סקירה כללית
כניסה באמצעות חשבון Google מבוססת-OAuth עם קישור יעיל מוסיפה כניסה באמצעות חשבון Google על גבי קישור OAuth. הקישור הזה מאפשר למשתמשי Google ליהנות מחוויית קישור חלקה, וגם ליצור חשבון חדש בשירות שלכם באמצעות חשבון Google שלהם.
כדי לבצע קישור חשבונות באמצעות OAuth ו'כניסה באמצעות חשבון Google', פועלים לפי השלבים הכלליים הבאים:
- קודם כל, צריך לבקש מהמשתמש לתת הסכמה לגישה לפרופיל ב-Google.
- משתמשים במידע בפרופיל כדי לבדוק אם חשבון המשתמש קיים.
- למשתמשים קיימים, מקשרים את החשבונות.
- אם לא מצאתם התאמה למשתמש Google במערכת האימות שלכם, צריך לאמת את אסימון הזהות שהתקבל מ-Google. לאחר מכן תוכלו ליצור משתמש על סמך פרטי הפרופיל שכלולים באסימון המזהה.
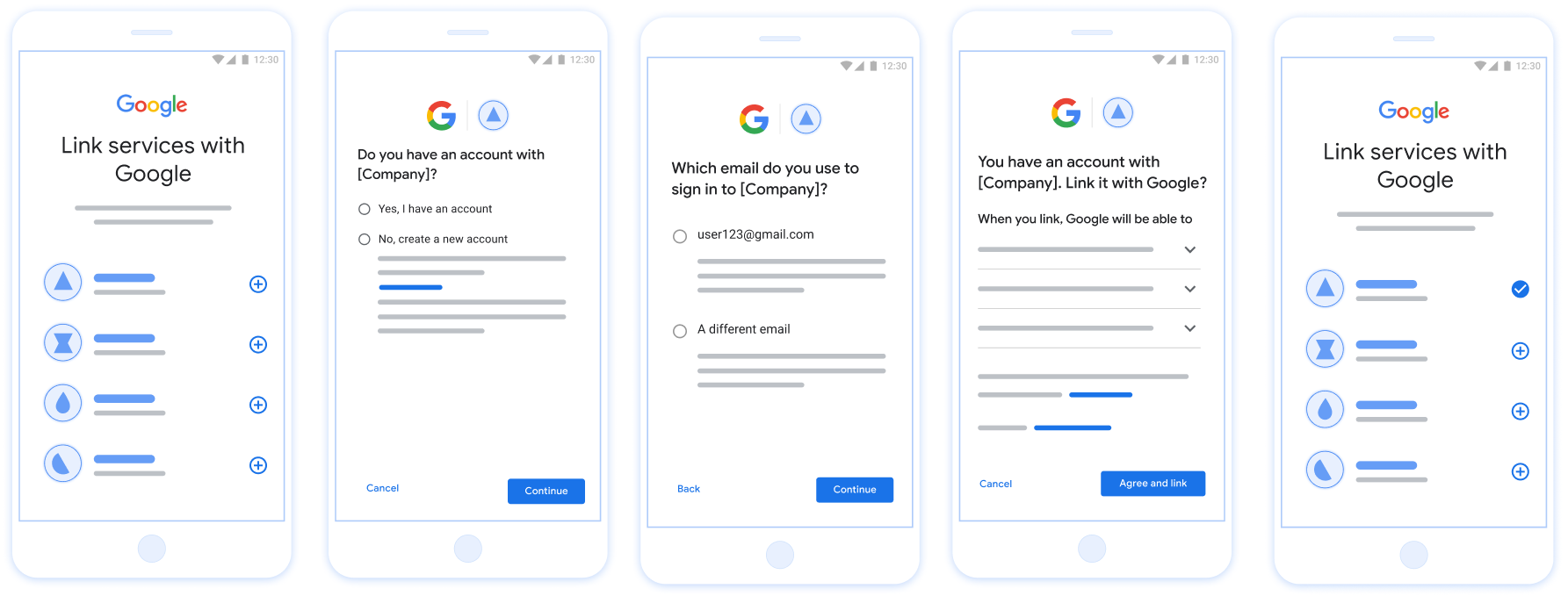
איור 1. קישור חשבון בטלפון של משתמש באמצעות קישור פשוט
קישור יעיל: תהליך OAuth + כניסה באמצעות חשבון Google
תרשים הרצף הבא מציג את האינטראקציות בין המשתמש, Google ונקודת הקצה של חילופי הטוקנים שלכם לקישור פשוט.
תפקידים ותחומי אחריות
בטבלה הבאה מוגדרים התפקידים ותחומי האחריות של הגורמים בתהליך המקוצר של קישור החשבונות.
| המשתמש / הרכיב | תפקיד ב-GAL | תחומי אחריות |
|---|---|---|
| אפליקציית Google / שרת | לקוח OAuth | מקבל את הסכמת המשתמש לכניסה באמצעות חשבון Google, מעביר הצהרות זהות (JWT) לשרת שלכם ושומר בצורה מאובטחת את הטוקנים שנוצרו. |
| נקודת הקצה של חילופי הטוקנים | ספק זהויות / שרת הרשאות | מאמת את הצהרות הזהות, בודק אם יש חשבונות קיימים, מטפל בכוונות לקישור חשבונות (check, get, create) ומנפיק טוקנים על סמך הכוונות המבוקשות. |
| Your Service API | שרת משאבים | מאפשר גישה לנתוני משתמש כשמוצג אסימון גישה תקין. |
הדרישות לקישור פשוט
- מטמיעים את תהליך הקישור הבסיסי באמצעות OAuth. השירות שלכם צריך לתמוך בנקודות קצה של הרשאה והחלפת אסימונים שתואמות ל-OAuth 2.0.
- נקודת הקצה של החלפת האסימונים חייבת לתמוך בהצהרות של JSON Web Token (JWT) וליישם את הכוונות
check,createו-get.
לוגיקה של החלטות לקישור יעיל
הלוגיקה הבאה קובעת איך מתבצעות קריאות לכוונות במהלך תהליך הקישור הפשוט:
- האם למשתמש יש חשבון במערכת האימות שלכם? (המשתמש מחליט על ידי בחירה באפשרות 'כן' או 'לא')
- כן : המשתמש משתמש בכתובת האימייל שמשויכת לחשבון Google שלו כדי להיכנס לפלטפורמה שלכם. (המשתמש מחליט על ידי בחירה באפשרות 'כן' או 'לא')
- כן : האם למשתמש יש חשבון תואם במערכת האימות שלכם? (מתקשרים אל
check intentכדי לאשר)- YES : מתקשרים אל
get intentוהחשבון מקושר אם הכוונה מוחזרת בהצלחה. - לא : ליצור חשבון חדש? (המשתמש מחליט על ידי בחירה באפשרות 'כן' או 'לא')
- כן : מתבצעת קריאה אל
create intentוהחשבון מקושר אם כוונת היצירה מוחזרת בהצלחה. - לא : תהליך הקישור באמצעות OAuth מופעל, המשתמש מועבר לדפדפן שלו ומוצגת לו האפשרות לקשר עם כתובת אימייל אחרת.
- כן : מתבצעת קריאה אל
- YES : מתקשרים אל
- לא : מופעל תהליך הקישור באמצעות OAuth, המשתמש מועבר לדפדפן שלו ומוצגת לו האפשרות לקשר עם כתובת אימייל אחרת.
- כן : האם למשתמש יש חשבון תואם במערכת האימות שלכם? (מתקשרים אל
- לא : האם למשתמש יש חשבון תואם במערכת האימות שלך? (מתקשרים אל
check intentכדי לאשר)- YES : מתקשרים אל
get intentוהחשבון מקושר אם הכוונה מוחזרת בהצלחה. - לא : מתבצעת קריאה אל
create intentוהחשבון מקושר אם הכוונה ליצור חוזרת בהצלחה.
- YES : מתקשרים אל
- כן : המשתמש משתמש בכתובת האימייל שמשויכת לחשבון Google שלו כדי להיכנס לפלטפורמה שלכם. (המשתמש מחליט על ידי בחירה באפשרות 'כן' או 'לא')
מתכון להטמעה
נקודת הקצה של חילופי הטוקנים צריכה להטמיע את ה-Intents check, get ו-create כדי לתמוך בקישור פשוט.
כדי לטפל בכוונות השונות:
בדיקה אם קיים חשבון משתמש (בדיקת כוונות)
Google מתקשרת לנקודת הקצה של החלפת האסימונים כדי לוודא שהמשתמש ב-Google קיים במערכת שלכם. פרטים על הפרמטרים זמינים במאמר בנושא הפעלת כוונות מקושרות.
מתכון להטמעה
כדי לטפל בכוונת המשתמש check, מבצעים את הפעולות הבאות:
אימות הבקשה:
- אימות של
client_id,client_secretו-grant_type(חייב להיותurn:ietf:params:oauth:grant-type:jwt-bearer). - מאמתים את
assertion(JWT) באמצעות הקריטריונים שמפורטים במאמר אימות JWT.
- אימות של
חיפוש משתמש:
- בודקים אם מזהה חשבון Google (
sub) או כתובת האימייל ב-JWT תואמים למשתמש במסד הנתונים.
- בודקים אם מזהה חשבון Google (
שליחת תשובה:
- אם נמצא: מחזירים HTTP
200 OKעם{"account_found": "true"}. - אם הקובץ לא נמצא: מחזירים HTTP
404 Not Foundעם{"account_found": "false"}.
- אם נמצא: מחזירים HTTP
טיפול בקישור אוטומטי (קבלת כוונת רכישה)
אם החשבון קיים, Google מתקשרת לנקודת הקצה עם intent=get כדי לאחזר טוקנים. פרטים על הפרמטרים זמינים במאמר בנושא הפעלת כוונות מקושרות.
מתכון להטמעה
כדי לטפל בכוונת המשתמש get, מבצעים את הפעולות הבאות:
אימות הבקשה:
- מאמתים את
client_id,client_secretוgrant_type. - מאמתים את
assertion(JWT).
- מאמתים את
חיפוש משתמש:
- מוודאים שהמשתמש קיים באמצעות הטענה
subאוemail.
- מוודאים שהמשתמש קיים באמצעות הטענה
שליחת תשובה:
- אם הפעולה הצליחה: ייווצרו ויוחזרו הערכים
access_token,refresh_tokenו-expires_inבתגובת JSON (HTTP200 OK). - אם הקישור נכשל: מחזירים HTTP
401 Unauthorizedעם{"error": "linking_error"}ואפשרותlogin_hintכדי לחזור לקישור OAuth רגיל.
- אם הפעולה הצליחה: ייווצרו ויוחזרו הערכים
טיפול ביצירת חשבון באמצעות "כניסה באמצעות חשבון Google" (יצירת כוונה)
אם לא קיים חשבון, Google מתקשרת לנקודת הקצה עם intent=create כדי ליצור משתמש חדש. פרטים על הפרמטרים זמינים במאמר בנושא הפעלת כוונות מקושרות.
מתכון להטמעה
כדי לטפל בכוונת המשתמש create, מבצעים את הפעולות הבאות:
אימות הבקשה:
- מאמתים את
client_id,client_secretוgrant_type. - מאמתים את
assertion(JWT).
- מאמתים את
מוודאים שהמשתמש לא קיים:
- בודקים אם
subאוemailכבר נמצאים במסד הנתונים. - אם המשתמש קיים: מחזירים HTTP
401 Unauthorizedעם{"error": "linking_error", "login_hint": "USER_EMAIL"}כדי לכפות מעבר לקישור OAuth.
- בודקים אם
יצירת חשבון:
- משתמשים בהצהרות
sub,email,nameו-pictureמתוך ה-JWT כדי ליצור רשומת משתמש חדשה.
- משתמשים בהצהרות
שליחת תשובה:
- יצירה והחזרה של טוקנים בתגובת JSON (HTTP
200 OK).
- יצירה והחזרה של טוקנים בתגובת JSON (HTTP
איך מקבלים את מזהה הלקוח ב-Google API
תצטרכו לספק את מזהה הלקוח של Google API במהלך תהליך ההרשמה לקישור החשבון. כדי לקבל את מזהה הלקוח של ה-API באמצעות הפרויקט שיצרתם במהלך השלבים של קישור OAuth. כדי לעשות זאת, מבצעים את השלבים הבאים:
- עוברים אל דף הלקוחות.
יוצרים פרויקט ב-Google APIs או בוחרים פרויקט קיים.
אם בפרויקט שלכם אין מזהה לקוח מסוג אפליקציית אינטרנט, לוחצים על יצירת לקוח כדי ליצור אחד. חשוב להוסיף את הדומיין של האתר לתיבה מקורות מורשים של JavaScript. כשמבצעים בדיקות מקומיות או פיתוח, צריך להוסיף את
http://localhostואתhttp://localhost:<port_number>לשדה מקורות JavaScript מורשים.
אימות ההטמעה
כדי לאמת את ההטמעה, אפשר להשתמש בכלי OAuth 2.0 Playground.
בכלי, מבצעים את השלבים הבאים:
- לוחצים על Configuration (הגדרה) כדי לפתוח את חלון ההגדרה של OAuth 2.0.
- בשדה OAuth flow (תהליך OAuth), בוחרים באפשרות Client-side (בצד הלקוח).
- בשדה OAuth Endpoints (נקודות קצה של OAuth), בוחרים באפשרות Custom (מותאם אישית).
- בשדות המתאימים, מציינים את נקודת הקצה של OAuth 2.0 ואת מזהה הלקוח שהקציתם ל-Google.
- בקטע Step 1, לא בוחרים אף היקף של Google. במקום זאת, משאירים את השדה הזה ריק או מקלידים היקף הרשאות שתקף לשרת (או מחרוזת שרירותית אם לא משתמשים בהיקפי הרשאות OAuth). בסיום, לוחצים על הרשאת ממשקי API.
- בקטעים שלב 2 ושלב 3, עוברים על תהליך ההרשאה באמצעות OAuth 2.0 ומוודאים שכל שלב פועל כמו שצריך.
כדי לאמת את ההטמעה, אפשר להשתמש בכלי Google Account Linking Demo.
בכלי, מבצעים את השלבים הבאים:
- לוחצים על הכפתור כניסה באמצעות חשבון Google.
- בוחרים את החשבון שרוצים לקשר.
- מזינים את מזהה השירות.
- אפשר להזין היקף אחד או יותר שרוצים לבקש גישה אליהם.
- לוחצים על התחלת ההדגמה.
- כשמופיעה הבקשה, מאשרים שרוצים להסכים לבקשת הקישור או לדחות אותה.
- מוודאים שמופנים לפלטפורמה שלכם.
