OAuth-based App Flip Linking (App Flip) allows your users to quickly link their accounts in your authentication system to their Google Accounts. If your app is installed on your user's phone when they initiate the account linking process, they are seamlessly flipped to your app to obtain user authorization.
This approach provides a faster linking process since the user does not have to re-enter their username and password to authenticate; instead, App Flip leverages the credentials from the user's account on your app. Once a user has linked their Google Account with your app, they can take advantage of any integrations that you have developed.
You can set up App Flip for both iOS and Android apps.
Requirements
To implement App Flip, you must fulfill the following requirements:
- You must have an Android or iOS app.
- You must own, manage and maintain an OAuth 2.0 server which supports the OAuth 2.0 authorization code flow.
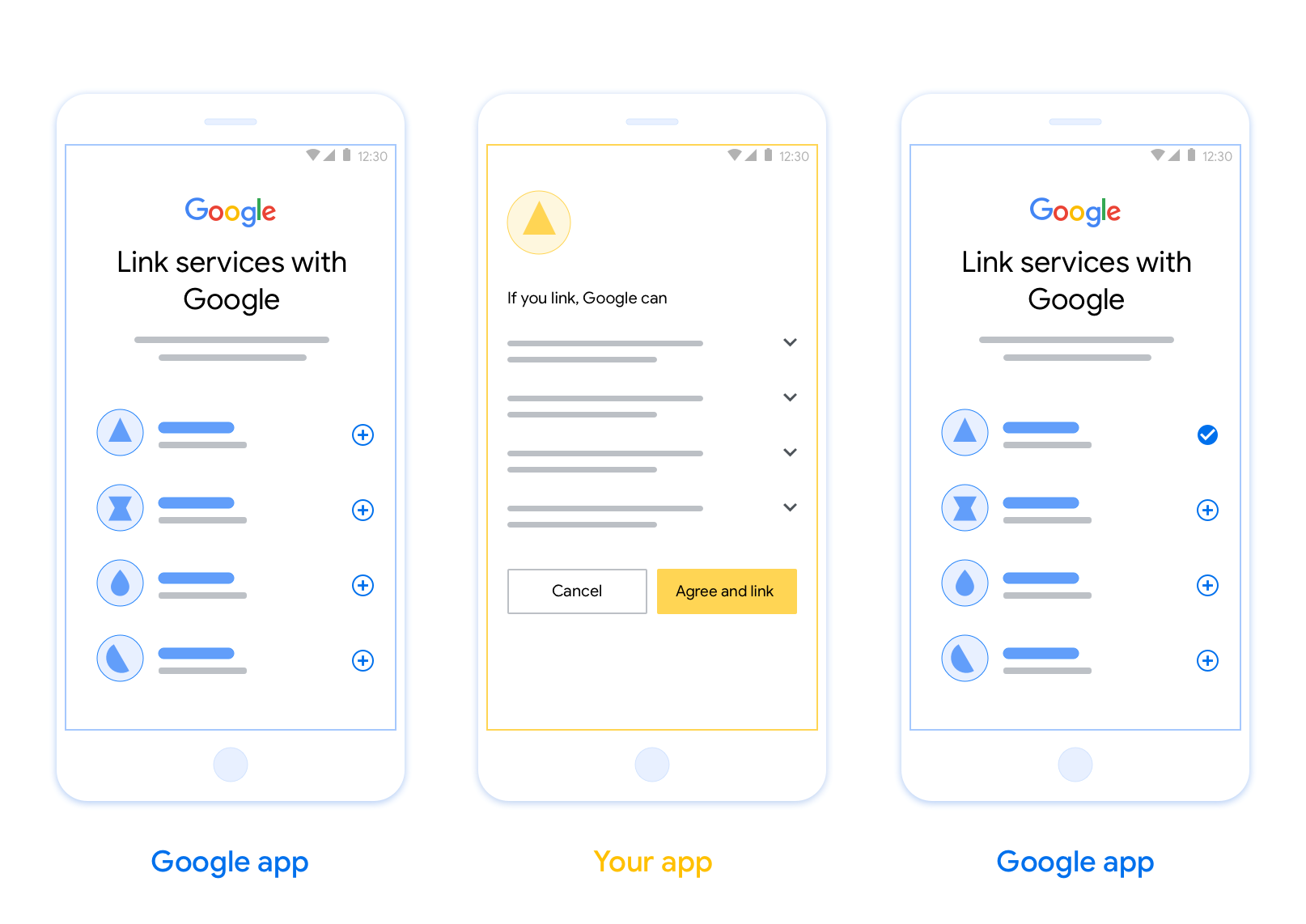
OAuth-based App Flip Flow
The following sequence diagram details the interaction between the User, Google App, Your App, and Your Authorization Server for App Flip.
Roles and responsibilities
The following table defines the roles and responsibilities of the actors in the App Flip flow.
| Actor / Component | GAL Role | Responsibilities |
|---|---|---|
| Google App / Server | OAuth Client | Initiates the linking process, triggers a deep link to your mobile app, exchanges the authorization code for tokens, and securely stores them to access your service's APIs. |
| Your App | Authorization Agent | Authenticates the user (typically using existing app credentials), obtains consent, and retrieves an authorization code from your server. |
| Your Authorization Server | Authorization Server | Validates authorization codes and refresh tokens, and issues access tokens to the Google Server. |
Design guidelines
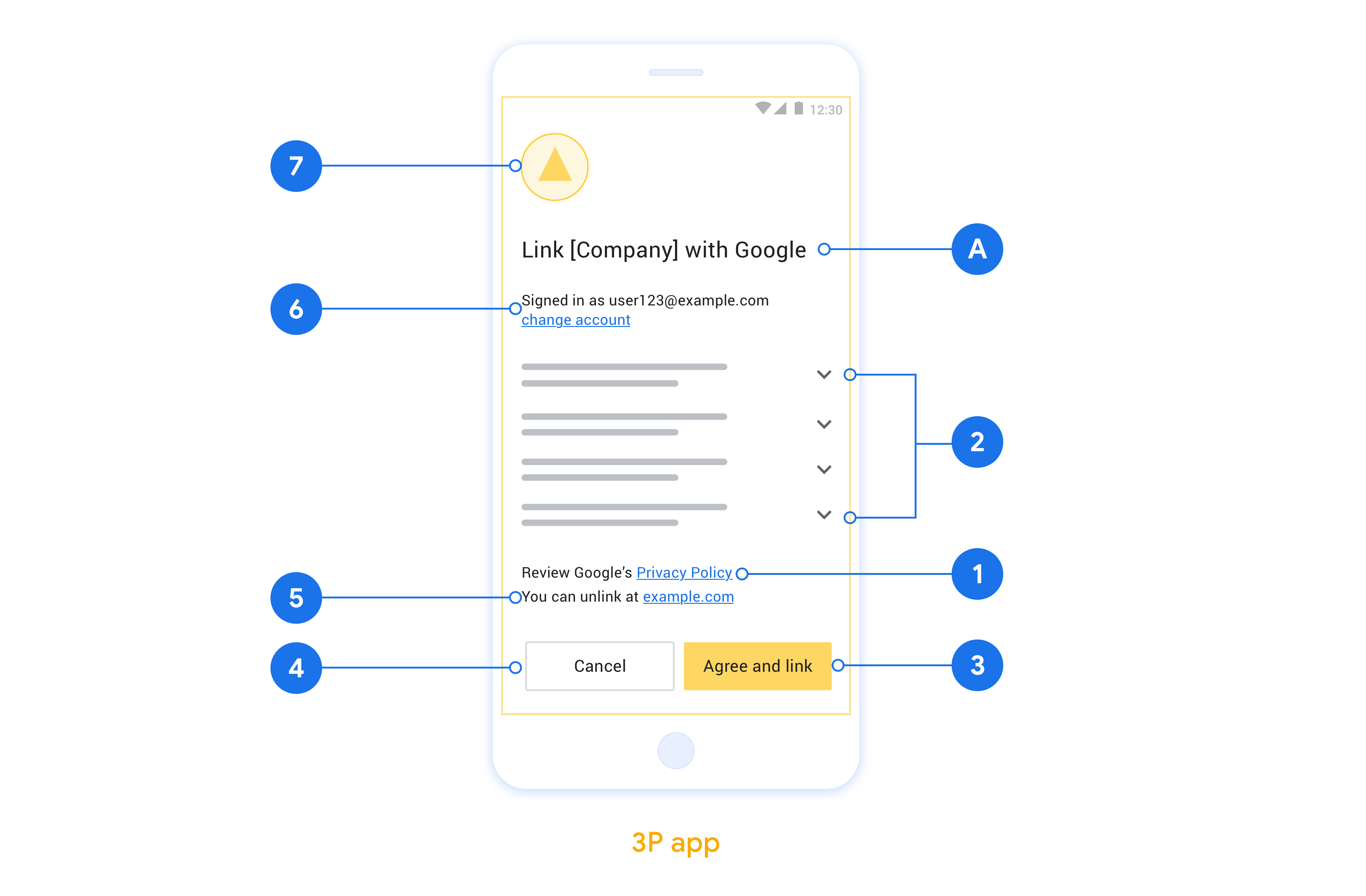
This section describes the design requirements and recommendations for the App Flip account linking consent screen. After Google calls your app, your app displays the consent screen to the user.
Requirements
- You must communicate that the user’s account is being linked to Google, not to a specific Google product, such as Google Home or Google Assistant.
Recommendations
We recommend that you do the following:
Display Google's Privacy Policy. Include a link to Google’s Privacy Policy on the consent screen.
Data to be shared. Use clear and concise language to tell the user what data of theirs Google requires and why.
Clear call-to-action. State a clear call-to-action on your consent screen, such as “Agree and link.” This is because users need to understand what data they're required to share with Google to link their accounts.
Ability to deny or cancel. Provide a way for users to go back, deny, or cancel, if they choose not to link.
Ability to unlink. Offer a mechanism for users to unlink, such as a URL to their account settings on your platform. Alternatively, you can include a link to Google Account where users can manage their linked account.
Ability to change user account. Suggest a method for users to switch their account(s). This is especially beneficial if users tend to have multiple accounts.
- If a user must close the consent screen to switch accounts, send a recoverable error to Google so the user can sign in to the desired account with OAuth linking and the implicit flow.
Include your logo. Display your company logo on the consent screen. Use your style guidelines to place your logo. If you wish to also display Google's logo, see Logos and trademarks.
Implementar a vinculação no app nos seus apps
Para implementar a vinculação no app, modifique o código de autorização do usuário no app para aceitar um link direto do Google.
Para oferecer suporte à vinculação no app no seu app Android, siga as instruções no guia de implementação do Android.
Para oferecer suporte à vinculação no app no seu app iOS, siga as instruções no guia de implementação do iOS.
Testar a vinculação no app
A vinculação no app pode ser simulada usando apps de exemplo e de teste antes que os apps de produção verificados e um servidor OAuth 2.0 funcional estejam disponíveis.
Durante a vinculação no app, um app do Google vai abrir seu app, que vai solicitar uma resposta de código de autorização do seu servidor OAuth 2.0. Na etapa final, a resposta é retornada ao app do Google.
Pré-requisitos
Para simular um app do Google e acionar a intent que inicia seu app, faça o download e instale a ferramenta de teste de vinculação no app para Android e iOS.
Faça o download e instale o exemplo de vinculação no app para Android e iOS para simular seu app e selecionar um tipo de resposta do OAuth 2.0.
Sequência de testes
- Abra a ferramenta de teste de vinculação no app.
- Pressione
Try Flip!para iniciar o app de exemplo de vinculação no app. - Selecione uma resposta nos botões de opção no app de exemplo.
- Pressione
Sendpara retornar uma resposta simulada do OAuth 2.0 para a ferramenta de teste. - Verifique as mensagens de registro da ferramenta de teste para ver um auth_code ou detalhes do erro.
Teste de produção
A vinculação no app pode ser testada na produção depois de concluir o registro e a implementação do servidor OAuth 2.0.
Recomendamos uma única Conta do Google e um endereço de e-mail específico da tarefa para testes automatizados.
O estado de vinculação das contas pode ser visualizado usando Contas vinculadas quando você faz login como titular da Conta do Google. As contas também podem ser desvinculadas entre testes repetidos.
Como opção, você pode implementar RISC para desvincular e notificar o Google sobre a mudança de forma programática.
