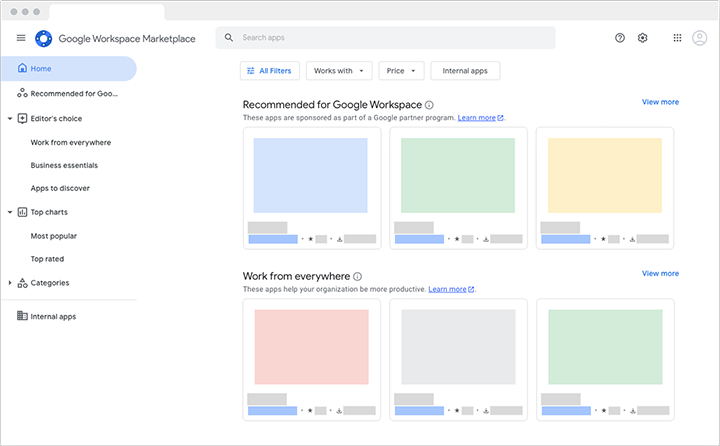
Share your solutions in the Google Workspace Marketplace.
The Google Workspace Marketplace makes it easy for users and administrators to find and install third-party applications that are integrated with Google Workspace.
You can publish Google Workspace add-ons, Editor add-ons, Google Chat apps, Classroom add-ons, Drive apps, and Web apps.
You can publish Google Workspace add-ons, Editor add-ons, Google Chat apps, Classroom add-ons, Drive apps, and Web apps.
Get started
Learn about how to publish your solutions to the Marketplace.
Learn about app reviews
Google reviews apps before they're published to make sure they meet Google's safety, content, and style guidelines.
Support
Get help, file a bug, or request a feature.