus aplicaciones pueden usar las credenciales para acceder a las APIs que habilitaste para ese proyecto.
- Ve a la página Clientes.
- Haz clic en Crear cliente.
- Selecciona el tipo de aplicación TVs and Limited Input devices.
- Asigna un nombre a tu cliente de OAuth 2.0 y haz clic en Crear.
Identifica los permisos de acceso
Los permisos permiten que tu aplicación solo solicite acceso a los recursos que necesita, al tiempo que permiten a los usuarios controlar el nivel de acceso que otorgan a tu aplicación. Por lo tanto, puede haber una relación inversa entre la cantidad de permisos solicitados y la probabilidad de obtener el consentimiento del usuario.
Antes de que comiences a implementar la autorización de OAuth 2.0, te recomendamos identificar los permisos a los que tu app necesitará acceder.
La versión 3 de la API de YouTube Data usa los siguientes alcances:
| Alcance | Descripción |
|---|---|
https://www. |
Administrar tu cuenta de YouTube |
https://www. |
Ver una lista de los miembros actuales y activos de su canal, su nivel actual y el momento en que se hicieron miembros |
https://www. |
Vea, edite y borre de forma permanente sus videos, calificaciones, comentarios y subtítulos de YouTube |
https://www. |
Permite ver tu cuenta de YouTube. |
https://www. |
Permite administrar tus videos de YouTube. |
https://www. |
Ver y administrar sus elementos y el contenido asociado en YouTube |
https://www. |
Ver información privada de tu canal de YouTube que sea relevante durante el proceso de auditoría con un socio de YouTube |
Consulta la lista de permisos permitidos para las apps o los dispositivos instalados.
Obtén tokens de acceso de OAuth 2.0
Aunque tu aplicación se ejecute en un dispositivo con capacidades de entrada limitadas, los usuarios deben tener acceso independiente a un dispositivo con capacidades de entrada más completas para completar este flujo de autorización. El flujo tiene los siguientes pasos:
- Tu aplicación envía una solicitud al servidor de autorización de Google que identifica los alcances a los que tu aplicación solicitará permiso para acceder.
- El servidor responde con varios fragmentos de información que se usan en pasos posteriores, como un código de dispositivo y un código de usuario.
- Muestras información que el usuario puede ingresar en un dispositivo aparte para autorizar tu app.
- Tu aplicación comienza a sondear el servidor de autorización de Google para determinar si el usuario autorizó tu app.
- El usuario cambia a un dispositivo con capacidades de entrada más completas, inicia un navegador web, navega a la URL que se muestra en el paso 3 y, luego, ingresa un código que también se muestra en el paso 3. Luego, el usuario puede otorgar (o denegar) el acceso a tu aplicación.
- La próxima respuesta a tu solicitud de sondeo contendrá los tokens que tu app necesita para autorizar solicitudes en nombre del usuario. (Si el usuario rechazó el acceso a tu aplicación, la respuesta no contiene tokens).
La imagen ilustra este proceso:
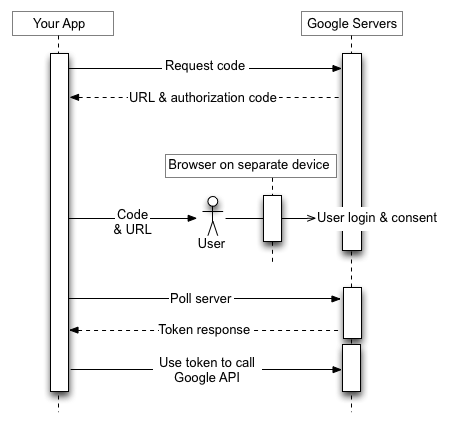
En las siguientes secciones, se explican estos pasos en detalle. Dado el rango de capacidades y entornos de ejecución que pueden tener los dispositivos, los ejemplos que se muestran en este documento usan la utilidad de línea de comandos curl. Estos ejemplos se pueden portar a varios lenguajes y tiempos de ejecución.
Paso 1: Solicita códigos de dispositivo y de usuario
En este paso, tu dispositivo envía una solicitud HTTP POST al servidor de autorización de Google, en https://oauth2.googleapis.com/device/code, que identifica tu aplicación y los alcances de acceso a los que tu aplicación quiere acceder en nombre del usuario.
Debes recuperar esta URL del documento de descubrimiento con el valor de metadatos device_authorization_endpoint. Incluye los siguientes parámetros de solicitud HTTP:
| Parámetros | |||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
client_id |
Obligatorio
Es el ID de cliente de tu aplicación. Puedes encontrar este valor en la página Clientes de la consola de Cloud. |
||||||||||||||||
scope |
Obligatorio
Lista de alcances separados por espacios que identifican los recursos a los que tu aplicación podría acceder en nombre del usuario. Estos valores informan a la pantalla de consentimiento que Google muestra al usuario. Consulta la lista de permisos permitidos para las apps o los dispositivos instalados. Los permisos permiten que tu aplicación solo solicite acceso a los recursos que necesita, al tiempo que permiten a los usuarios controlar el nivel de acceso que otorgan a tu aplicación. Por lo tanto, existe una relación inversa entre la cantidad de permisos solicitados y la probabilidad de obtener el consentimiento del usuario. La versión 3 de la API de YouTube Data usa los siguientes alcances:
En el documento Permisos de la API de OAuth 2.0, se proporciona una lista completa de los permisos que puedes usar para acceder a las APIs de Google. |
||||||||||||||||
Ejemplos
En el siguiente fragmento, se muestra una solicitud de ejemplo:
POST /device/code HTTP/1.1 Host: oauth2.googleapis.com Content-Type: application/x-www-form-urlencoded client_id=client_id&scope=https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fyoutube.force-ssl
En este ejemplo, se muestra un comando curl para enviar la misma solicitud:
curl -d "client_id=client_id&scope=https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fyoutube.force-ssl" \
https://oauth2.googleapis.com/device/code
Paso 2: Controla la respuesta del servidor de autorización
El servidor de autorización devolverá una de las siguientes respuestas:
Respuesta de éxito
Si la solicitud es válida, tu respuesta será un objeto JSON que contendrá las siguientes propiedades:
| Propiedades | |
|---|---|
device_code |
Es un valor que Google asigna de forma única para identificar el dispositivo que ejecuta la app que solicita autorización. El usuario autorizará ese dispositivo desde otro dispositivo con capacidades de entrada más enriquecidas. Por ejemplo, un usuario puede usar una laptop o un teléfono celular para autorizar una app que se ejecuta en una TV. En este caso, el device_code identifica la TV.
Este código permite que el dispositivo que ejecuta la app determine de forma segura si el usuario otorgó o denegó el acceso. |
expires_in |
Es la cantidad de tiempo, en segundos, durante la cual son válidos los parámetros device_code y user_code. Si, en ese tiempo, el usuario no completa el
flujo de autorización y tu dispositivo tampoco sondea para recuperar información sobre la
decisión del usuario, es posible que debas reiniciar este proceso desde el paso 1. |
interval |
Es el tiempo, en segundos, que tu dispositivo debe esperar entre las solicitudes de sondeo. Por ejemplo, si el valor es 5, tu dispositivo debe enviar una solicitud de sondeo al servidor de autorización de Google cada cinco segundos. Consulta el paso 3 para obtener más detalles. |
user_code |
Es un valor que distingue mayúsculas de minúsculas y que identifica ante Google los alcances a los que la aplicación solicita acceso. Tu interfaz de usuario le indicará al usuario que ingrese este valor en un dispositivo independiente con capacidades de entrada más completas. Luego, Google usa el valor para mostrar el conjunto correcto de permisos cuando le solicita al usuario que otorgue acceso a tu aplicación. |
verification_url |
Es una URL a la que el usuario debe navegar en un dispositivo independiente para ingresar el user_code y otorgar o rechazar el acceso a tu aplicación. Tu interfaz de usuario también mostrará este valor. |
En el siguiente fragmento, se muestra una respuesta de ejemplo:
{ "device_code": "4/4-GMMhmHCXhWEzkobqIHGG_EnNYYsAkukHspeYUk9E8", "user_code": "GQVQ-JKEC", "verification_url": "https://www.google.com/device", "expires_in": 1800, "interval": 5 }
Respuesta de cuota excedida
Si tus solicitudes de código del dispositivo superaron la cuota asociada a tu ID de cliente, recibirás una respuesta 403 que contiene el siguiente error:
{ "error_code": "rate_limit_exceeded" }
En ese caso, usa una estrategia de retirada para reducir la frecuencia de las solicitudes.
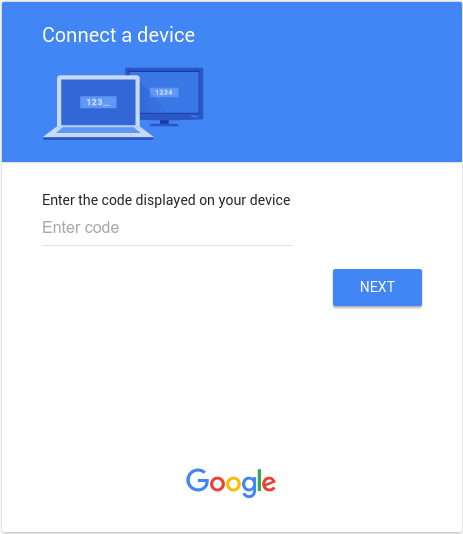
Paso 3: Muestra el código del usuario
Mostrar al usuario los valores de verification_url y user_code obtenidos en el paso 2 Ambos valores pueden contener cualquier carácter imprimible del conjunto de caracteres US-ASCII. El contenido que le muestres al usuario debe indicarle que navegue a verification_url en un dispositivo aparte y que ingrese el código user_code.
Diseña tu interfaz de usuario (IU) teniendo en cuenta las siguientes reglas:
user_code- El
user_codese debe mostrar en un campo que pueda controlar 15 caracteres de tamaño "W". En otras palabras, si puedes mostrar el códigoWWWWWWWWWWWWWWWcorrectamente, tu IU es válida y te recomendamos que uses ese valor de cadena cuando pruebes la forma en que se muestrauser_codeen tu IU. - El parámetro
user_codedistingue mayúsculas de minúsculas y no se debe modificar de ninguna manera, por ejemplo, cambiando las mayúsculas o minúsculas, o insertando otros caracteres de formato.
- El
verification_url- El espacio en el que muestras el
verification_urldebe ser lo suficientemente ancho como para admitir una cadena de URL de 40 caracteres. - No debes modificar el
verification_urlde ninguna manera, excepto para quitar de forma opcional el esquema para su visualización. Si planeas quitar el esquema (p.ej.,https://) de la URL por motivos de visualización, asegúrate de que tu app pueda controlar las varianteshttpyhttps.
- El espacio en el que muestras el
Paso 4: Sondea el servidor de autorización de Google
Dado que el usuario usará un dispositivo independiente para navegar al verification_url y otorgar (o denegar) el acceso, el dispositivo solicitante no recibe una notificación automática cuando el usuario responde a la solicitud de acceso. Por ese motivo, el dispositivo solicitante debe sondear el servidor de autorización de Google para determinar cuándo respondió el usuario a la solicitud.
El dispositivo solicitante debe seguir enviando solicitudes de sondeo hasta que reciba una respuesta que indique que el usuario respondió a la solicitud de acceso o hasta que venzan los parámetros device_code y user_code obtenidos en el
paso 2. El interval que se devolvió en el paso 2 especifica la cantidad de tiempo, en segundos, que se debe esperar entre las solicitudes.
La URL del extremo que se debe sondear es https://oauth2.googleapis.com/token. La solicitud de sondeo contiene los siguientes parámetros:
| Parámetros | |
|---|---|
client_id |
Es el ID de cliente de tu aplicación. Puedes encontrar este valor en la página Clientes de la consola de Cloud. |
client_secret |
Es el secreto del cliente para el client_id proporcionado. Puedes encontrar este valor en la
página Clientes
de la consola de Cloud. |
device_code |
El device_code que devolvió el servidor de autorización en el paso 2. |
grant_type |
Configura este valor en urn:ietf:params:oauth:grant-type:device_code. |
Ejemplos
En el siguiente fragmento, se muestra una solicitud de ejemplo:
POST /token HTTP/1.1 Host: oauth2.googleapis.com Content-Type: application/x-www-form-urlencoded client_id=client_id& client_secret=client_secret& device_code=device_code& grant_type=urn%3Aietf%3Aparams%3Aoauth%3Agrant-type%3Adevice_code
En este ejemplo, se muestra un comando curl para enviar la misma solicitud:
curl -d "client_id=client_id&client_secret=client_secret& \
device_code=device_code& \
grant_type=urn%3Aietf%3Aparams%3Aoauth%3Agrant-type%3Adevice_code" \
-H "Content-Type: application/x-www-form-urlencoded" \
https://oauth2.googleapis.com/tokenPaso 5: El usuario responde a la solicitud de acceso
En la siguiente imagen, se muestra una página similar a la que ven los usuarios cuando navegan al elemento verification_url que mostraste en el paso 3:
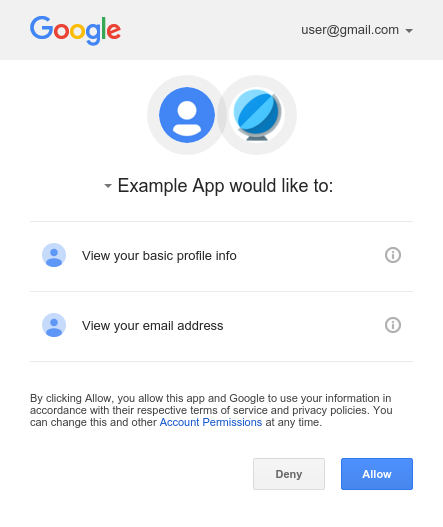
Después de ingresar el user_code y, si aún no accedió, acceder a Google, el usuario verá una pantalla de consentimiento:
Paso 6: Controla las respuestas a las solicitudes de sondeo
El servidor de autorización de Google responde a cada solicitud de sondeo con una de las siguientes respuestas:
Acceso otorgado
Si el usuario otorgó acceso al dispositivo (haciendo clic en Allow en la pantalla de consentimiento), la respuesta contendrá un token de acceso y un token de actualización. Los tokens permiten que tu dispositivo acceda a las APIs de Google en nombre del usuario. (La propiedad scope de la respuesta determina a qué APIs puede acceder el dispositivo).
En este caso, la respuesta de la API contiene los siguientes campos:
| Campos | |
|---|---|
access_token |
Es el token que envía tu aplicación para autorizar una solicitud a la API de Google. |
expires_in |
Es la vida útil restante del token de acceso en segundos. |
refresh_token |
Es un token que puedes usar para obtener un token de acceso nuevo. Los tokens de actualización son válidos hasta que el usuario revoca el acceso o hasta que vencen. Ten en cuenta que los tokens de actualización siempre se devuelven para los dispositivos. |
scope |
Permisos de acceso otorgados por el access_token, expresados como una lista de cadenas sensibles a mayúsculas y minúsculas delimitadas por espacios. |
token_type |
Es el tipo de token que se devuelve. Este valor siempre es Bearer. |
En el siguiente fragmento, se muestra una respuesta de ejemplo:
{ "access_token": "1/fFAGRNJru1FTz70BzhT3Zg", "expires_in": 3920, "scope": "openid https://www.googleapis.com/auth/userinfo.profile https://www.googleapis.com/auth/userinfo.email", "token_type": "Bearer", "refresh_token": "1/xEoDL4iW3cxlI7yDbSRFYNG01kVKM2C-259HOF2aQbI" }
Los tokens de acceso tienen una vida útil limitada. Si tu aplicación necesita acceder a una API durante un período prolongado, puede usar el token de actualización para obtener un token de acceso nuevo. Si tu aplicación necesita este tipo de acceso, debe almacenar el token de actualización para usarlo más adelante.
Acceso denegado
Si el usuario se niega a otorgar acceso al dispositivo, la respuesta del servidor tendrá un código de estado de respuesta HTTP 403 (Forbidden). La respuesta contiene el siguiente error:
{ "error": "access_denied", "error_description": "Forbidden" }
Autorización pendiente
Si el usuario aún no completó el flujo de autorización, el servidor devuelve un código de estado de respuesta HTTP 428 (Precondition Required). La respuesta contiene el siguiente error:
{ "error": "authorization_pending", "error_description": "Precondition Required" }
Realiza sondeos con demasiada frecuencia
Si el dispositivo envía solicitudes de sondeo con demasiada frecuencia, el servidor devuelve un código de estado de respuesta HTTP 403 (Forbidden). La respuesta contiene el siguiente error:
{ "error": "slow_down", "error_description": "Forbidden" }
Otros errores
El servidor de autorización también devuelve errores si la solicitud de sondeo no incluye los parámetros obligatorios o tiene un valor de parámetro incorrecto. Estas solicitudes suelen tener un código de estado de respuesta HTTP 400 (Bad Request) o 401 (Unauthorized). Estos errores incluyen lo siguiente:
| Error | Código de estado HTTP | Descripción |
|---|---|---|
admin_policy_enforced |
400 |
La Cuenta de Google no puede autorizar uno o más permisos solicitados debido a las políticas de su administrador de Google Workspace. Consulta el artículo de ayuda para administradores de Google Workspace Controla qué apps internas y de terceros acceden a los datos de Google Workspace para obtener más información sobre cómo un administrador puede restringir el acceso a los permisos hasta que se otorgue explícitamente el acceso a tu ID de cliente de OAuth. |
invalid_client |
401 |
No se encontró el cliente de OAuth. Por ejemplo, este error se produce si el valor del parámetro El tipo de cliente de OAuth es incorrecto. Asegúrate de que el tipo de aplicación para el ID de cliente esté establecido en TVs y dispositivos de entrada limitada. |
invalid_grant |
400 |
El valor del parámetro code no es válido, ya se reclamó o no se puede analizar. |
unsupported_grant_type |
400 |
El valor del parámetro grant_type no es válido. |
org_internal |
403 |
El ID de cliente de OAuth de la solicitud forma parte de un proyecto que limita el acceso a las Cuentas de Google en una organización de Google Cloud específica. Confirma la configuración del tipo de usuario para tu aplicación de OAuth. |
Llama a las APIs de Google
Después de que tu aplicación obtiene un token de acceso, puedes usarlo para realizar llamadas a una API de Google en nombre de una cuenta de usuario determinada si se otorgaron los permisos de acceso requeridos por la API. Para ello, incluye el token de acceso en una solicitud a la API con un parámetro de consulta access_token o un valor Bearer del encabezado HTTP Authorization. Cuando sea posible, se recomienda usar el encabezado HTTP, ya que las cadenas de consulta suelen ser visibles en los registros del servidor. En la mayoría de los casos, puedes usar una biblioteca cliente para configurar tus llamadas a las APIs de Google (por ejemplo, cuando llamas a la API de YouTube Live Streaming).
Ten en cuenta que la API de YouTube en vivo no admite el flujo de cuentas de servicio. Dado que no hay forma de vincular una cuenta de servicio a una cuenta de YouTube, los intentos de autorizar solicitudes con este flujo generarán un error NoLinkedYouTubeAccount.
Puedes probar todas las APIs de Google y ver sus permisos en OAuth 2.0 Playground.
Ejemplos de HTTP GET
Una llamada al endpoint
liveBroadcasts.list (la API de YouTube en vivo) con el encabezado HTTP Authorization: Bearer podría verse de la siguiente manera. Ten en cuenta que debes especificar tu propio token de acceso:
GET /youtube/v3/liveBroadcasts?part=id%2Csnippet&mine=true HTTP/1.1 Host: www.googleapis.com Authorization: Bearer access_token
Esta es una llamada a la misma API para el usuario autenticado con el parámetro de cadena de consulta access_token:
GET https://www.googleapis.com/youtube/v3/liveBroadcasts?access_token=access_token&part=id%2Csnippet&mine=true
Ejemplos de curl
Puedes probar estos comandos con la aplicación de línea de comandos de curl. A continuación, se muestra un ejemplo que usa la opción de encabezado HTTP (preferida):
curl -H "Authorization: Bearer access_token" https://www.googleapis.com/youtube/v3/liveBroadcasts?part=id%2Csnippet&mine=true
O, de forma alternativa, la opción del parámetro de cadena de consulta:
curl https://www.googleapis.com/youtube/v3/liveBroadcasts?access_token=access_token&part=id%2Csnippet&mine=true
Actualización de un token de acceso
Los tokens de acceso vencen periódicamente y se convierten en credenciales no válidas para una solicitud a la API relacionada. Puedes actualizar un token de acceso sin solicitarle permiso al usuario (incluso cuando el usuario no está presente) si solicitaste acceso sin conexión a los alcances asociados con el token.
Para actualizar un token de acceso, tu aplicación envía una solicitud POST HTTPS al servidor de autorización de Google (https://oauth2.googleapis.com/token) que incluye los siguientes parámetros en el cuerpo de la solicitud:
| Nombre | Valor |
|---|---|
client_id |
Es el ID de cliente que se obtuvo de la Consola de APIs. |
client_secret |
Opcional
Es el secreto de cliente que se obtuvo de la Consola de APIs. |
grant_type |
Como se define en la especificación de OAuth 2.0, el valor de este campo debe establecerse en refresh_token. |
refresh_token |
Es el token de actualización que se devuelve del intercambio del código de autorización. |
En el siguiente fragmento, se muestra una solicitud de ejemplo:
POST /token HTTP/1.1 Host: oauth2.googleapis.com Content-Type: application/x-www-form-urlencoded client_id=your_client_id& refresh_token=refresh_token& grant_type=refresh_token
Siempre que el usuario no haya revocado el acceso otorgado a la aplicación, el servidor de tokens devolverá un objeto JSON que contiene un nuevo token de acceso. En el siguiente fragmento, se muestra una respuesta de ejemplo:
{ "access_token": "1/fFAGRNJru1FTz70BzhT3Zg", "expires_in": 3920, "scope": "https://www.googleapis.com/auth/youtube.force-ssl https://www.googleapis.com/auth/calendar.readonly", "token_type": "Bearer" }
Ten en cuenta que hay límites en la cantidad de tokens de actualización que se emitirán: un límite por combinación de cliente y usuario, y otro por usuario en todos los clientes. Debes guardar los tokens de actualización en un almacenamiento a largo plazo y seguir usándolos mientras sigan siendo válidos. Si tu aplicación solicita demasiados tokens de actualización, es posible que alcance estos límites, en cuyo caso los tokens de actualización más antiguos dejarán de funcionar.
Revocación de tokens
En algunos casos, es posible que un usuario desee revocar el acceso que le otorgó a una aplicación. Para revocar el acceso, el usuario debe visitar la configuración de la cuenta. Consulta la sección para quitar el acceso de sitios o apps del documento de asistencia Sitios y apps de terceros con acceso a tu cuenta para obtener más información.
También es posible que una aplicación revoque de forma programática el acceso que se le otorgó. La revocación programática es importante en los casos en que un usuario cancela la suscripción, quita una aplicación o los recursos de la API que requiere una app cambiaron significativamente. En otras palabras, parte del proceso de eliminación puede incluir una solicitud a la API para garantizar que se quiten los permisos que se otorgaron anteriormente a la aplicación.
Para revocar un token de forma programática, tu aplicación realiza una solicitud a https://oauth2.googleapis.com/revoke y, luego, incluye el token como parámetro:
curl -d -X -POST --header "Content-type:application/x-www-form-urlencoded" \
https://oauth2.googleapis.com/revoke?token={token}El token puede ser un token de acceso o un token de actualización. Si el token es un token de acceso y tiene un token de actualización correspondiente, también se revocará el token de actualización.
Si la revocación se procesa correctamente, el código de estado HTTP de la respuesta será 200. En caso de error, se muestra un código de estado HTTP 400 junto con un código de error.
Permisos aceptados
El flujo de OAuth 2.0 para dispositivos solo se admite para los siguientes permisos:
OpenID Connect, Acceso con Google
emailopenidprofile
API de Drive
https://www.googleapis.com/auth/drive.appdatahttps://www.googleapis.com/auth/drive.file
APIs de YouTube
https://www.googleapis.com/auth/youtubehttps://www.googleapis.com/auth/youtube.readonly
Acceso basado en el tiempo
El acceso basado en el tiempo permite que un usuario le otorgue a tu app acceso a sus datos durante un período limitado para completar una acción. El acceso basado en el tiempo está disponible en algunos productos de Google durante el flujo de consentimiento, lo que les brinda a los usuarios la opción de otorgar acceso por un período limitado. Un ejemplo es la API de Data Portability, que permite una transferencia única de datos.
Cuando un usuario otorga a tu aplicación acceso basado en el tiempo, el token de actualización vencerá después de la duración especificada. Ten en cuenta que los tokens de actualización pueden invalidarse antes en circunstancias específicas. Consulta estos casos para obtener más detalles. El campo refresh_token_expires_in que se devuelve en la respuesta del intercambio de códigos de autorización representa el tiempo restante hasta que venza el token de actualización en esos casos.
Implementa la Protección integral de la cuenta
Un paso adicional que debes seguir para proteger las cuentas de tus usuarios es implementar la Protección integral de la cuenta utilizando el servicio de Protección integral de la cuenta de Google. Este servicio te permite suscribirte a las notificaciones de eventos de seguridad, que proporcionan información a tu aplicación sobre los cambios importantes en la cuenta del usuario. Luego, puedes usar la información para tomar medidas según cómo decidas responder a los eventos.
Estos son algunos ejemplos de los tipos de eventos que el Servicio de Protección integral de la cuenta de Google envía a tu app:
-
https://schemas.openid.net/secevent/risc/event-type/sessions-revoked -
https://schemas.openid.net/secevent/oauth/event-type/token-revoked -
https://schemas.openid.net/secevent/risc/event-type/account-disabled
Consulta la página Protección de cuentas de usuario con la Protección integral de la cuenta para obtener más información sobre cómo implementar la Protección integral de la cuenta y ver la lista completa de eventos disponibles.
