Les comptes sont associés à l'aide de flux implicites et code d'autorisation OAuth 2.0. Votre service doit être compatible avec les points de terminaison d'autorisation et d'échange de jetons conformes à OAuth 2.0.
Dans le flux implicite, Google ouvre votre point de terminaison d'autorisation dans le navigateur de l'utilisateur. Une fois la connexion établie, vous renvoyez un jeton d'accès de longue durée à Google. Ce jeton d'accès est désormais inclus dans chaque requête envoyée depuis Google.
Dans le flux de code d'autorisation, vous avez besoin de deux points de terminaison:
Le point de terminaison de l'autorisation, qui présente l'interface utilisateur de connexion aux utilisateurs qui ne sont pas encore connectés. Le point de terminaison de l'autorisation crée également un code d'autorisation de courte durée permettant d'enregistrer les utilisateurs et de donner leur consentement à l'accès demandé.
Le point de terminaison token Exchange, responsable de deux types de places de marché:
- Échange un code d'autorisation contre un jeton d'actualisation de longue durée et un jeton d'accès de courte durée. Cet échange se produit lorsque l'utilisateur suit le flux d'association de comptes.
- Échange un jeton d'actualisation de longue durée contre un jeton d'accès de courte durée. Cet échange se produit lorsque Google a besoin d'un nouveau jeton d'accès, car celui-ci a expiré.
Choisir un parcours OAuth 2.0
Bien que le flux implicite soit plus simple à mettre en œuvre, Google recommande que les jetons d'accès émis par le flux implicite n'expirent pas. En effet, l'utilisateur doit de nouveau associer son compte après l'expiration d'un jeton avec le parcours implicite. Si vous avez besoin d'un délai d'expiration du jeton pour des raisons de sécurité, nous vous recommandons vivement d'utiliser plutôt le flux de code d'autorisation.
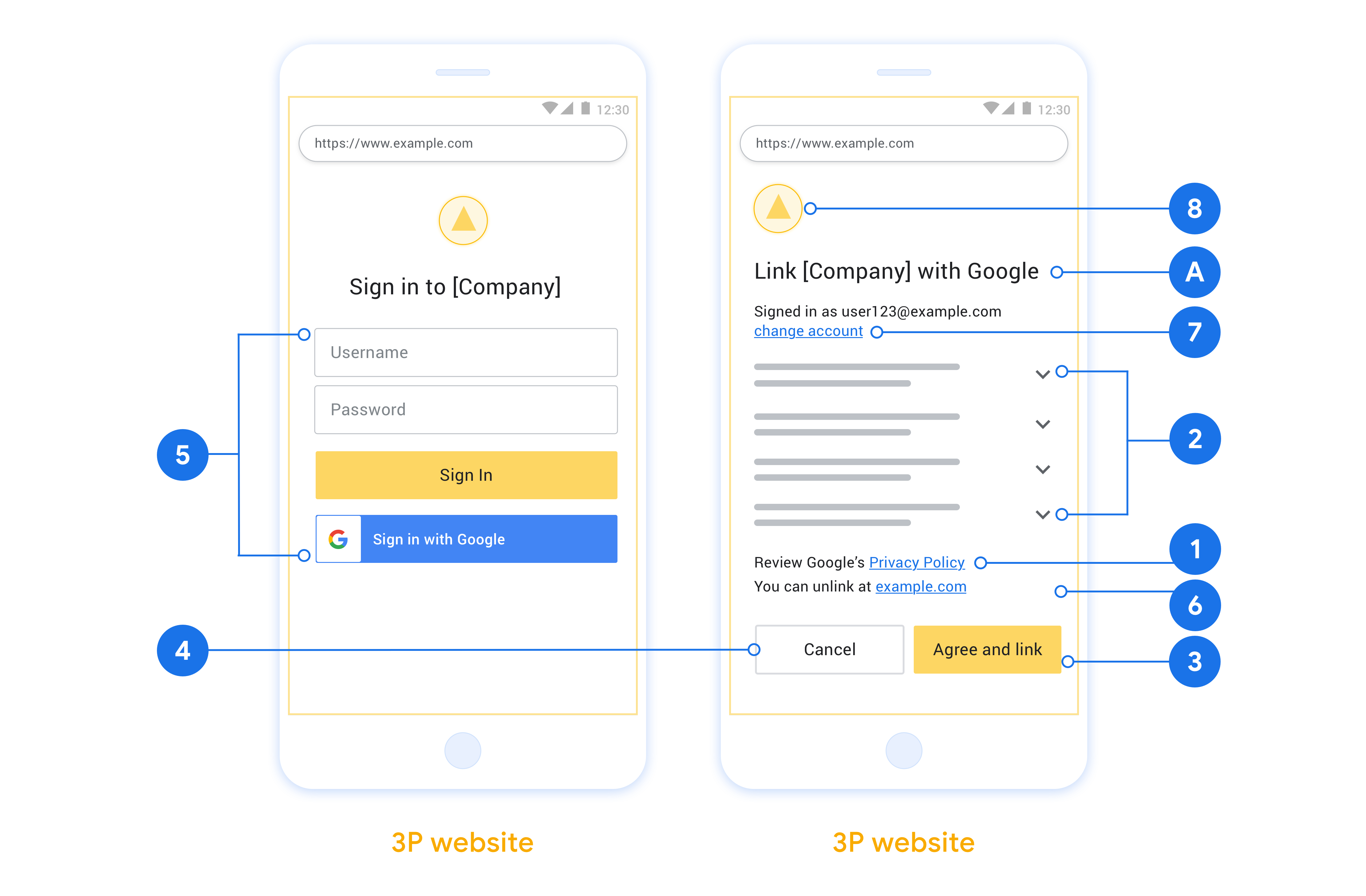
Consignes relatives à la conception
Cette section décrit les exigences et les recommandations de conception pour l'écran d'utilisateur que vous hébergez dans les flux d'association OAuth. Une fois l'application appelée par Google, votre plate-forme affiche l'écran de consentement pour l'association d'un compte Google à une page Google. L'utilisateur est redirigé vers l'application Google après avoir consenti à l'association des comptes.
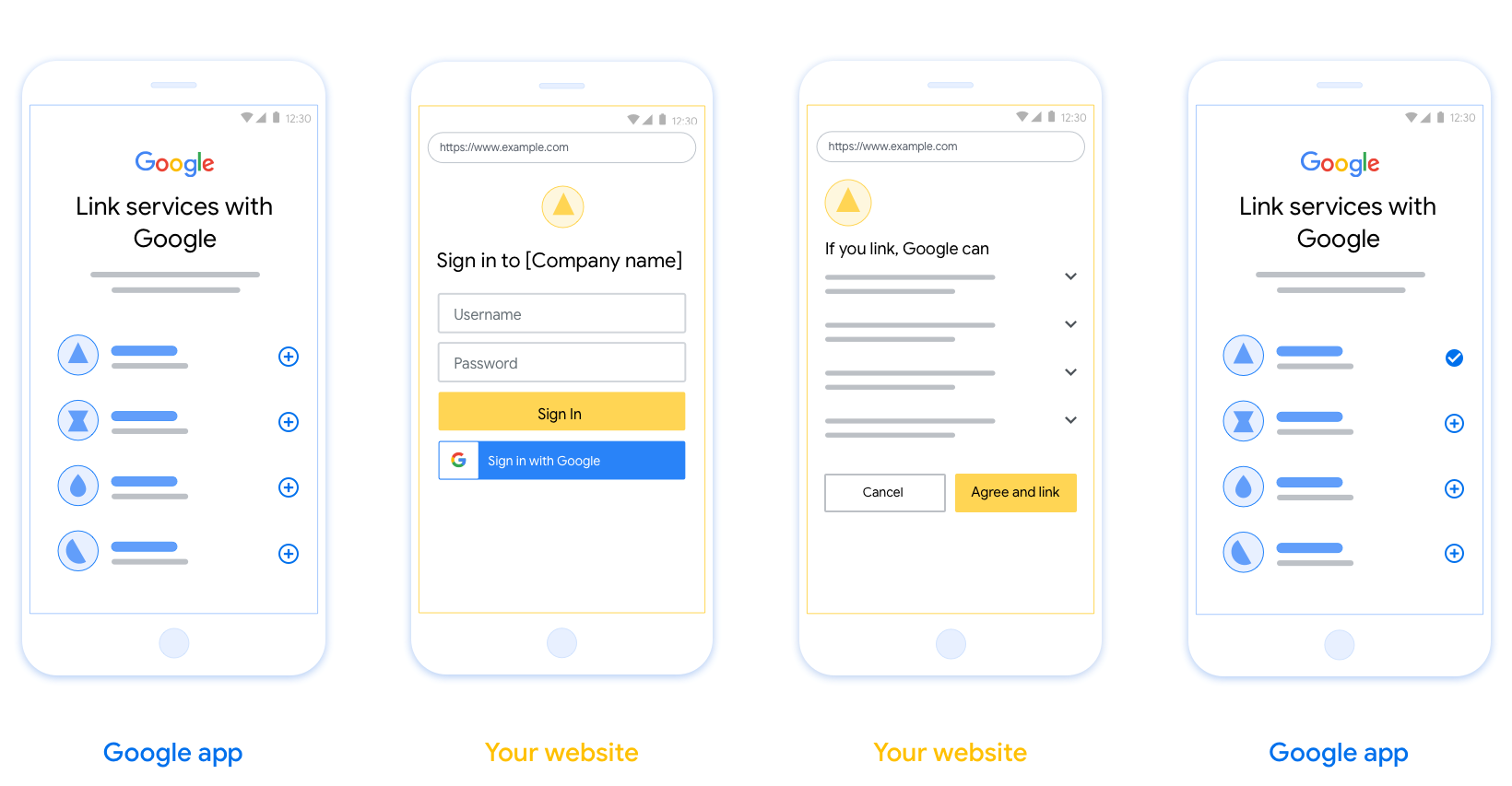
Conditions requises
- Vous devez indiquer que le compte de l'utilisateur sera associé à Google, et non à un produit Google spécifique tel que Google Home ou Assistant Google.
Recommandations
Nous vous recommandons d'effectuer les opérations suivantes :
Afficher les règles de confidentialité de Google. Incluez un lien vers les Règles de confidentialité de Google sur l'écran de consentement.
Données à partager. Utilisez un langage clair et concis pour indiquer à l'utilisateur les informations requises par Google et pourquoi.
Incitation à l'action claire. Indiquer une incitation à l'action claire sur votre écran de consentement, par exemple "Accepter et associer", car les utilisateurs doivent comprendre quelles données ils sont tenus de partager avec Google pour associer leurs comptes.
Possibilité d'annulation. Permettez aux utilisateurs de revenir en arrière ou d'annuler s'ils décident de ne pas créer de lien.
Processus de connexion clair. Assurez-vous que les utilisateurs disposent d'une méthode claire pour se connecter à leur compte Google, telle que des champs pour leur nom d'utilisateur et leur mot de passe, ou encore Se connecter avec Google.
Possibilité de dissocier. Proposez aux utilisateurs un mécanisme à dissocier, comme une URL renvoyant vers les paramètres de leur compte sur votre plate-forme. Vous pouvez également inclure un lien vers un compte Google dans lequel les utilisateurs peuvent gérer leur compte associé.
Possibilité de changer de compte utilisateur Suggérez une méthode permettant aux utilisateurs de changer de compte. C'est particulièrement intéressant si les utilisateurs ont généralement plusieurs comptes.
- Si un utilisateur doit fermer l'écran de consentement pour changer de compte, envoyez une erreur reproductible à Google afin qu'il puisse se connecter au compte souhaité avec l'association OAuth et le flux implicite.
Incluez votre logo. afficher le logo de votre entreprise sur l'écran de consentement ; Utilisez les consignes de style pour placer votre logo. Si vous souhaitez également afficher le logo Google, consultez Logos et marques.
Créer le projet
Pour créer votre projet afin d'utiliser l'association de comptes:
- Go to the Google API Console.
- Cliquez sur Créer un projet .
- Saisissez un nom ou acceptez la suggestion générée.
- Confirmez ou modifiez les champs restants.
- Cliquez sur Créer .
Pour afficher votre ID de projet:
- Go to the Google API Console.
- Trouvez votre projet dans le tableau de la page de destination. L'ID du projet apparaît dans la colonne ID .
Configurer votre écran de consentement OAuth
Le processus d'association de comptes Google comprend un écran de consentement qui indique aux utilisateurs l'application qui demande l'accès à leurs données, le type de données qu'ils demandent et les conditions qui s'appliquent. Vous devrez configurer votre écran de consentement OAuth avant de générer un ID client pour l'API Google.
- Ouvrez la page de l'écran de consentement OAuth dans la console des API Google.
- Si vous y êtes invité, sélectionnez le projet que vous venez de créer.
Sur la page "Écran de consentement OAuth", remplissez le formulaire et cliquez sur le bouton "Enregistrer".
Nom de l'application:nom de l'application demandant le consentement des utilisateurs. Le nom doit refléter précisément votre application et correspondre à celui que les utilisateurs voient ailleurs. Le nom de l'application s'affichera sur l'écran de consentement pour l'association de comptes.
Logo de l'application:image qui s'affiche sur l'écran de consentement pour aider les utilisateurs à reconnaître votre application. Le logo est affiché sur l'écran de consentement pour l'association de comptes et dans les paramètres du compte.
Adresse e-mail d'assistance:cette option permet aux utilisateurs de vous contacter pour vous poser des questions sur leur consentement.
Champs d'application pour les API Google:les champs d'application permettent à votre application d'accéder aux données Google privées de vos utilisateurs. Pour le cas d'utilisation de l'association de comptes Google, le champ d'application par défaut (adresse e-mail, profil, openid) est suffisant. Vous n'avez pas besoin d'ajouter de champs d'application sensibles. Il est généralement recommandé de demander des champs d'application de manière incrémentielle, au moment où l'accès est requis, plutôt qu'au départ. (en savoir plus).
Domaines autorisés:afin de vous protéger, vous et vos utilisateurs, Google n'autorise que les applications qui s'authentifient via OAuth à utiliser des domaines autorisés. Les liens de vos applications doivent être hébergés sur des domaines autorisés. (en savoir plus).
Lien vers la page d'accueil de l'application:page d'accueil de votre application. Doit être hébergé sur un domaine autorisé.
Lien vers les règles de confidentialité de l'application:s'affiche sur l'écran de consentement pour l'association de comptes Google. Doit être hébergé sur un domaine autorisé.
Lien vers les conditions d'utilisation de l'application (facultatif) : doit être hébergé sur un domaine autorisé.

Figure 1 : Écran de consentement pour l'association de comptes Google pour une application fictive, Tunery
Vérifiez l'état de validation de votre demande, puis cliquez sur le bouton "Envoyer pour validation". Pour en savoir plus, consultez les conditions de validation OAuth.
Implémenter votre serveur OAuth
To support the OAuth 2.0 implicit flow, your service makes an authorization endpoint available by HTTPS. This endpoint is responsible for authentication and obtaining consent from users for data access. The authorization endpoint presents a sign-in UI to your users that aren't already signed in and records consent to the requested access.
When a Google application needs to call one of your service's authorized APIs, Google uses this endpoint to get permission from your users to call these APIs on their behalf.
A typical OAuth 2.0 implicit flow session initiated by Google has the following flow:
- Google opens your authorization endpoint in the user's browser. The user signs in, if not signed in already, and grants Google permission to access their data with your API, if they haven't already granted permission.
- Your service creates an access token and returns it to Google. To do so, redirect the user's browser back to Google with the access token attached to the request.
- Google calls your service's APIs and attaches the access token with each request. Your service verifies that the access token grants Google authorization to access the API and then completes the API call.
Handle authorization requests
When a Google application needs to perform account linking via an OAuth 2.0 implicit flow, Google sends the user to your authorization endpoint with a request that includes the following parameters:
| Authorization endpoint parameters | |
|---|---|
client_id |
The client ID you assigned to Google. |
redirect_uri |
The URL to which you send the response to this request. |
state |
A bookkeeping value that is passed back to Google unchanged in the redirect URI. |
response_type |
The type of value to return in the response. For the OAuth 2.0 implicit
flow, the response type is always token. |
user_locale |
The Google Account language setting in RFC5646 format used to localize your content in the user's preferred language. |
For example, if your authorization endpoint is available at
https://myservice.example.com/auth, a request might look like the following:
GET https://myservice.example.com/auth?client_id=GOOGLE_CLIENT_ID&redirect_uri=REDIRECT_URI&state=STATE_STRING&response_type=token&user_locale=LOCALE
For your authorization endpoint to handle sign-in requests, do the following steps:
Verify the
client_idandredirect_urivalues to prevent granting access to unintended or misconfigured client apps:- Confirm that the
client_idmatches the client ID you assigned to Google. - Confirm that the URL specified by the
redirect_uriparameter has the following form:https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID https://oauth-redirect-sandbox.googleusercontent.com/r/YOUR_PROJECT_ID
- Confirm that the
Check if the user is signed in to your service. If the user isn't signed in, complete your service's sign-in or sign-up flow.
Generate an access token for Google to use to access your API. The access token can be any string value, but it must uniquely represent the user and the client the token is for and must not be guessable.
Send an HTTP response that redirects the user's browser to the URL specified by the
redirect_uriparameter. Include all of the following parameters in the URL fragment:access_token: The access token you just generatedtoken_type: The stringbearerstate: The unmodified state value from the original request
The following is an example of the resulting URL:
https://oauth-redirect.googleusercontent.com/r/YOUR_PROJECT_ID#access_token=ACCESS_TOKEN&token_type=bearer&state=STATE_STRING
Google's OAuth 2.0 redirect handler receives the access token and confirms
that the state value hasn't changed. After Google has obtained an
access token for your service, Google attaches the token to subsequent calls
to your service APIs.
Gérer les demandes d'informations sur les utilisateurs
Le point d'extrémité de userinfo est un OAuth 2.0 ressource protégée que les demandes de retour sur l'utilisateur liée. La mise en œuvre et l'hébergement du point de terminaison userinfo sont facultatifs, à l'exception des cas d'utilisation suivants :
- Lié Compte Se connecter avec Google One Tap.
- Abonnement Frictionless sur Android TV.
Une fois que le jeton d'accès a été récupéré avec succès à partir de votre point de terminaison de jeton, Google envoie une demande à votre point de terminaison userinfo pour récupérer les informations de profil de base sur l'utilisateur lié.
| en-têtes de demande de point de terminaison userinfo | |
|---|---|
Authorization header | Le jeton d'accès de type Bearer. |
Par exemple, si votre userinfo point final est disponible à https://myservice.example.com/userinfo , une demande pourrait ressembler à ce qui suit:
GET /userinfo HTTP/1.1 Host: myservice.example.com Authorization: Bearer ACCESS_TOKEN
Pour que votre point de terminaison userinfo gère les demandes, procédez comme suit :
- Extrayez le jeton d'accès de l'en-tête d'autorisation et renvoyez les informations pour l'utilisateur associé au jeton d'accès.
- Si le jeton d'accès est non valide, un retour HTTP 401 erreur non autorisée avec l' utilisation du
WWW-Authenticate- tête de réponse. Voici un exemple d'une réponse d'erreur userinfo:HTTP/1.1 401 Unauthorized WWW-Authenticate: error="invalid_token", error_description="The Access Token expired"
Si un 401 non autorisé, ou toute autre réponse d'erreur échoue est retournée au cours du processus de liaison, l'erreur sera non récupérable, le jeton Récupéré sera mis au rebut et l'utilisateur aura pour relancer le processus de liaison. Si le jeton d'accès est valide, le retour et réponse HTTP 200 avec l'objet JSON suivant dans le corps du protocole HTTPS réponse:
{ "sub": "USER_UUID", "email": "EMAIL_ADDRESS", "given_name": "FIRST_NAME", "family_name": "LAST_NAME", "name": "FULL_NAME", "picture": "PROFILE_PICTURE", }Si votre userinfo retourne point final une réponse de succès HTTP 200, le jeton récupéré et demandes sont enregistrées contre Google de l'utilisateur Compte.réponse du point de terminaison userinfo subUn identifiant unique qui identifie l'utilisateur dans votre système. emailAdresse e-mail de l'utilisateur. given_nameEn option: Prénom de l'utilisateur. family_nameFacultatif: Nom de l'utilisateur. nameFacultatif: Nom complet de l'utilisateur. pictureEn option: photo du profil de l'utilisateur.
Valider votre intégration
Vous pouvez valider votre implémentation en utilisant le Playground OAuth 2.0 outil.
Dans l'outil, procédez comme suit :
- Cliquez sur Configuration des pour ouvrir la fenêtre Configuration OAuth 2.0.
- Dans le champ d'écoulement OAuth, sélectionnez côté client.
- Dans le domaine Endpoints OAuth, sélectionnez Personnalisé.
- Spécifiez votre point de terminaison OAuth 2.0 et l'ID client que vous avez attribué à Google dans les champs correspondants.
- Dans la section Étape 1, ne sélectionnez pas de champs Google. Au lieu de cela, laissez ce champ vide ou saisissez une étendue valide pour votre serveur (ou une chaîne arbitraire si vous n'utilisez pas d'étendues OAuth). Lorsque vous avez terminé, cliquez sur Autoriser les API.
- Dans les étapes 2 et 3 sections, passez par le flux OAuth 2.0 et vérifiez que chaque étape fonctionne comme prévu.
Vous pouvez valider votre implémentation en utilisant le compte Google Linking Demo outil.
Dans l'outil, procédez comme suit :
- Cliquez sur le signe-avec le bouton Google.
- Choisissez le compte que vous souhaitez associer.
- Saisissez l'ID du service.
- Saisissez éventuellement une ou plusieurs étendues pour lesquelles vous demanderez l'accès.
- Cliquez sur Démarrer démo.
- Lorsque vous y êtes invité, confirmez que vous pouvez consentir et refuser la demande d'association.
- Confirmez que vous êtes redirigé vers votre plateforme.
